
Your organization’s IT systems and processes are the backbone of your business.
IT security breaches and system break-ins can seriously impact your company’s bottom line. Hence, it is important to conduct regular and systematic security checks on your IT networks and systems.
An IT security audit helps you clearly understand the state of your IT systems security. It highlights areas that need improvement to protect your valuable data and maintain business continuity.
Did you know? IBM’s Cost of a Data Breach reports show that the global average breach cost hit $4.44 million in 2025, while smaller businesses with fewer than 500 employees were already facing around $3.31 million per breach based on 2023 data - showing that no organization is safe from serious financial impact.
Key takeaways
IT security audits are crucial for protecting your business from data breaches and cyber threats. They help you stay ahead of vulnerabilities.
Conducting regular audits can help you detect security gaps early and fix them before they become serious problems.
Audits also help you stay compliant with important regulations like GDPR, HIPAA, and PCI DSS, avoiding legal and financial penalties.
There are different types of audits (internal, external, compliance-focused, and risk-based) so you can choose what best fits your organization’s needs.
You should perform a full audit at least once a year, and also run audits whenever major changes happen in your IT environment.
A comprehensive IT security audit checklist has been included that can help you get started.
What is an IT security audit?
An IT security audit is a detailed and regular review of your entire information technology infrastructure, policies, processes and protocols.
This helps you identify potential threats and vulnerabilities that could be exploited by hackers and cyber-criminals. It also ensures compliance with industry standards and regulations such as PCI DSS, GDPR, HIPAA, ISO 27001, and NIST.
A thorough information security audit includes an in-depth review and evaluation of the following critical components of your IT infrastructure:
Internal security policies and procedures
Physical Information Systems environment and configuration
Software applications – security patches and updates
Network architecture and access controls
Information/data protection, encryption and protocols
Employee/user access controls, security awareness and training
The final output of this audit process is a detailed report which outlines the security gaps, potential risks, and specific mitigation steps.
Security audits today have evolved beyond simple compliance checks and have become strategic tools for risk management. They help your organization understand security vulnerabilities, identify potential threats, and develop targeted remediation plans to enhance your overall security posture.
Importance of IT security audits
Now that we understand what security audits entail, let’s explore why they’ve become indispensable for modern organizations. Below are the benefits of regular information security audits.
Proactive mitigation of risks
Information security audits help identify vulnerabilities before malicious actors can exploit them. By systematically checking your security controls and processes, your organization can uncover weaknesses in its defense mechanisms and implement effective countermeasures.
This proactive approach to security is more cost-effective than responding to security breaches after they occur.
Compliance with regulatory requirements
Many industries are subject to strict regulatory requirements related to data protection and privacy. Non-compliance can result in severe penalties, legal consequences, and reputational damage.
Security audits help your organization ensure compliance with regulations such as the Health Insurance Portability and Accountability Act (HIPAA), the Sarbanes-Oxley Act (SOX), the General Data Protection Regulation (GDPR), and other industry-specific frameworks.
Protection of sensitive information
A security audit ensures that necessary safeguards are in place to protect your organization’s data about your operations, clients and employees.
It helps prevent unauthorized access, use, disclosure, disruption, modification, or destruction of your sensitive data.
Business continuity and resilience
Security audits evaluate your organization’s incident response capabilities and disaster recovery plans.
This assessment ensures that your business can continue operating during and after security incidents, minimizing downtime and financial losses.
Trust and reputation management
By conducting regular information security audits, it demonstrates your organization’s commitment to data protection and security.
This commitment builds trust with customers, partners, and stakeholders while also enhancing your organization’s reputation in an increasingly security-conscious marketplace.
Types of IT security audits
Information security audits can be categorized based on various parameters including approach, methodology, and scope.
Understanding their differences helps you choose the most suitable audit type for your organization’s specific security needs and objectives.
Based on approach
Internal audits
Internal information security audits are conducted by your organization’s own staff, typically the internal audit team, in collaboration with IT security professionals. These audits offer several advantages:
Deep understanding of the organization’s systems and processes
Lower direct costs compared to external audits
Opportunity to develop in-house security expertise
Ability to conduct more frequent assessments
However, internal audits may lack the objectivity and fresh perspective that external auditors bring to the process. This limitation is precisely where external audits provide complementary value.
External audits
For external audits, IT security audit services provided by third-party specialists are used to assess your organization’s security posture. These independent evaluations offer several benefits:
Unbiased perspective and objective findings
Specialized expertise and experience across multiple industries
Credibility with stakeholders, regulators, and business partners
Fresh insights and innovative recommendations based on broader industry exposure
External audits are specifically valuable for compliance certifications and when your organization needs to demonstrate the effectiveness of its security measures to external stakeholders.
Based on methodology
Compliance audits
Compliance-focused security audits evaluate your organization’s adherence to specific regulatory frameworks, standards, or industry requirements. These include assessments for HIPAA, SOX, ISO 27001, NIST frameworks, PCI DSS, and other mandatory compliance requirements.
The main objective is to ensure that your security controls meet the required standards while also making sure your organization can demonstrate compliance to regulators or certifying bodies.
Risk-based audits
While compliance audits focus on meeting standards, risk-based security audits focus on identifying and evaluating security risks based on your organization’s unique business environment and objectives.
These audits identify areas which have the highest potential impact, helping you to allocate resources more effectively to address the most significant threats. Risk-based audits typically involve:
Identifying critical assets and their value to your organization
Assessing threats and vulnerabilities specific to those assets
Evaluating the effectiveness of existing controls
Recommending targeted improvements based on risk exposure
Penetration testing
Penetration testing is a specific type of security assessment. It involves simulating real-world cyberattacks to identify exploitable vulnerabilities in systems, networks, applications, or physical security controls.
Penetration tests provide valuable insights into how well your organization’s defenses can withstand real-world attack scenarios. It also helps identify security weaknesses that might be missed in other types of audit approaches.
Comprehensive security audits
Comprehensive security audits combine different elements of compliance checks, like risk assessments, and technical testing, to provide a complete view of your organization’s security posture.
These thorough evaluations examine all aspects of information security, including:
Physical security controls
Technical infrastructure and systems
Applications and software
Human factors and security awareness
Policies, procedures, and governance structures
Incident response capabilities and business continuity plans
How often should security audits be performed?
The frequency of information security audits depends on several factors, including regulatory requirements, industry standards, organizational size, the complexity of IT infrastructure, and risk profile.
However, some general guidelines can help your organization set up suitable audit schedules:
Regular scheduled audits
Most security experts and regulatory frameworks recommend conducting comprehensive information security audits at least once a year.
Annual audits provide an opportunity to evaluate the entire security program and ensure that it continues to meet your organizational needs and compliance requirements. These periodic assessments help you track security improvements over time.
Continuous monitoring and interim assessments
When you continuously monitor your security controls and conduct in-between assessments of high-risk areas, you can detect new vulnerabilities or control weaknesses promptly.
Trigger-based audits
Certain events should trigger additional security audits outside the regular schedule:
Significant changes to IT infrastructure or business operations
After major security incidents or breaches
Implementation of new systems or applications
Changes in regulatory requirements
Mergers, acquisitions, or major organizational restructuring
This dynamic approach ensures that security evaluations remain aligned with the organization’s changing risk landscape.

Industry-specific considerations
Some industries with particularly sensitive data or critical infrastructure may require more frequent security audits.
Healthcare organizations, financial institutions, and government agencies often conduct security audits semi-annually or quarterly to address their higher risk exposure and strict regulatory obligations.
Best practices for IT audits
Regardless of your chosen audit frequency, following established best practices ensures maximum value from your security assessments .
Establish clear objectives and scope
Before beginning an audit, clearly define its objectives, scope, and methodology.
This preparation ensures that the audit addresses your organization’s most important security concerns and compliance requirements while making efficient use of resources.
Follow recognized standards and frameworks
Align security audits with established frameworks such as NIST Cybersecurity Framework, ISO 27001, CIS Controls, or industry-specific standards.
These frameworks provide structured approaches to conducting security assessments and help ensure comprehensive coverage of relevant security domains.
Implement continuous monitoring and automation
Supplement periodic audits with continuous monitoring technologies that can automatically detect and alert on security anomalies or policy violations.
This approach provides real-time visibility into security posture and allows for faster remediation of issues.
Stay current with emerging threats
Your security auditors must remain informed about evolving cyber threats, attack techniques, and security technologies.
Continuous professional education and participation in industry information-sharing communities help ensure that audit methodologies remain relevant in the face of rapidly changing threat landscapes.
Engage stakeholders across departments
Effective security audits require collaboration between IT security professionals, business unit leaders, legal teams, compliance officers, and executive management.
This cross-functional engagement ensures that security controls are evaluated in the context of business needs and that audit findings receive the right attention and resources.
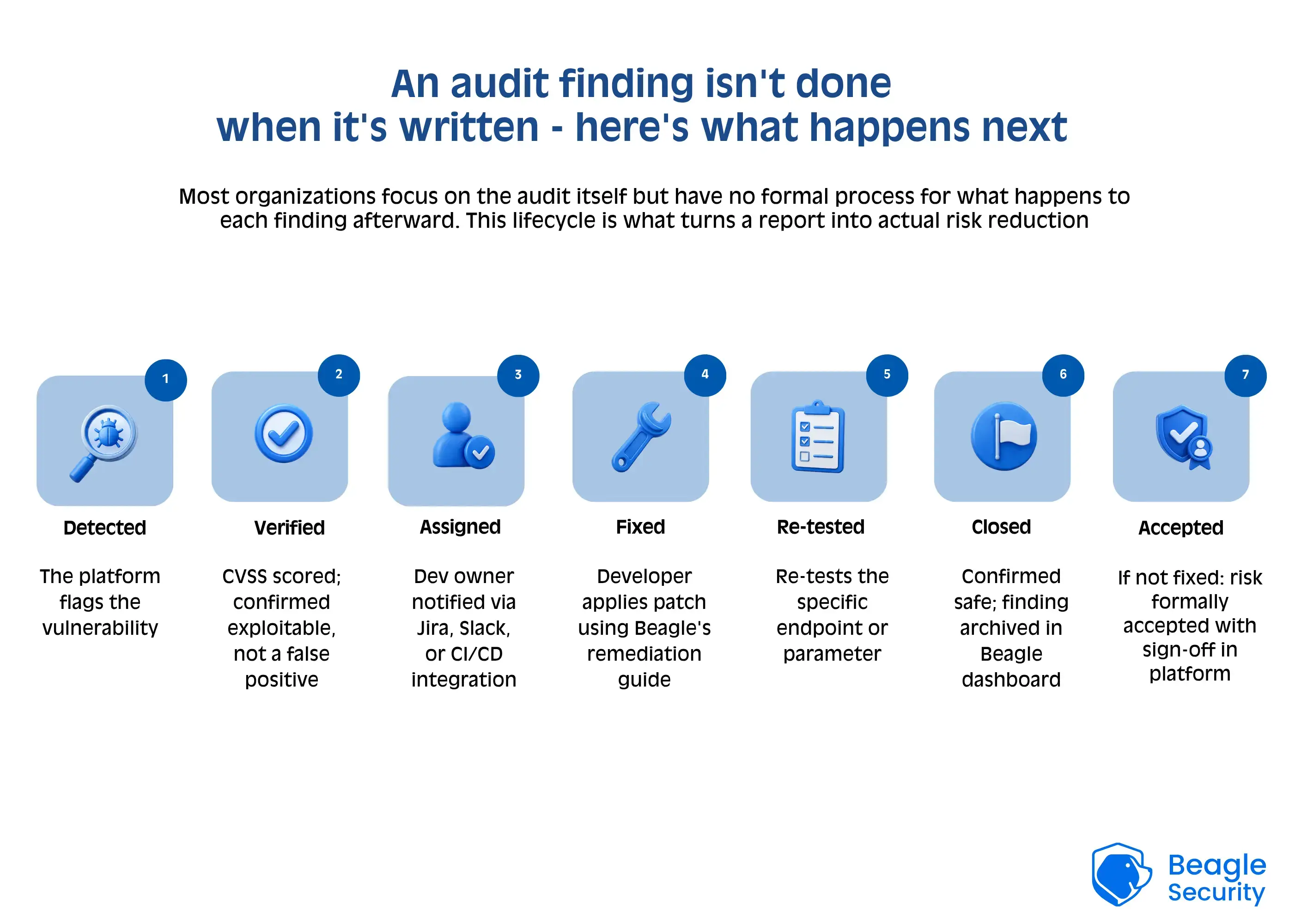
Document findings clearly and prioritize recommendations
Audit reports should clearly communicate findings in language that non-technical stakeholders can understand.
Recommendations should be prioritized based on risk level, with clear guidance on remediation steps and expected outcomes. This clarity supports better decision-making about security investments and improvements.
Conduct regular tabletop exercises
Include scenario-based exercises into the audit process to test incident response capabilities under simulated conditions.
These exercises help identify gaps in security protocols and prepare teams to respond effectively to actual security incidents.
Focus on risk-based prioritization
Not all security weaknesses are equally dangerous for your organization.
A solid audit helps you focus on fixing the most serious problems first - those that are more likely to happen and cause the most damage. This way, your security team can use their time and resources more effectively.
IT security audit checklist
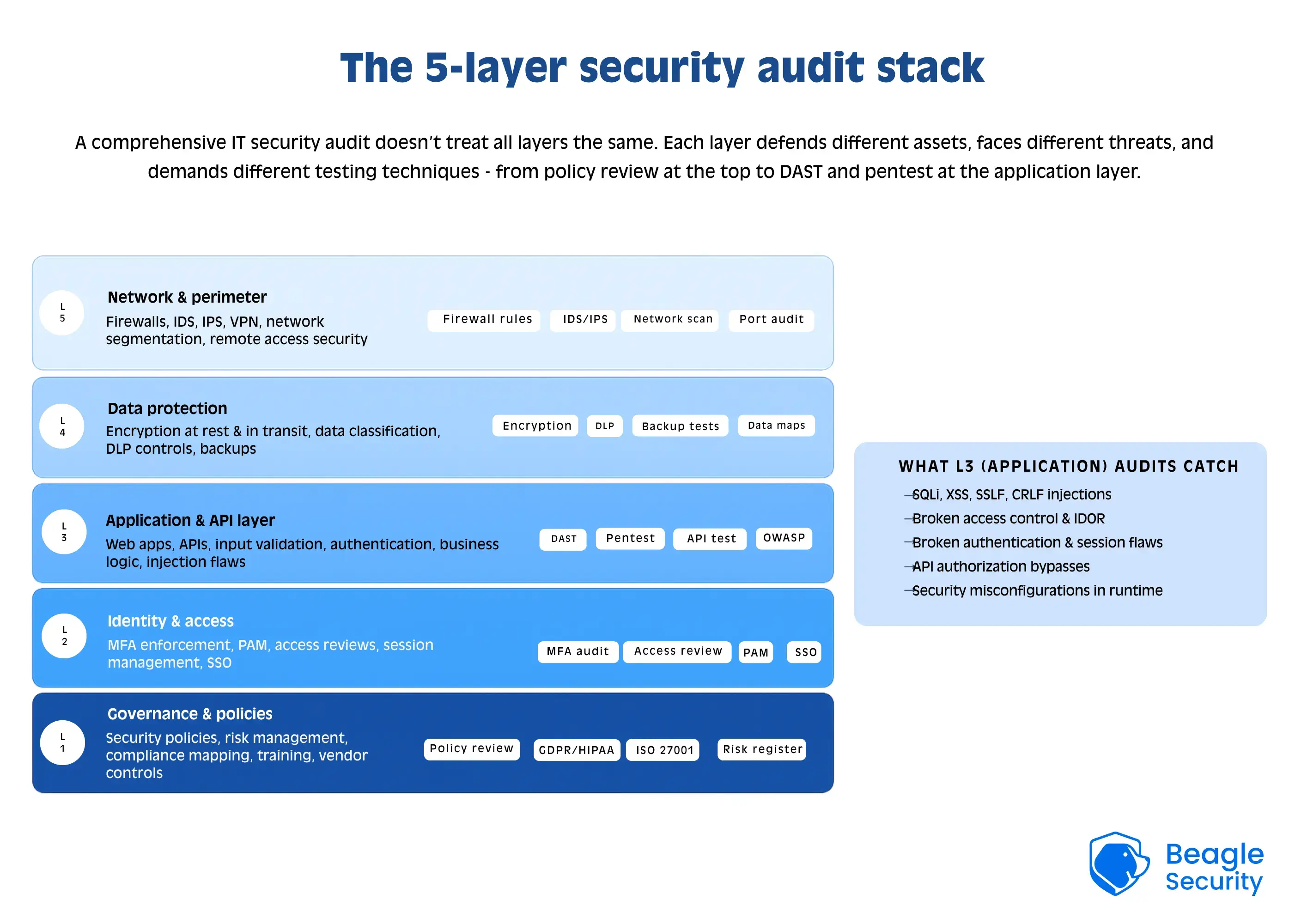
A comprehensive information security audit should examine multiple layers of security controls and processes. The following checklist covers key areas that should be included in such assessments:
Governance and policies
- Review security policies, standards, and procedures for completeness and currency
- Evaluate security governance structure and reporting relationships
- Assess security awareness and training programs
- Verify documentation of security controls and procedures
- Review security strategy alignment with business objectives
Risk management
- Examine risk assessment methodologies and documentation
- Evaluate risk treatment plans and their implementation status
- Review processes for identifying and addressing new security risks
- Assess third-party risk management procedures
- Verify business continuity and disaster recovery plans
Access control and identity management
- Review user provisioning and deprovisioning processes
- Evaluate password policies and implementation
- Assess privileged access management controls
- Verify multi-factor authentication implementation where appropriate
- Review user access rights and separation of duties
- Examine session management controls
Network security
- Evaluate network architecture and segmentation
- Review firewall configurations and rules
- Assess wireless network security controls
- Verify remote access security measures
- Review network monitoring and intrusion detection capabilities
- Examine email and web filtering controls
Systems and applications security
- Review system hardening practices
- Assess patch management processes
- Evaluate change management procedures
- Review secure development practices for in-house applications
- Verify vulnerability management programs
- Assess database security controls
Data protection
- Review data classification and handling procedures
- Evaluate data encryption implementation for data at rest and in transit
- Assess data loss prevention controls
- Review data retention and disposal practices
- Verify backup procedures and security of backups
Physical security
- Evaluate physical access controls to facilities and data centers
- Review environmental controls (power, cooling, fire suppression)
- Assess physical media handling and disposal procedures
- Verify monitoring of physical access and security incidents
Incident management
- Review incident response procedures and capabilities
- Assess security monitoring and detection mechanisms
- Evaluate incident reporting and escalation processes
- Review lessons learned processes following security incidents
- Verify integration with business continuity plans
Compliance and third-party management
- Verify compliance with applicable regulations and standards
- Review vendor security assessment processes
- Evaluate contractual security requirements for service providers
- Assess ongoing vendor security monitoring procedures
This checklist provides a starting point for security audits, but your organization should tailor it based on your specific industry requirements, technology environment, and risk profile.
Final thoughts
Armed with this comprehensive framework for conducting thorough security audits, it’s worth reflecting on how these assessments fit into the broader cybersecurity landscape. With cyber threats becoming more advanced and regulations getting stricter, your organization will need to treat audits as ongoing activities, not just one-time tasks.
The best security audits include regular full assessments, continuous monitoring, and special audits when major changes or new risks appear. This flexible method helps your organization keep track of its security status and update their protections as threats evolve.
IT audits do more than just find weaknesses or compliance issues. They provide useful insights for making smarter security decisions. By using audit results well, your organization can make better use of their security budgets, improve defenses, and prepare for future attacks.
As businesses rely more on digital systems and face a growing range of cyber threats, the role of security audits becomes even more important.
Companies that see audits as chances to improve will be better prepared to protect their data and build trust with customers and partners in today’s challenging digital world.
FAQs
What is the difference between an internal & external security audit?
Internal IT audits are conducted by an organization’s own staff, providing deep institutional knowledge but potentially lacking objectivity. External audits are performed by independent third parties, with expertise in IT security audit services - these provide an unbiased assessment and specialized expertise but at higher direct costs.
What does an IT security auditor do?
An IT security auditor checks a company’s computer systems, rules, and processes to find weaknesses, make sure they follow laws like GDPR or HIPAA, and see how well their security measures work. They look at risks, do technical checks like scans or tests, and share their results with management to help make the company’s cybersecurity better.
What are the 7 principles of IT security?
The 7 main ideas of IT security are: keeping information private, making sure data is accurate and hasn’t been changed, ensuring systems are always available, verifying who is accessing information, deciding what access they have, making sure actions can’t be denied, and keeping track of activities. These ideas help keep data safe, systems running, access controlled, and actions traceable for a secure digital space.
How to prepare for an IT audit?
Getting ready for an IT audit means setting clear goals, checking for potential risks, and collecting all the necessary documents about IT controls. Start by choosing a leader, training your team, and doing practice audits to find any weaknesses. Also, make sure to update important policies like security and change management. Pay special attention to systems that pose the highest risks, check who has access, and keep proof of compliance easy to find.
How is an IT security audit different from a compliance audit?
A security audit comprehensively evaluates the effectiveness of security controls across an organization’s entire IT environment, while a compliance audit specifically focuses on whether security controls meet the requirements of particular regulations or standards such as HIPAA, SOX, or ISO 27001.


![Top vendor application security tools [2026] Top vendor application security tools [2026]](/blog/images/top-vendor-application-security-testing-tools-2026-cover.webp)


![Top API security vendors [2026] Top API security vendors [2026]](/blog/images/top-api-security-vendors-cover.webp)

![Top enterprise application security tools [2026] Top enterprise application security tools [2026]](/blog/images/blog-banner-four-cover.webp)
![Top Snyk alternatives and competitors [2026] Top Snyk alternatives and competitors [2026]](/blog/images/top-snyk-alternatives-cover.webp)


![Top Burp Suite alternatives in the market [2026] Top Burp Suite alternatives in the market [2026]](/blog/images/burpsuite-alternatives-cover.webp)
![Top Invicti alternatives in the market [2026] Top Invicti alternatives in the market [2026]](/blog/images/invicti-alternatives-cover.webp)
