![Top Invicti alternatives in the market [2026] Top Invicti alternatives in the market [2026]](/blog/images/invicti-alternatives.webp)
If you’re searching for a robust application security testing solution in 2026, Invicti (formerly Netsparker) remains a dominant enterprise name. Known for its proprietary proof-based scanning technology and strong automation capabilities, Invicti continues to be a reliable DAST solution for organizations that require validated vulnerability findings at scale.
However, the application security landscape has evolved significantly.
With the rise of AI-generated code, microservices, API-first architectures, and continuous deployment pipelines, many teams are reassessing whether traditional scanning approaches are sufficient. Invicti’s expansion into Application Security Posture Management (ASPM) through acquisitions such as Kondukto has strengthened its governance layer, but it has also introduced additional operational complexity for some teams.
In 2026, organizations are looking for platforms that balance detection accuracy with agility, runtime intelligence, developer usability, and cost flexibility.
This blog explores the leading Invicti alternatives available today, covering both enterprise-grade platforms and next-generation AI-driven solutions. Whether your team prioritizes governance, autonomous testing, integrated remediation, or open-source flexibility, this comparison will help you choose a platform that strengthens your security culture rather than slowing down your development velocity.
Best Invicti alternatives TL;DR
| Software | Starting prices | Strengths | Best for |
|---|---|---|---|
| Beagle Security | $119 per month |
| Agile teams and modern applications with complex login flows |
| Rapid7 InsightAppSec | $175 per month |
| Organizations already using the Rapid7 Insight Platform |
| Tenable WAS | $7,434 per year |
| Large enterprises with a focus on comprehensive exposure management |
| Qualys WAS | Custom quote |
| Organizations already using the Qualys Cloud Platform |
| ZAP | Free |
| Individual developers, small teams, and budget-constrained projects |
| Burp Suite | Custom quote |
| Expert security professionals and dedicated penetration testers |
| Checkmarx | Custom quote |
| Organizations needing a full-spectrum, enterprise-grade AppSec solution |
| Veracode | Custom quote |
| Large enterprises with a long-term AppSec strategy |
| HCL AppScan | Custom quote; $295.87 per scan |
| Enterprises needing a flexible, comprehensive solution with on-premises options |
Best Invicti alternatives
1. Beagle Security
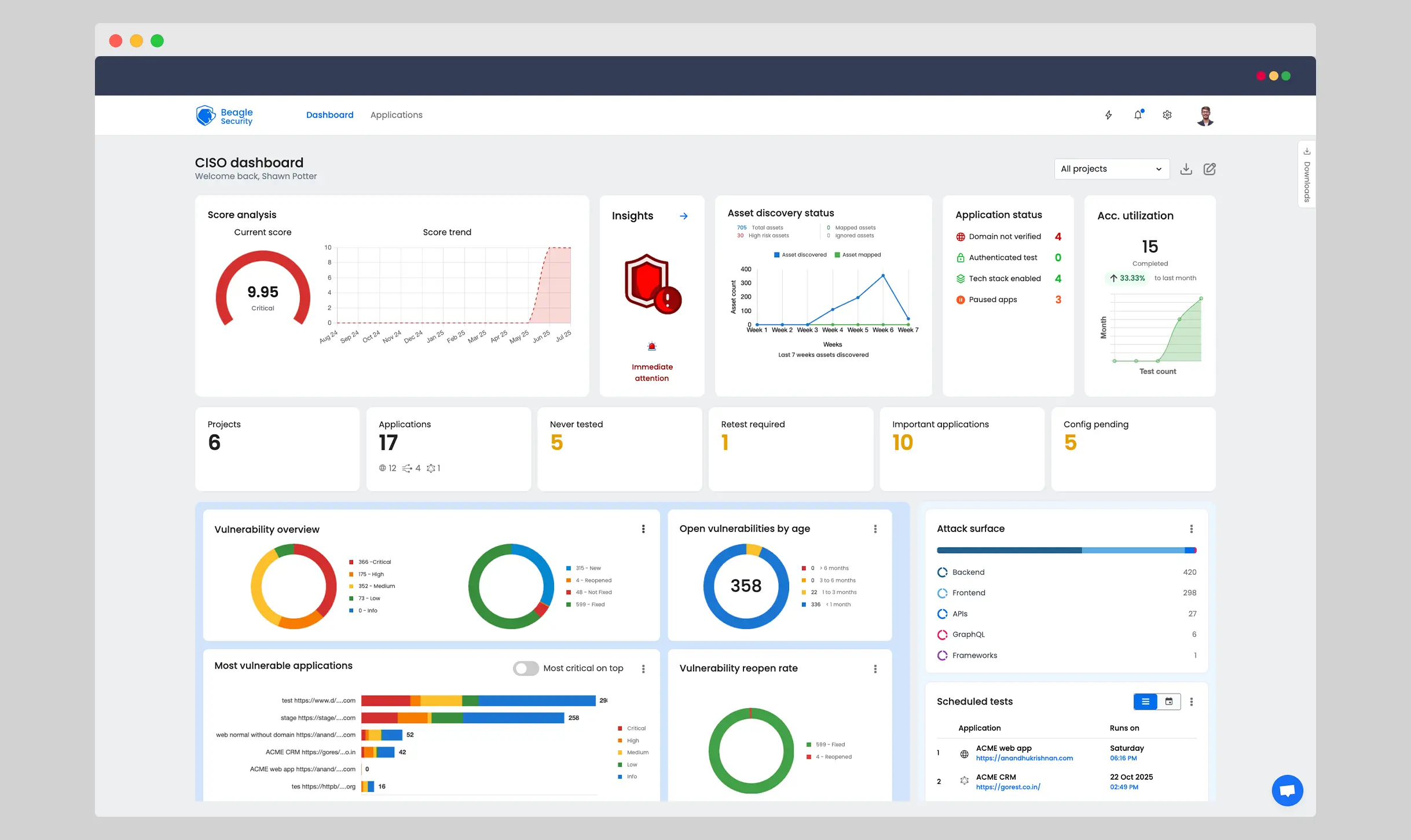
Beagle Security key overview:
AI-native DAST: Provides automated, AI-powered penetration testing.
Pricing: Starts at $1,188 per year, with transparent, concurrent test-based pricing.
Reviews: Highly rated on G2 (4.7/5) for its intuitive UI, AI-based engine, and developer-first reports.
Beagle Security represents a new generation of application security testing platforms. Rather than relying solely on predefined vulnerability signatures, it uses agentic AI to mimic the reasoning process of human penetration testers.
Its engine dynamically adapts to application behavior, identifies authentication endpoints, explores business logic, and tests multi-step workflows. This approach is particularly effective for detecting complex issues such as broken object-level authorization, privilege escalation, and logic flaws that traditional scanners often miss.
One of its strongest differentiators is Cosmog, a secure outbound-only private tunnel that allows organizations to scan internal staging and development environments without exposing inbound firewall rules.
Beagle Security key features:
Performs context-aware testing and handles complex login flows, including 2FA.
Simulates real-world attacker behavior to test business logic.
Offers contextual, developer-friendly reports with remediation guidance specific to the tech stack.
Integrates seamlessly with CI/CD pipelines.
Beagle Security pricing

Beagle Security uses a tiered pricing structure with plans starting at $1,188 per year. Enterprise plans begin at $8,500 annually for 5 concurrent tests. A 14-day free trial is available.
Beagle Security reviews
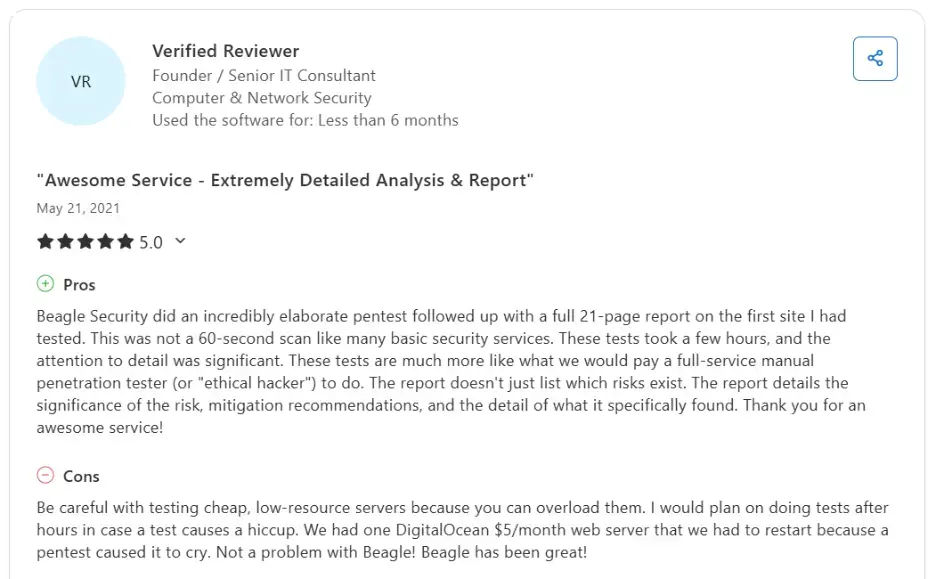
With a G2 rating of 4.7/5, users praise its intuitive UI, AI-based test engine, and developer-first reports.
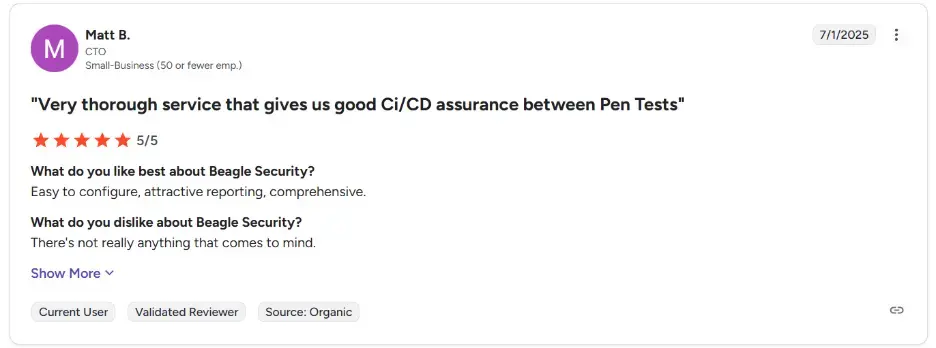
2. Rapid7 InsightAppSec
Rapid7 InsightAppSec key overview:
Integrated DAST/IAST: Combines DAST with lightweight IAST capabilities.
Pricing: Starts at $175 per month on a per-application basis.
Reviews: Rated 4.3/5 on G2, with users appreciating its integration with other Rapid7 tools.
Rapid7 InsightAppSec is part of the broader Rapid7 Command Platform, positioning application security within a unified exposure management ecosystem.
The platform includes a Universal Translator engine capable of interpreting modern protocols such as REST, JSON, and GraphQL. It also features Attack Replay, enabling developers to validate vulnerabilities and confirm fixes without requiring a full rescan.
The AI-powered Remediation Hub fuses exploit intelligence with asset criticality, providing plain-language guidance that helps prioritize remediation based on real-world risk.
Rapid7 key features:
DAST with lightweight IAST via agents
Attack Replay for developer validation
Scan gating within CI/CD pipelines
ServiceNow-certified integrations
Hybrid scan engine deployment options
Rapid7 InsightAppSec pricing
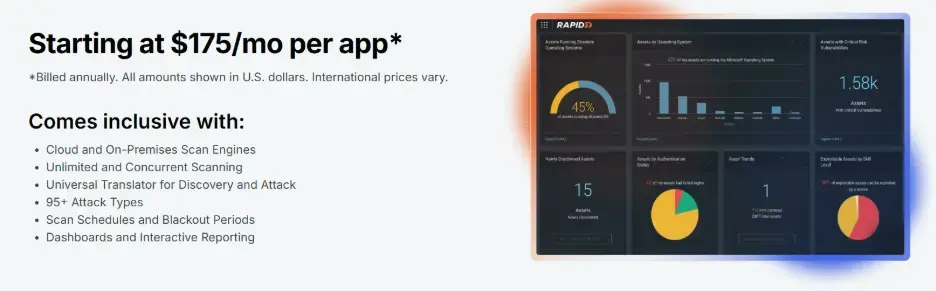
Rapid7 pricing starts at $175 per month for a single application, using a per-application pricing model. This can be costly for organizations with many applications. A 30-day free trial is available.
Rapid7 InsightAppSec reviews
Rated 4.3/5 on G2, users appreciate its integration with other Rapid7 tools. Common complaints include a steep learning curve and performance issues.
3. Tenable WAS
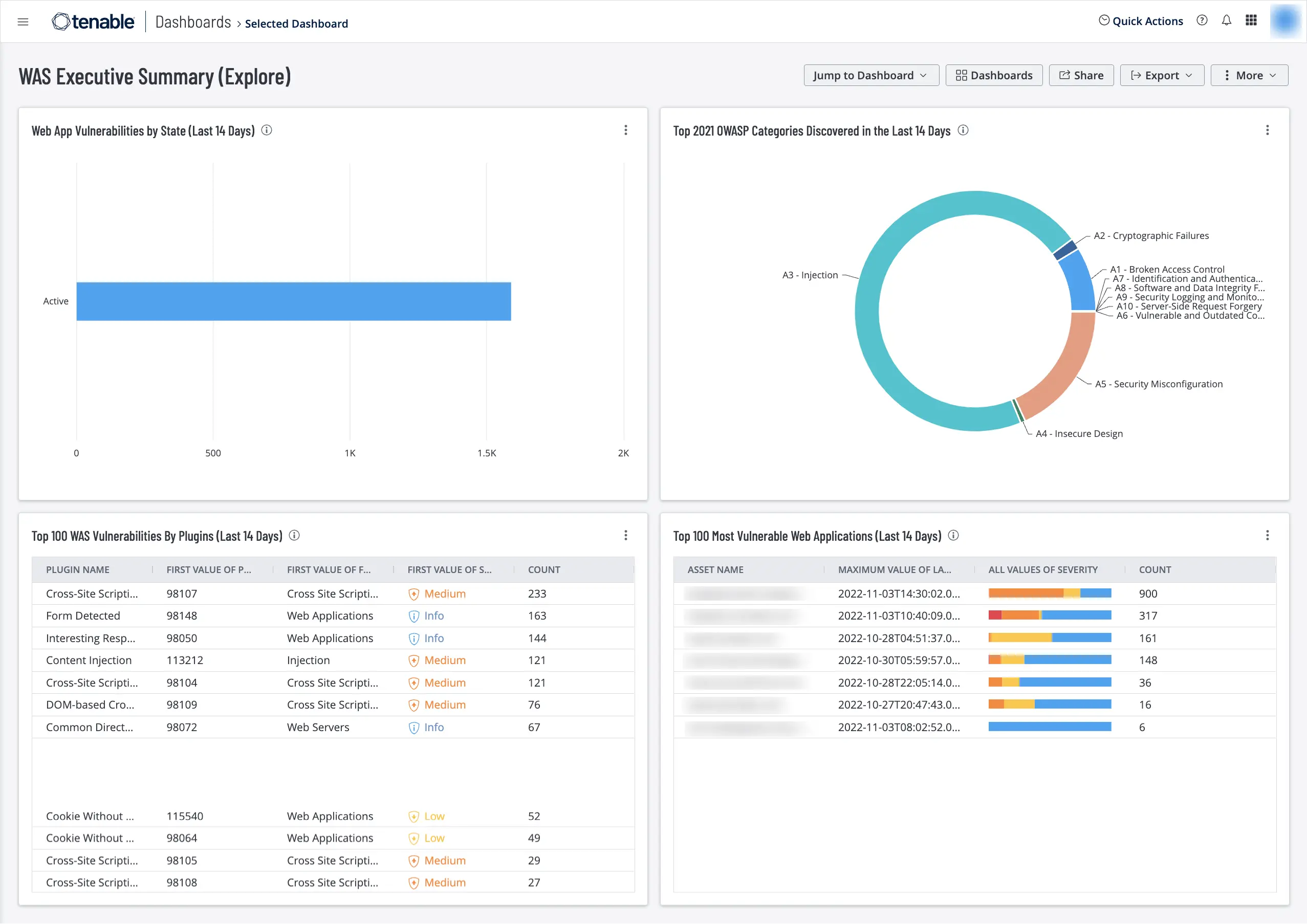
Tenable WAS key overview:
Risk-based approach: Prioritizes vulnerabilities based on exploitability.
Pricing: Starts at $7,434 per year for 5 FQDNs.
Reviews: Praised on G2 (4.5/5) for its comprehensive vulnerability coverage and intuitive dashboards.
Tenable Web Application Scanning operates within the Tenable One Exposure Management Platform. It emphasizes comprehensive vulnerability detection and predictive risk scoring.
Recent enhancements include GraphQL and SOAP API support, as well as AI Exposure modules that help organizations monitor AI assets and prevent data leakage.
Tenable WAS key features:
Extensive plugin library with high signature coverage
Predictive Vulnerability Priority Rating System.
AI asset governance
Scan-by-tag automation
Tenable WAS pricing
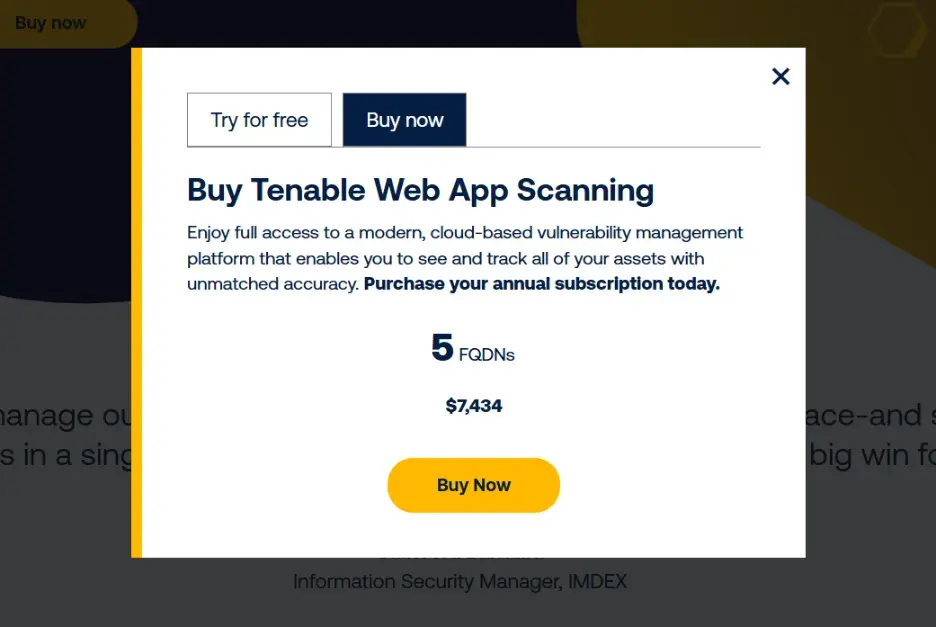
Tenable WAS pricing starts at $7,434 per year for 5 FQDNs. A 30-day free trial is available, but it is often limited in functionality.
Tenable WAS reviews
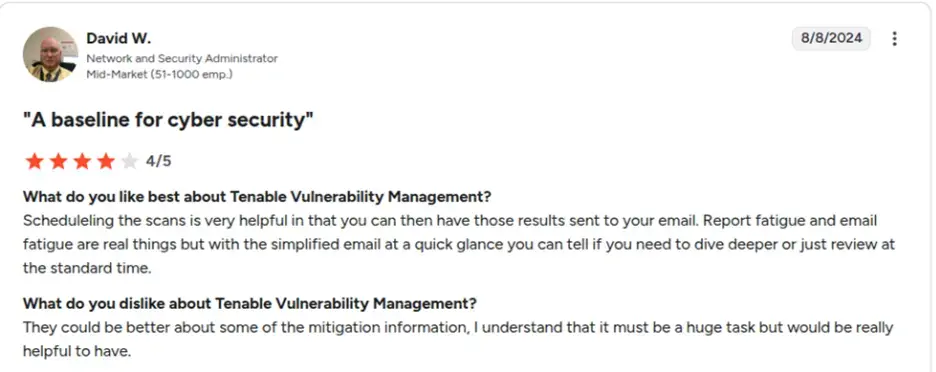
With a G2 rating of 4.5/5, users praise its comprehensive vulnerability coverage and intuitive dashboards. Some reviewers mention that the initial setup can be complex, and scan times can be lengthy.
4. Qualys WAS

Qualys WAS key overview:
All-in-one platform: Part of the Qualys VMDR platform, with integrated vulnerability management.
Pricing: Custom quote; based on a per-target cost.
Reviews: Recognized on G2 (4.3/5) for strong asset visibility and integrated vulnerability management.
Part of the all-in-one Qualys VMDR platform, this solution helps organizations discover web assets and continuously monitor them for vulnerabilities.
Qualys WAS provides DAST and includes a TruRisk™ prioritization engine. It offers CI/CD integrations and reports that meet compliance requirements. Users have noted a steep learning curve and higher false positive rates compared to some other tools.
Qualys WAS key features:
Provides DAST and includes a TruRisk™ prioritization engine.
Offers CI/CD integrations.
Provides reports that meet compliance requirements.
Integrated vulnerability management and asset discovery.
DAST integrated with patch management
OpenAPI drift detection
Deep asset discovery
Compliance reporting
Qualys WAS pricing
Pricing is based on a custom quote and a per-target cost basis. A 30-day free trial is available.
Qualys WAS reviews
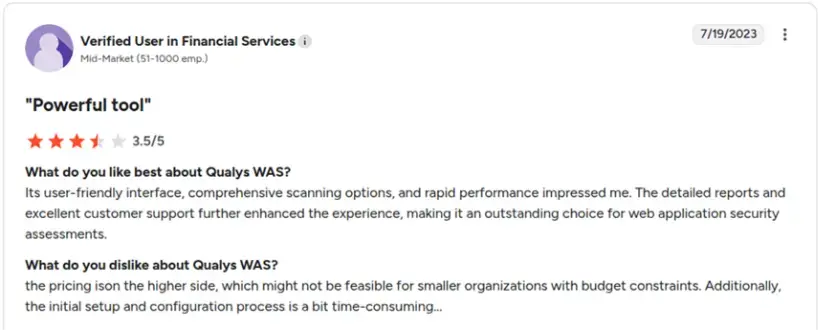
With a G2 rating of 4.3/5, the platform is recognized for its strong asset visibility and integrated vulnerability management.
5. ZAP by Checkmarx
ZAP by Checkmarx key overview:
Open-source & free: A free, community-driven open-source tool.
Pricing: Free.
Reviews: Praised on G2 (4.7/5) for its accessibility and effectiveness, with a strong community.
ZAP remains one of the most widely used open-source DAST tools in the world. Originally designed as a community project under the Open Web Application Security Project, ZAP has matured significantly over the years and now benefits from broader ecosystem support, including backing and contributions from Checkmarx.
In 2026, ZAP continues to be an attractive choice for developers, startups, educational institutions, and budget-conscious teams that need automated security scanning without licensing costs. It provides both automated and manual testing capabilities, allowing teams to run baseline scans as well as perform deeper exploratory testing.
ZAP’s automated scanner detects common web vulnerabilities such as cross-site scripting, SQL injection, insecure headers, and misconfigurations. It also supports API security testing, including REST endpoints and OpenAPI definitions. With scripting extensions and add-ons, teams can expand ZAP’s capabilities to suit their specific workflows.
However, as with most open-source tools, ZAP requires hands-on configuration and expertise. False positive management is manual, and complex authentication flows often require custom scripting. For organizations without dedicated security engineers, operational overhead can increase quickly.
ZAP by Checkmarx key features:
Automated scanner tests for common vulnerabilities like XSS and SQL injection.
Provides OWASP Top 10 reports.
Accessible to users of all skill levels.
Supports API security testing, scheduled testing, and SSO.
ZAP by Checkmarx pricing
ZAP is a free, open-source tool.
ZAP by Checkmarx reviews
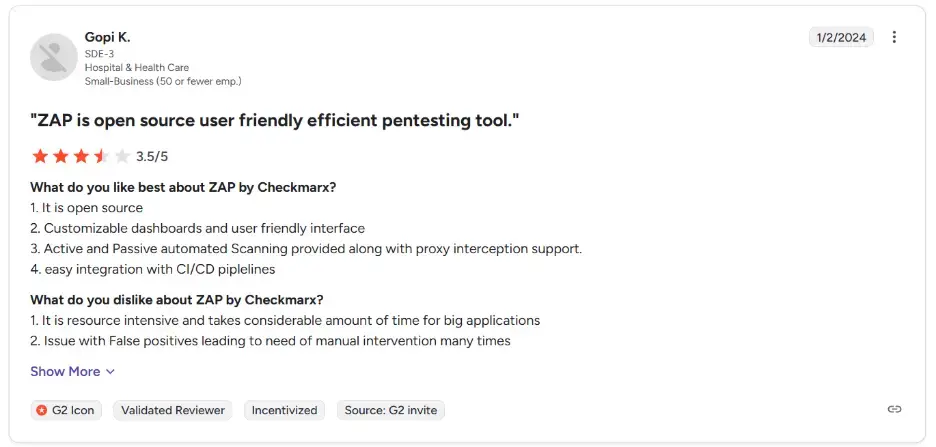
ZAP has a G2 rating of 4.7/5. It is praised for its accessibility and effectiveness, though the initial setup has a learning curve.
6. Burp Suite
Burp Suite key overview:
Manual PT: Primarily used for manual penetration testing with DAST capabilities.
Pricing: Custom quote; no free trial.
Reviews: Highly rated on G2 (4.8/5) for its powerful features for manual testing, but noted for a steep learning curve.
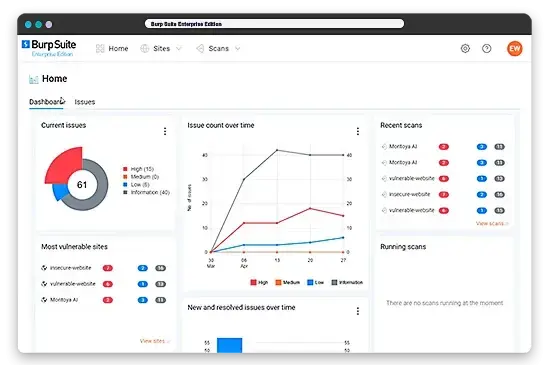
Burp Suite is widely regarded as the gold standard for manual web application security testing. Developed by PortSwigger, it offers a powerful interception proxy that allows security professionals to analyze and manipulate HTTP traffic in real time.
While Burp Suite includes automated scanning capabilities in its Professional and Enterprise editions, its primary strength lies in manual testing depth. Security engineers can craft custom payloads, explore application logic, test edge cases, and validate complex attack scenarios in ways that fully automated DAST tools cannot replicate.
The Enterprise edition adds scalable scanning and CI/CD integration, enabling organizations to automate routine checks while maintaining access to advanced manual testing capabilities.
Burp Suite supports API testing, single-page application scanning, and authentication workflows. However, the platform is resource-intensive and requires significant expertise to fully leverage its capabilities.
Burp Suite key features:
Primarily used for manual penetration testing, but also offers DAST capabilities.
Allows for scheduled testing, CI/CD integrations, and scanning of SPAs.
Provides PCI DSS and OWASP Top 10 reports.
Supports SSO and API security testing.
Burp Suite pricing
Burp Suite pricing is typically custom and depends on the specific edition (e.g., Community, Professional, Enterprise) and the features required.
For larger organizations and enterprise-grade scanning, it can be a significant investment, often requiring dedicated security personnel to maximize its capabilities.
Burp Suite reviews
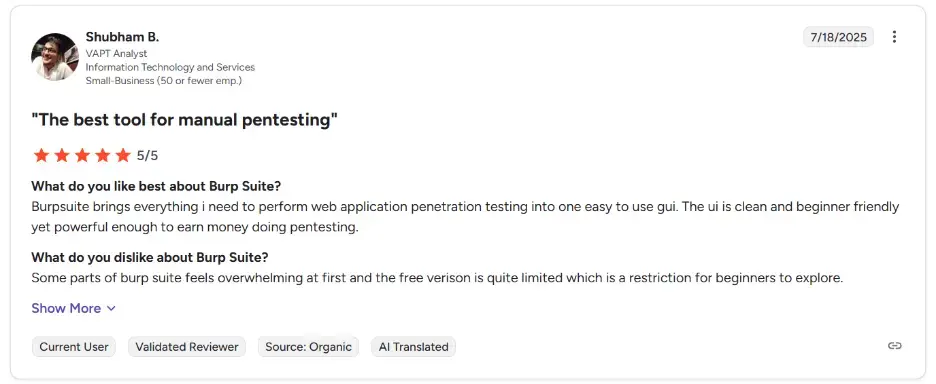
With a G2 rating of 4.8/5, users appreciate its powerful features for detailed manual testing and its flexibility for advanced security professionals. However, customers commonly complain about the steep learning curve required to master the platform and that it can be resource-intensive, particularly for large-scale or continuous scanning.
7. Checkmarx
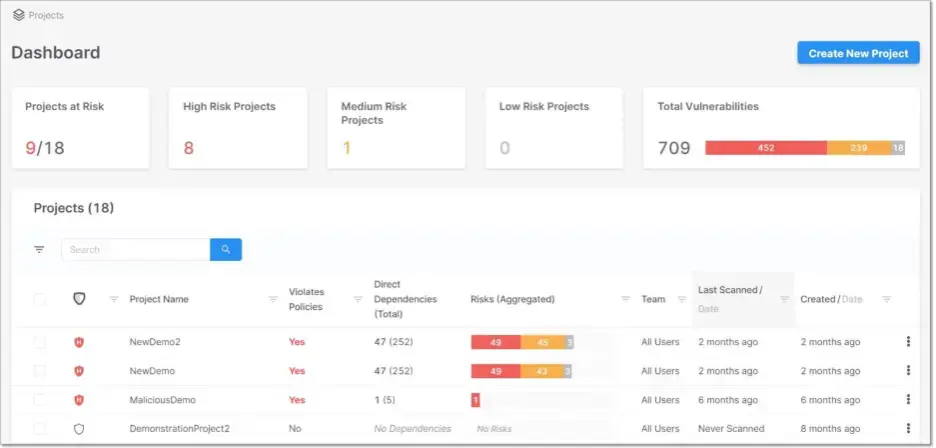
Checkmarx key overview:
Comprehensive suite: Offers SAST, DAST, and SCA solutions.
Pricing: Custom quote; not publicly available.
Reviews: The ZAP tool (a part of the Checkmarx family) has a G2 rating of 4.7/5, with users appreciating its effectiveness.
Checkmarx provides a comprehensive application security testing platform focused heavily on source code analysis and prevention across the software development lifecycle.
Its SAST engine scans source code early in development to detect vulnerabilities such as injection flaws, insecure cryptographic usage, and logic errors. The platform offers deep language support, enabling organizations to secure diverse technology stacks.
Checkmarx also includes Software Composition Analysis capabilities to identify vulnerabilities and license compliance issues in open-source dependencies. In an era where software supply chain risk is increasing, this feature plays a critical role in preventing malicious package usage.
The platform integrates with popular development environments such as GitHub, GitLab, Bitbucket, and major IDEs. Developers can receive vulnerability feedback directly within their workflow, supporting shift-left security initiatives.
While Checkmarx provides robust capabilities, enterprise deployments may require tuning to reduce false positives and optimize performance for large codebases.
Checkmarx key features:
A comprehensive suite of security solutions, including SAST, DAST, and SCA.
It integrates with popular development tools like GitHub, Bitbucket, and GitLab.
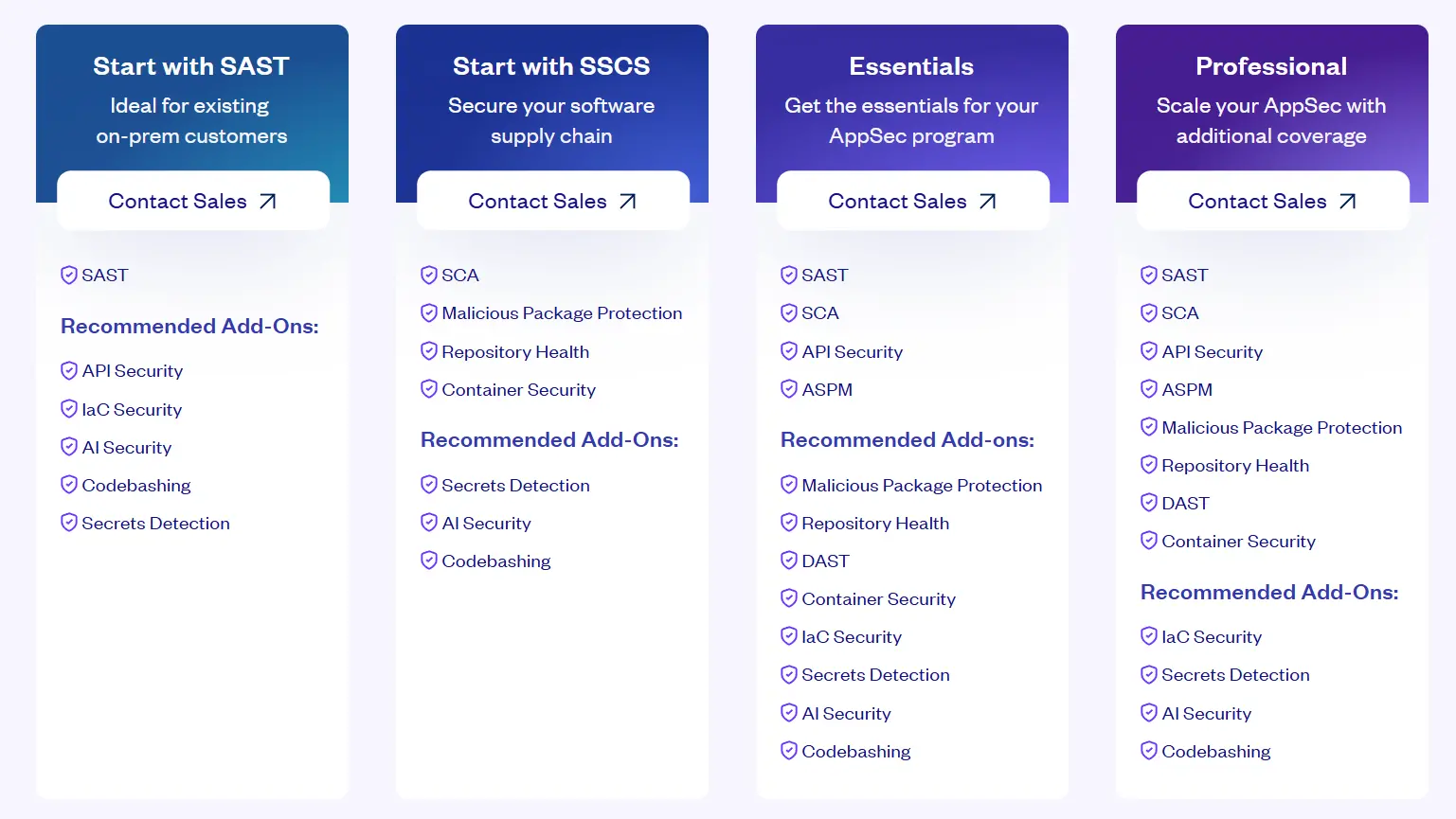
Checkmarx pricing
Checkmarx offers a structured set of plans designed to meet varying levels of application security maturity.
Their pricing is not publicly disclosed, and all tiers require direct contact with the sales team for a customized quote based on your needs. They offer plans, namely “Start with SAST”, “Start with SSCS”, “Essentials”, and “Professional”.
Details of what is offered in each plan can be found below:
Checkmarx reviews
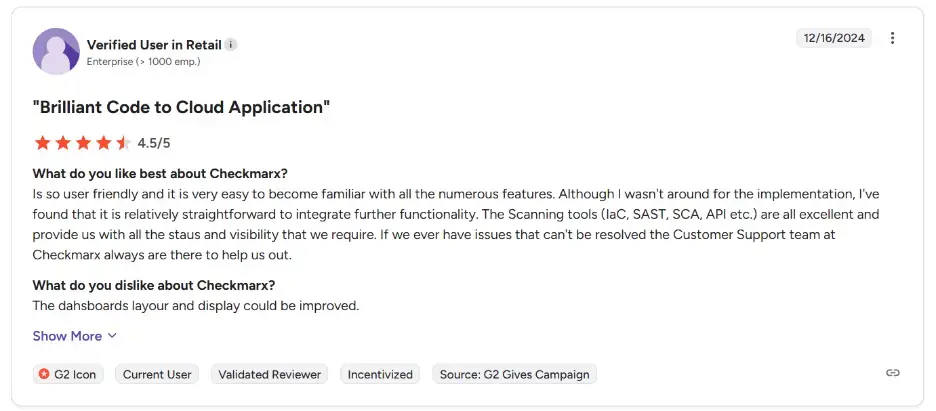
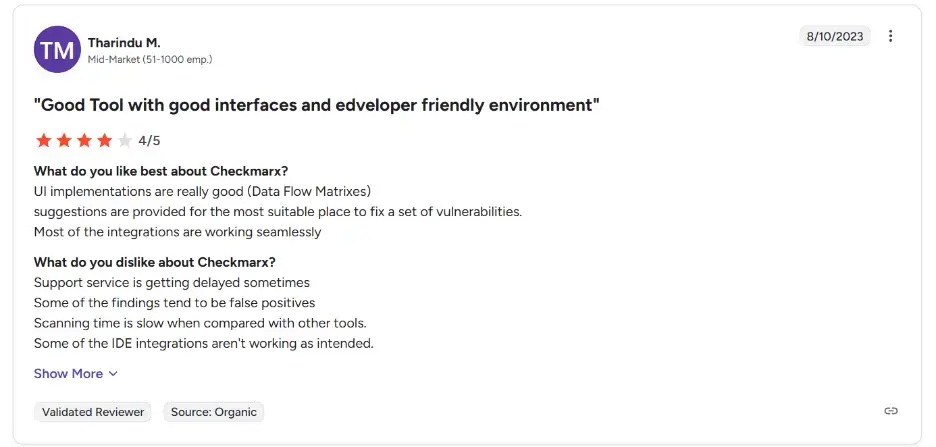
Checkmarx is praised for its user-friendly UI and helpful vulnerability fix suggestions. However, users report delays in support, occasional false positives, slower scan times, and some IDE integration issues. It is rated 4.2 on G2.
8. Veracode
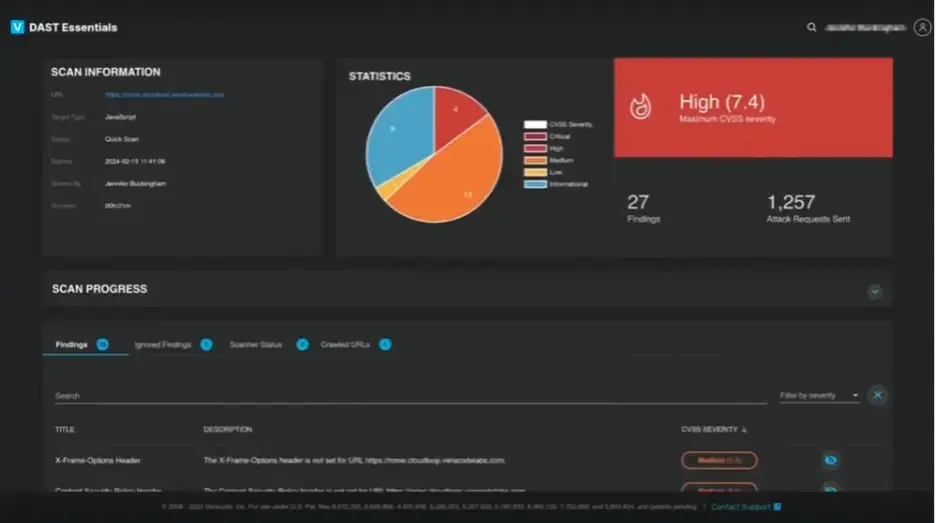
Veracode key overview:
Full-Spectrum Platform: Offers SAST, DAST, IAST, SCA, and IaC security.
Pricing: Custom contract; not publicly listed.
Reviews: Praised for its comprehensive scanning and support, with a G2 rating of 3.7/5.
Veracode is a long-standing enterprise AppSec platform offering SAST, DAST, IAST, SCA, and Infrastructure as Code security.
One of its distinguishing features is binary analysis. Unlike traditional SAST tools that require source code access, Veracode can scan compiled binaries, making it particularly useful for third-party applications or scenarios where source code cannot be shared externally.
The platform emphasizes compliance and governance workflows. Organizations operating under regulatory frameworks such as PCI DSS, HIPAA, ISO 27001, and SOC 2 benefit from structured reporting and policy enforcement capabilities.
Veracode also provides AI-generated code fix suggestions, accelerating remediation cycles for development teams.
However, onboarding can be complex, and licensing structures are not publicly disclosed, requiring direct consultation with sales teams.
Veracode key features:
A comprehensive platform offering SAST, DAST, IAST, SCA, and IaC security.
Integrates with popular IDEs and CI/CD pipelines.
Provides AI-generated code fix suggestions.
Uses a patented binary code analysis method.
Veracode pricing
Veracode’s pricing is not published publicly. Veracode has a tiered pricing structure based on the number of applications and the number of scans performed.
The only way to understand what their services are going to cost you is by scheduling a demo and talking to one of their sales reps.
Veracode reviews
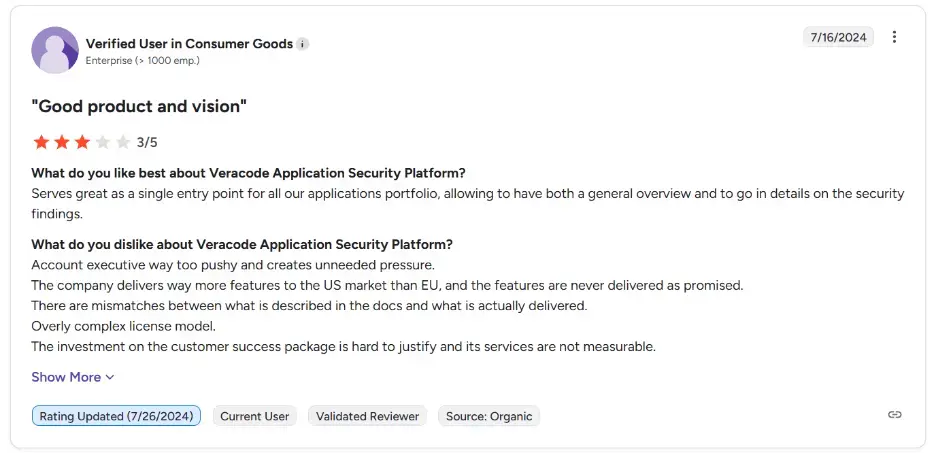
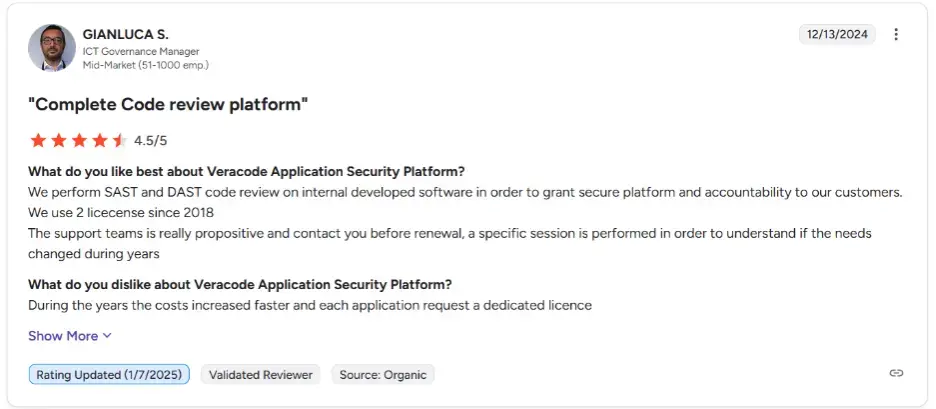
With a G2 rating of 3.7/5, Veracode is praised for its comprehensive scanning capabilities and committed support. Some users find it complex to implement and note that the pricing model can be costly.
9. HCL AppScan
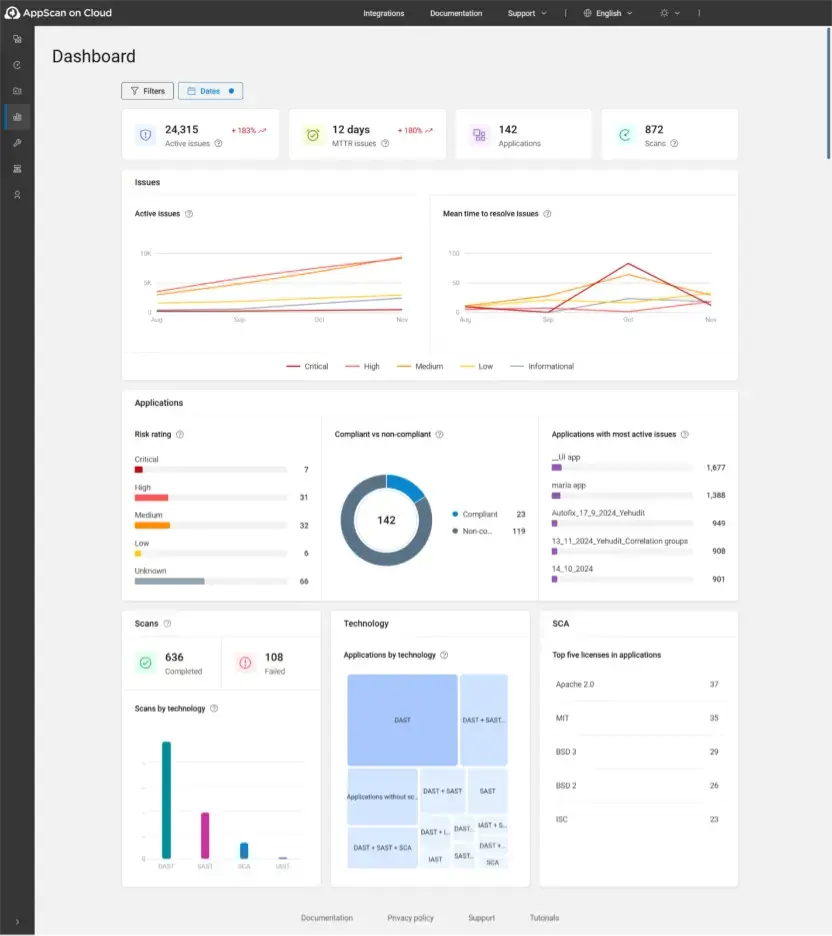
HCL AppScan key overview:
Full suite: Offers SAST, DAST, IAST, SCA, and API testing.
Pricing: Starts at $295.87 per scan for the cloud version.
Reviews: Rated 4.1/5 on G2 for its ease of use and accurate scan results.
HCL AppScan delivers a comprehensive application security solution suitable for enterprises requiring flexible deployment models.
The platform supports both on-premise and cloud-based scanning, making it attractive for organizations with strict data residency or compliance requirements.
AppScan incorporates AI-driven analysis to reduce false positives and prioritize risk more effectively. Centralized dashboards provide visibility across development portfolios, and actionable reporting supports faster remediation.
HCL AppScan key features:
Offers a full suite of technologies, including SAST, DAST, IAST, SCA, and API testing.
Uses AI-driven accuracy to reduce false positives and prioritize risks.
Provides centralized dashboards and actionable reporting with fix recommendations.
Integrates with developer workflows.
HCL AppScan pricing
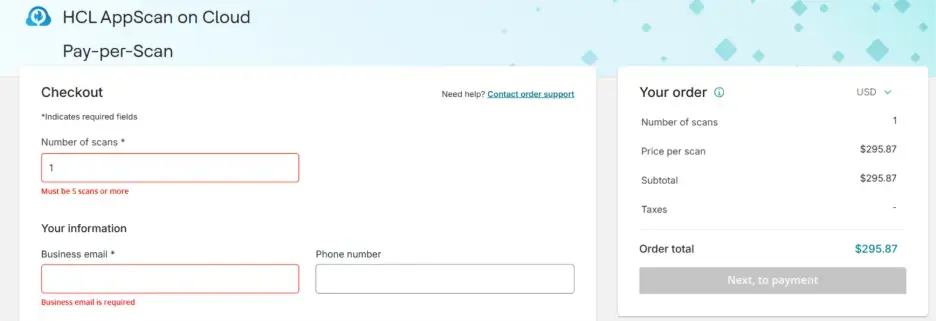
Pricing of HCL AppScan is typically custom quoted, but a pay-per-scan option for the cloud version is available, starting at $295.87 per scan (minimum of five scans). A 30-day free trial is available.
HCL AppScan reviews
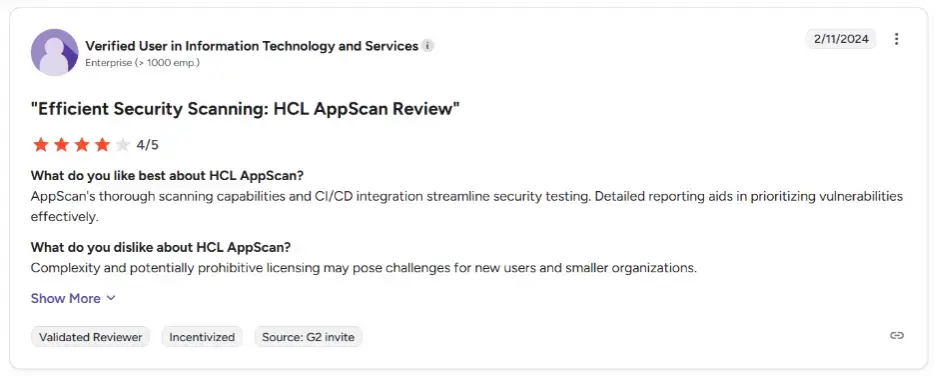
HCL AppScan has a G2 rating of 4.1/5. Users appreciate its accurate scan results, though some report a difficult installation process and a lack of documentation.
Key factors to consider when choosing an Invicti alternative
Pricing model
Pricing structures in 2026 vary widely across vendors, and the differences can significantly impact the long-term total cost of ownership.
Some platforms follow per-application or per-FQDN licensing models. Others use concurrent testing limits, usage-based quotas, asset-based pricing, or fully customized enterprise contracts. While entry-level pricing may appear competitive, costs can scale rapidly as your application portfolio grows or as new microservices and APIs are introduced.
When evaluating alternatives, consider:
How pricing scales with additional applications, subdomains, and APIs
Whether ephemeral environments, such as staging or short-lived deployments, are counted
Whether target-based pricing creates long-term lock-in
If the platform offers predictable budgeting as your organization expands
A transparent pricing model that aligns with your growth trajectory can prevent unexpected budget strain as your security program matures.
Ease of use and integration
In modern DevSecOps environments, security tools must operate at the speed of development. A powerful scanner that slows down pipelines or requires heavy configuration will struggle to gain adoption among engineering teams.
Look for platforms that provide:
Intuitive dashboards with minimal onboarding friction
Native integrations with CI/CD tools such as GitHub Actions, GitLab, Jenkins, and Azure DevOps
IDE integrations that deliver feedback directly within the developer workflow
Automated ticket creation in Jira, ServiceNow, or similar systems
Clear remediation guidance mapped to specific frameworks and technologies
Ease of integration is often the difference between a tool that is technically capable and one that is actually used consistently across teams.
Advanced capabilities and AI maturity
Modern applications are API-first, cloud-native, and frequently built using microservices and single-page frameworks. Traditional rule-based scanners may struggle with dynamic authentication flows, stateful sessions, and business logic vulnerabilities.
In 2026, advanced capabilities should include:
AI-powered authentication and session handling
Business logic flaw detection
GraphQL and REST API security testing
Support for Infrastructure as Code scanning
Adaptive crawling for single-page applications
Behavioral validation to reduce false positives
It is also worth evaluating how mature a platform’s AI capabilities are. Some vendors use AI primarily for reporting or prioritization, while others incorporate autonomous reasoning into the testing engine itself.
Choose a solution that aligns with the complexity of your application architecture today and where it is headed in the next three to five years.
Support model and community strength
Support quality plays a critical role in long-term success, especially for teams without dedicated application security engineers.
Open-source tools like ZAP rely heavily on community forums, documentation, and peer contributions. While this can provide flexibility and cost savings, it also means troubleshooting and optimization require internal expertise.
Enterprise vendors typically offer structured customer support, onboarding assistance, and service-level agreements. Some modern platforms also provide proactive guidance, tailored remediation assistance, and faster iteration cycles driven by user feedback.
When evaluating support, consider:
Availability of live technical support
Responsiveness and expertise of support engineers
Documentation quality and knowledge base depth
Community ecosystem and third-party integrations
A strong support model reduces friction during implementation and ensures long-term operational stability.
Final thoughts
Invicti remains a powerful and mature DAST solution, particularly valued for its proof-based scanning and enterprise scalability. However, the 2026 application security landscape is defined by continuous deployment, AI-generated code, API sprawl, and increasingly complex business logic.
As a result, many organizations are expanding their evaluation criteria beyond traditional vulnerability detection. They are looking for platforms that balance detection accuracy with operational efficiency, developer adoption, runtime validation, and pricing flexibility.
Whether you choose an open-source solution like ZAP, an enterprise-focused platform like Veracode or HCL AppScan, or a modern AI-native platform like Beagle Security, the key is alignment.
Align your choice with:
Your development velocity
Your compliance obligations
Your application architecture complexity
Your internal security expertise
Your long-term growth plans
The right alternative should not only protect your applications today but also scale seamlessly as your organization evolves, your codebase expands, and your security maturity deepens.
A well-informed decision will help you move from reactive vulnerability management to proactive exposure resilience in 2026 and beyond.


![Top vendor application security tools [2026] Top vendor application security tools [2026]](/blog/images/top-vendor-application-security-testing-tools-2026-cover.webp)



![Top API security vendors [2026] Top API security vendors [2026]](/blog/images/top-api-security-vendors-cover.webp)

![Top enterprise application security tools [2026] Top enterprise application security tools [2026]](/blog/images/blog-banner-four-cover.webp)
![Top Snyk alternatives and competitors [2026] Top Snyk alternatives and competitors [2026]](/blog/images/top-snyk-alternatives-cover.webp)


![Top Burp Suite alternatives in the market [2026] Top Burp Suite alternatives in the market [2026]](/blog/images/burpsuite-alternatives-cover.webp)
