![Best tools for HIPAA penetration testing [2026] Best tools for HIPAA penetration testing [2026]](/blog/images/blog-banner-one.webp)
HIPAA penetration testing is not explicitly required by federal regulation, but Security Rule § 164.308(a)(8) mandates periodic technical evaluations, making penetration testing one of the most effective ways to validate the security of systems handling electronic Protected Health Information (ePHI).
Healthcare organizations remain a prime target for cyberattacks. According to the 2025 Verizon Data Breach Investigations Report, the healthcare sector saw 1,710 security incidents, with 1,542 confirmed data disclosures. Vulnerability exploitation surged 34% year-over-year, now accounting for 20% of all incidents largely driven by attackers targeting internet-facing edge devices that are often poorly managed. This highlights the growing urgency for continuous and application-focused security testing.
Traditional consultant-driven penetration tests cost $15,000 - $35,000 annually, but automated DAST tools can deliver 75-80% equivalent coverage for under $5,000 per year.
This blog explores HIPAA penetration testing requirements, evaluates cost-effective tools, and outlines implementation strategies that help organizations maintain compliance while adapting to evolving security risks.
Does HIPAA require penetration testing?
HIPAA does not explicitly require penetration testing, but Security Rule § 164.308(a)(8) mandates “periodic technical evaluations” that penetration testing directly satisfies in practice.
The regulation states: “Conduct an evaluation in accordance with § 164.308(a)(8) to determine if the security measures implemented are sufficient to reduce risks and vulnerabilities to a reasonable and appropriate level.”
In short: explicitly no, but implicitly yes.
Any time your infrastructure changes, whether it’s a new deployment, a backend refactor, a third-party integration, or an API endpoint handling ePHI, you are expected to re-evaluate whether your current security setup still protects sensitive data.
That’s where penetration testing becomes essential. It simulates real-world attack scenarios to uncover vulnerabilities and validate how your system holds up against potential compromise attempts.
This makes penetration testing one of the most effective ways to satisfy HIPAA’s requirement for technical evaluations, especially in modern cloud-native, API-driven healthcare applications.
What are the HIPAA penetration testing requirements in 2026?
The HIPAA Security Rule establishes three core technical evaluation requirements that penetration testing must address: comprehensive risk analysis, documented vulnerability remediation, and continuous security monitoring.
Meeting HIPAA expectations in practice calls for:
1. Risk analysis requirements
HIPAA requires businesses to conduct regular risk analyses, essentially a deep technical review of systems to identify potential vulnerabilities. This goes beyond a simple checklist. It’s about understanding where your system is weak before those gaps are exploited.
From exposed APIs to misconfigured cloud resources, risk analysis covers all possible entry points where PHI may be at risk. Penetration testing strengthens this process by going beyond surface-level scanning.
Auditors often expect a combination of automated vulnerability scans for speed and coverage, along with manual or tool-assisted penetration testing for accuracy and depth.
2. Vulnerability remediation
Identifying vulnerabilities is only half the job. HIPAA also emphasizes timely remediation of issues discovered during assessments.
Penetration test reports are especially valuable because they prioritize risks based on impact, helping teams focus on what matters most. By addressing critical issues quickly and documenting actions, organizations demonstrate not just compliance, but operational maturity.
3. Continuous scanning
Cloud-native architectures with frequent deployments require ongoing security validation. Even a single API update can introduce vulnerabilities that compromise ePHI protection.
Organizations need tools that deliver high-accuracy results, reduced false positives, and integrate seamlessly with CI/CD pipelines to detect vulnerabilities early in the development lifecycle.
Tool integration requirements: HIPAA-compliant penetration testing tools should also provide audit trails, encrypted result storage, and role-based access controls that align with administrative safeguard requirements.
Defining the scope of your HIPAA penetration test
HIPAA penetration testing scope must cover all systems, applications, and network components that create, receive, maintain, or transmit ePHI. This includes often-overlooked areas such as medical device connectivity and IoMT (Internet of Medical Things) infrastructure.
Core application testing scope
Web application security assessment:
Authentication and session management testing across all user roles
Input validation and injection attack simulation (SQL, NoSQL, LDAP, XML)
Business logic flaw identification affecting patient data access controls
File upload security and data export functionality validation
API security testing requirements:
REST and GraphQL endpoint authentication bypass attempts
Parameter manipulation and data exposure testing
Rate limiting and DDoS protection validation
API versioning security and deprecated endpoint assessment
Infrastructure and network testing scope
Internal network penetration testing:
Network segmentation validation between ePHI and non-ePHI systems
Privilege escalation testing from compromised workstations
Database access control validation and data exfiltration testing
Wireless network security assessment, including guest access isolation
Cloud infrastructure security testing:
Container and serverless function security validation
Cloud storage permission and encryption testing (S3, Azure Blob, GCP buckets)
Identity and Access Management (IAM) role permission validation
Logging and monitoring system security assessment
Medical device and IoMT security testing
Device connectivity security:
Medical device network isolation and communication encryption
Device authentication and certificate management validation
Firmware update security and default credential testing
Patient monitoring system data transmission security
Integration point testing:
HL7 FHIR API security validation
Electronic Health Record (EHR) integration security testing
Telehealth platform security assessment
Medical imaging system (DICOM) security validation
Third-party integration testing scope
Business associate security validation:
Vendor API access control testing
Data sharing agreement technical implementation validation
Third-party authentication integration security assessment
Backup and disaster recovery system security testing
Testing frequency recommendations:
Full-scope testing: Annually or after major system changes
Application-focused testing: Quarterly for customer-facing applications
Infrastructure testing: Semi-annually or after network modifications
Continuous monitoring: Daily automated scans or monthly automated penetration tests with monthly comprehensive analysis
What are the best tools for HIPAA penetration testing?
Healthcare organizations require penetration testing tools that provide comprehensive vulnerability detection, minimal false positives, and seamless integration with development workflows, while maintaining the audit trails required for HIPAA compliance documentation.
Web application & API penetration testing tools
Beagle Security - Best for healthtech startups
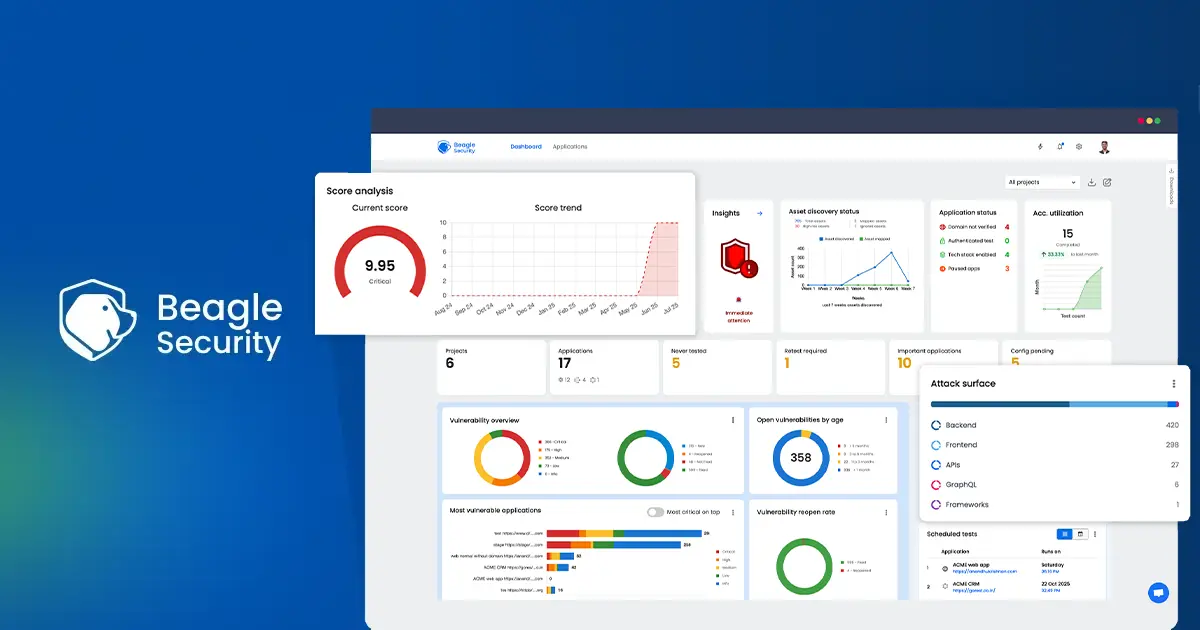
Beagle Security is tailored for startups and growing companies navigating the complexities of HIPAA compliance. Designed for modern development teams, it enables organizations to run comprehensive, automated security tests on web applications and APIs.
Rather than focusing only on surface-level vulnerabilities, Beagle Security simulates real-world attack scenarios based on frameworks like the OWASP Top 10, helping teams understand how attackers might target their applications.
HIPAA-specific capabilities:
Authentication testing: Comprehensive testing of healthcare application login workflows, including SSO, MFA, and role-based access controls
API discovery and testing: Automatic identification of undocumented endpoints handling patient data
Compliance reporting: With pre-built HIPAA-mapped penetration test reports
Implementation for healthcare startups:
Setup time: 10 minutes for basic configuration
Learning curve: Minimal, designed for development and security teams
Pricing: Starting at $119/month for small healthcare teams
Best use cases:
Patient portals and telehealth applications
Healthcare SaaS platforms with API integrations
Medical device connectivity applications
Invicti (formerly Netsparker) – Enterprise healthcare security

Invicti (formerly Netsparker) is a dynamic application security testing (DAST) tool designed for organizations that require deep, automated scanning of web applications and APIs without sacrificing accuracy.
Its Proof-Based Scanning engine reduces false positives by safely validating vulnerabilities, making it particularly valuable for lean security teams. It supports complex authentication workflows, scans modern frameworks and single-page applications, and integrates with CI/CD pipelines to detect issues early.
For HIPAA-focused organizations, Invicti helps validate access controls, input sanitization, and session management, which are core technical safeguards under the HIPAA Security Rule.
Implementation considerations:
Pricing: $37,000 annually, depending on application complexity
Setup complexity: Requires a security team or consultant for optimal configuration
Learning curve: 2 to 4 weeks for healthcare teams to achieve proficiency
Best fit: Organizations with 50+ applications or complex infrastructure
Network penetration testing tools
Metasploit - Internal network security validation
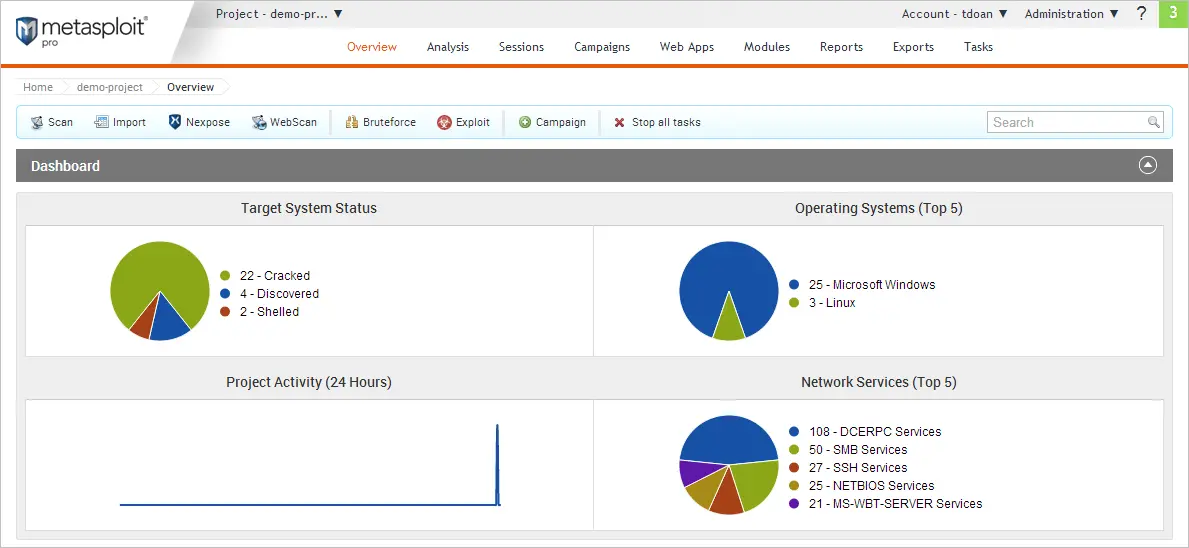
Metasploit remains the industry standard for internal network security testing, offering extensive exploit capabilities for validating healthcare network segmentation and access controls under the HIPAA Security Rule.
Its powerful exploit library and scripting capabilities make it a preferred choice for professional penetration testers. However, this power comes with complexity, and effective use requires strong technical expertise, especially in network configuration.
For startups without dedicated security teams, this learning curve can be significant.
Implementation requirements:
Technical expertise: Requires experienced penetration testers or security consultants
Learning curve: 3–6 months for healthcare IT teams to achieve proficiency
Infrastructure requirements: Isolated testing environments separate from production ePHI systems
Compliance considerations: Careful scoping required to avoid ePHI exposure during testing
Cost considerations:
Metasploit Pro: $15,000 per user/year for commercial healthcare use
Community Edition: Free, but requires significant expertise
Metasploit Express: $2,000 – $5,000 per year. A lower-tier commercial version focused on faster, automated scans and basic penetration testing
Note: Pricing often changes and is usually sold through Rapid7 via custom quotes.
Best use cases:
Annual network security assessments
Medical device security validation
Business associate access testing
Incident response training and preparation
Final thoughts
HIPAA penetration testing in 2026 requires a balanced approach, combining automated tools for continuous monitoring with professional manual testing for comprehensive compliance validation.
The key to successful implementation lies in selecting tools that align with your organization’s technical capabilities while also providing the level of documentation required for regulatory compliance.
Essential implementation principles:
Start with automated tools to establish baseline security and build internal expertise
Focus on ePHI data flows and ensure testing covers all systems handling patient information
Document everything with clear mapping to HIPAA Security Rule requirements
Plan for growth by selecting tools that scale with organizational expansion
Integrate with development workflows to catch vulnerabilities before production deployment
Your 2026 HIPAA penetration testing program should prioritize:
Risk-based testing scope aligned with actual ePHI exposure and business impact
Tool selection that balances comprehensive coverage with resource constraints
Documentation standards that satisfy OCR audit requirements and support compliance reviews
Continuous improvement based on evolving threats and regulatory updates
Healthcare organizations that implement comprehensive and well-documented penetration testing programs are better positioned to scale securely while maintaining patient trust and regulatory compliance.
FAQs
Is penetration testing required for HIPAA?
HIPAA does not explicitly require penetration testing. However, the Security Rule § 164.308(a)(8) mandates periodic technical evaluations, and penetration testing is widely used to meet this requirement by validating the effectiveness of security controls protecting ePHI.
Does HIPAA require annual penetration testing?
HIPAA does not specify annual penetration testing as a strict requirement, but it does mandate “periodic” technical evaluations under § 164.308(a)(8). In practice, this is commonly interpreted as conducting comprehensive penetration testing at least once a year, along with additional testing after significant system changes.
What’s the difference between vulnerability scanning and penetration testing for HIPAA compliance?
Vulnerability scanning uses automated tools to identify potential security weaknesses, while penetration testing goes a step further by simulating real-world attacks to determine whether those vulnerabilities can be exploited to access ePHI. This makes penetration testing essential for demonstrating that security measures are effective in reducing risk, as required by the HIPAA Security Rule.
![Best tools for SOC 2 compliance penetration testing [2025] Best tools for SOC 2 compliance penetration testing [2025]](/blog/images/blog-banner-two-cover.webp)