Black box penetration testing is one of the most realistic approaches to security simulating how an external attacker would attempt to break into your system with no prior knowledge of its internals.
With cyberattacks becoming more advanced and harder to detect, businesses of all sizes are turning to penetration testing to identify vulnerabilities before attackers exploit them. Among these, black box penetration testing stands out for the unbiased, outsider perspective it brings to external security assessment.
It provides a clear view of your organization’s external security posture, helping uncover weak points that might otherwise go unnoticed. This guide explains what black box penetration testing is, when to use it, and how to choose the right approach for your business.
What is penetration testing?
Penetration testing is a structured, authorized simulation of a cyberattack. Security professionals attempt to exploit vulnerabilities in applications, networks, or systems before malicious actors do.
The primary objectives are:
Identifying exploitable weaknesses before they are discovered and abused
Assessing whether existing security controls hold up under realistic attack conditions
Testing incident response readiness when something does go wrong
Meeting compliance obligations under frameworks like SOC 2, ISO 27001, PCI DSS, or HIPAA
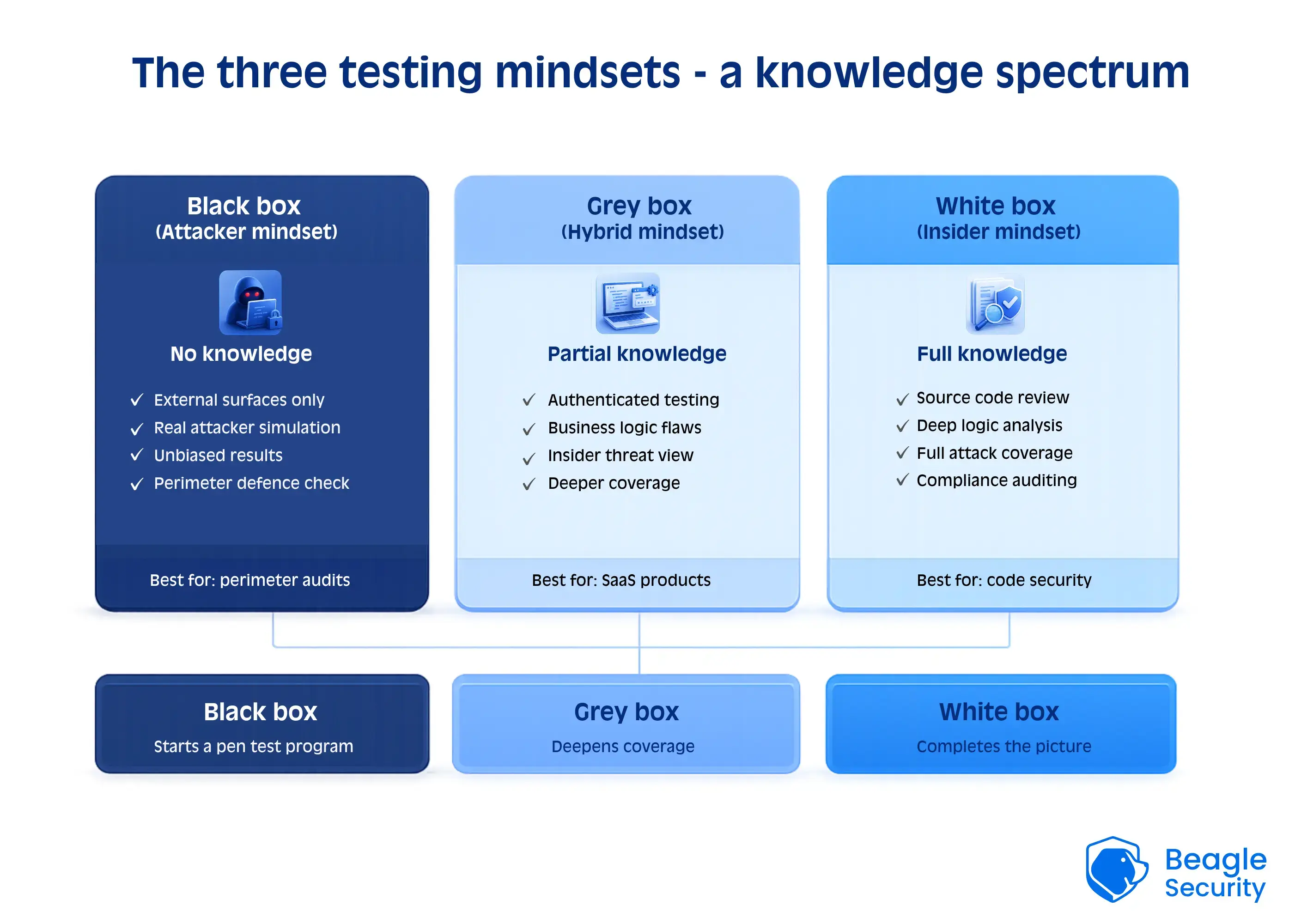
Penetration tests fall into three broad categories depending on how much information the tester has before they begin: black box, grey box, and white box.
What is black box penetration testing?
Black box penetration testing is a method where the tester has no prior knowledge of the system, network, or application being tested.
The goal is to mimic a real-world cyberattack from an external perspective, just as a malicious hacker would attempt to infiltrate your systems without insider access.
In a black box scenario, the tester starts from scratch, gathering information through reconnaissance and scanning, and then tries to exploit vulnerabilities discovered along the way.
Key characteristics:
No internal access or credentials are provided to the tester
Scope is limited to external attack surfaces: web applications, APIs, and public-facing infrastructure
Simulates real-world attack behavior, testing detection and response capabilities.
Ideal for assessing perimeter security and understanding external risk exposure.
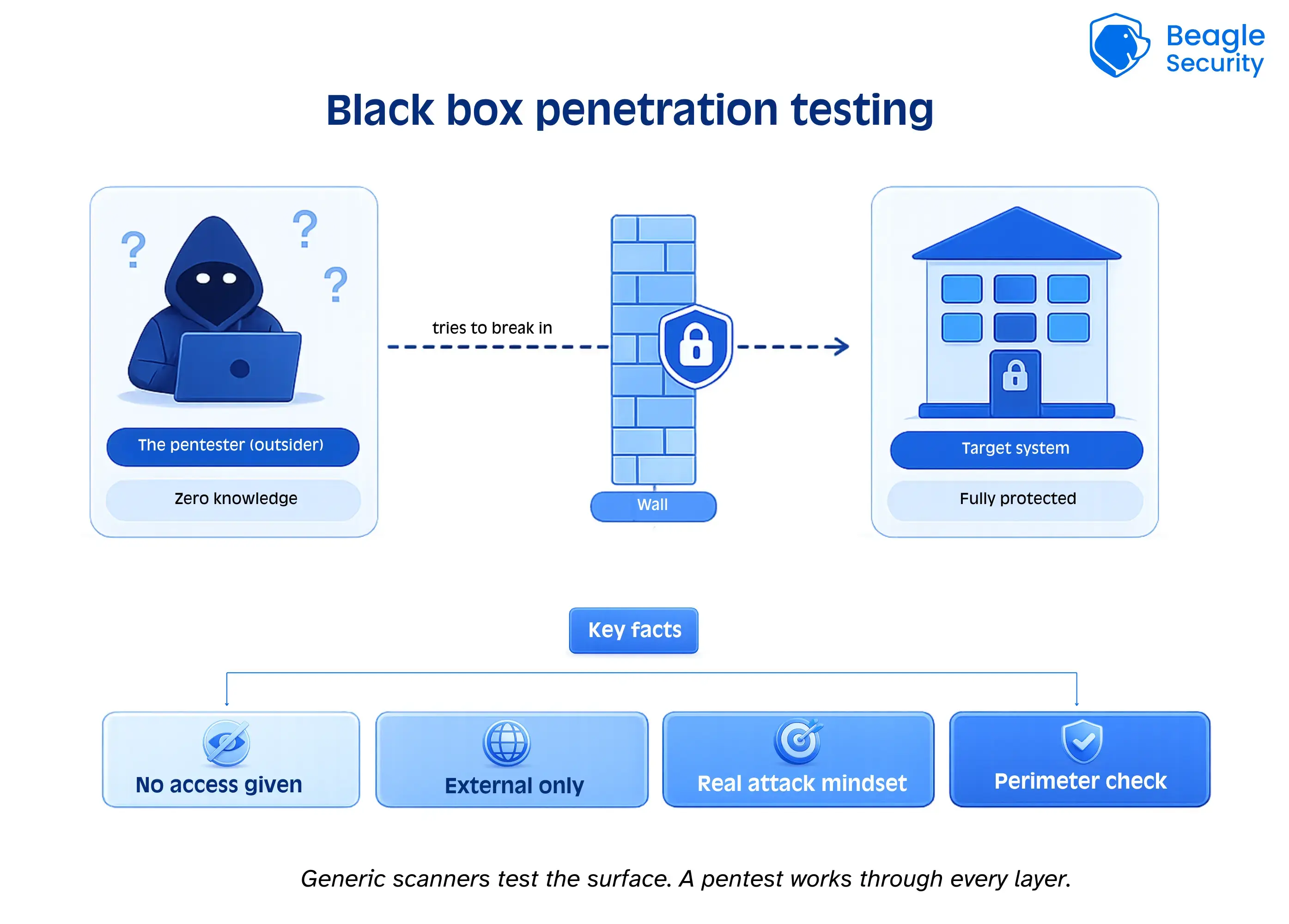
By adopting a black-box approach, organizations can see how effective their firewalls, intrusion detection systems, and external configurations are against real attackers.
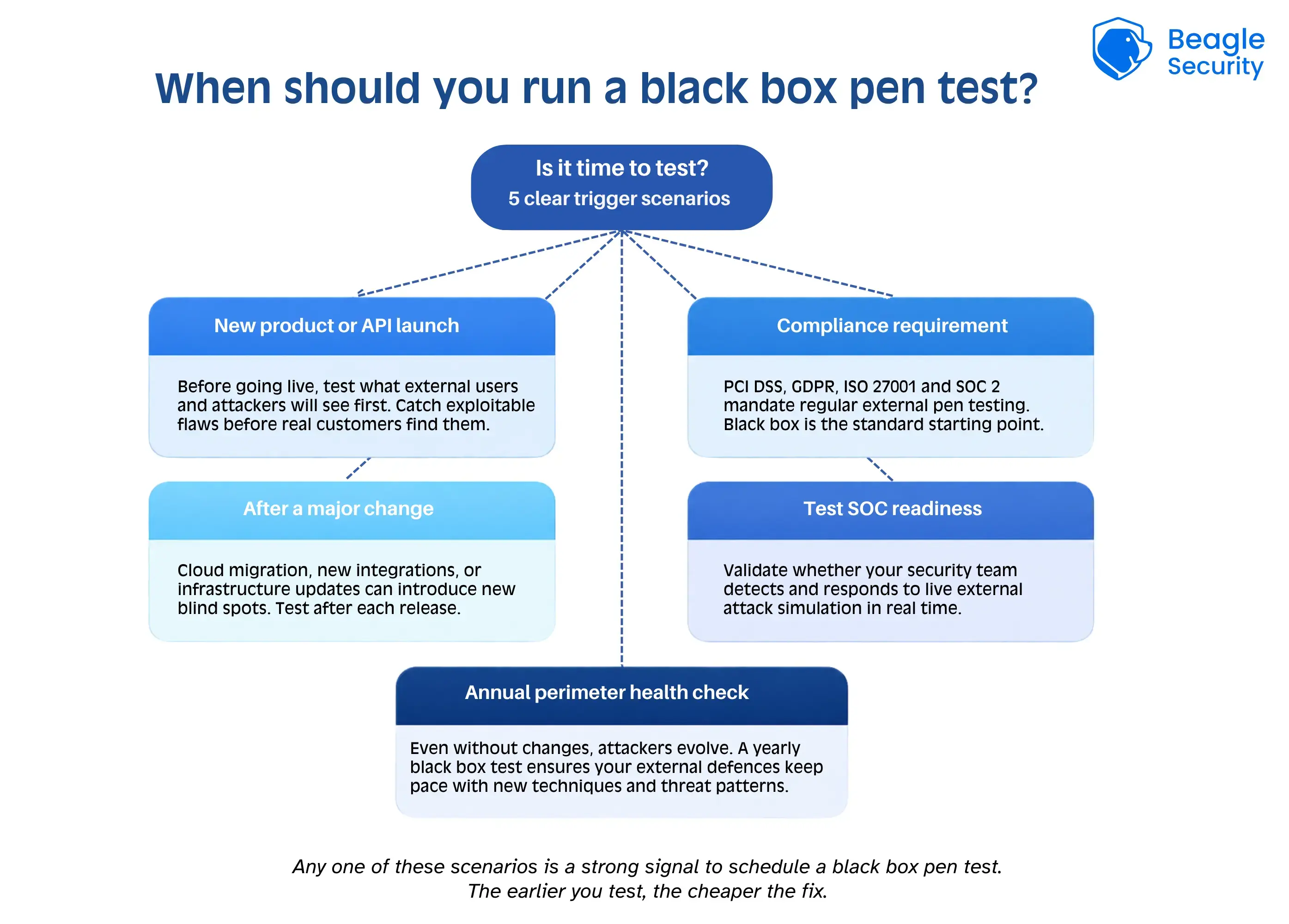
When do you need a black box penetration testing?
Not every organization needs black-box testing all the time, but there are specific scenarios where it adds significant value.
You should consider a black box penetration test when you want to:
1. Test external resilience
If your goal is to evaluate how well public-facing infrastructures (like web apps, APIs, or servers) hold up against attack, black box testing is the most direct method.
2. Validate attack detection and response
A black box test also measures how well your security operations center (SOC) or incident response team detects and responds to external threats in real time. If the test completes without triggering a single alert, that is its own finding.
3. Meet compliance and regulatory requirements
Many standards like PCI DSS, GDPR, and ISO 27001 recommend regular external penetration testing to ensure your systems are resilient to attacks.
4. After major infrastructure changes
If you’ve recently undergone cloud migration, new integrations, product releases. Each of these introduces a potential new attack surface. A black box test after significant changes helps catch vulnerabilities introduced during the transition. product releases, or new integrations, a black-box test can reveal vulnerabilities introduced during updates.
5. Conduct pre-launch security assurance
Before deploying a new SaaS product, mobile app, or API, black-box testing helps identify exploitable flaws that internal teams may have missed, before customers data is exposed.
How to perform black box penetration testing using Beagle Security
Performing black box penetration testing manually can be complex and time-consuming, requiring expert knowledge of tools, scripting, and attack techniques.
However, platforms like Beagle Security automate and simplify the process using AI-driven testing while ensuring accurate, continuous, and standards-aligned assessments.
Here’s how to conduct a black box penetration test effectively using Beagle Security:
Getting started
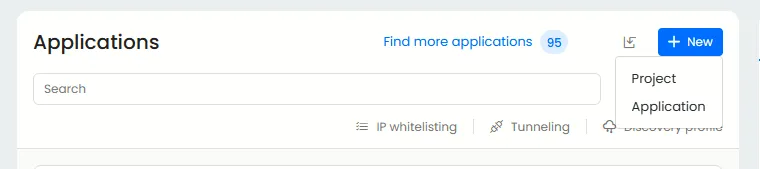
In the applications tab in the left corner, choose to add a new application or create a new project.
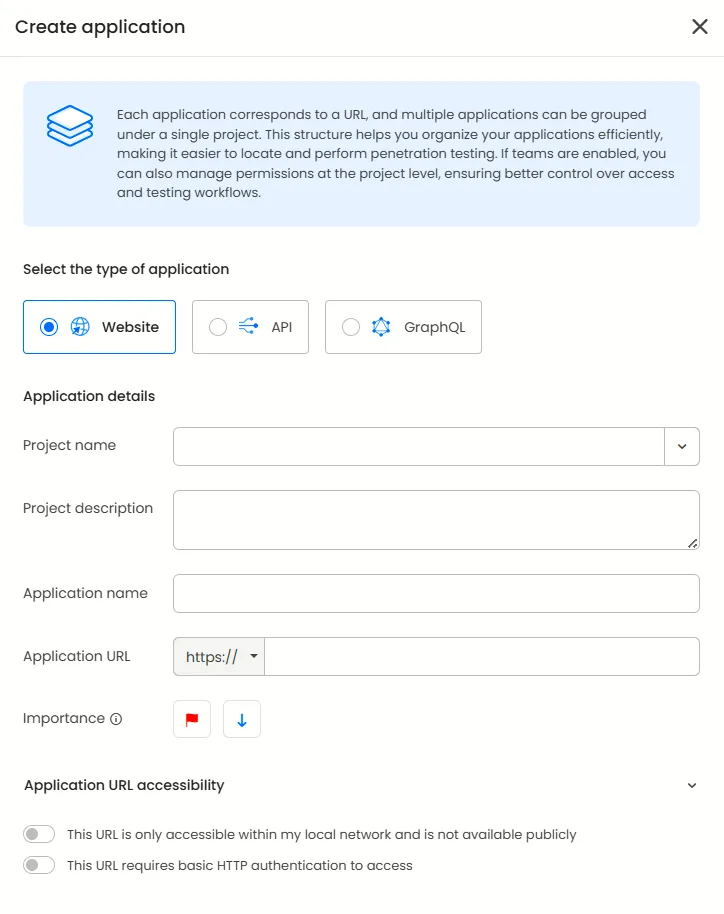
In the ‘create application’ section, you can choose the type of application you wish to create. Currently Beagle Security offers three types which are website, API and GraphQL.
After choosing the application, you can decide the other parameters such as:
The project to which it belongs to
Application name & URL
Importance of said application
Accessibility of URL (HTTP authentication requirements and availability on public networks)
Starting the test
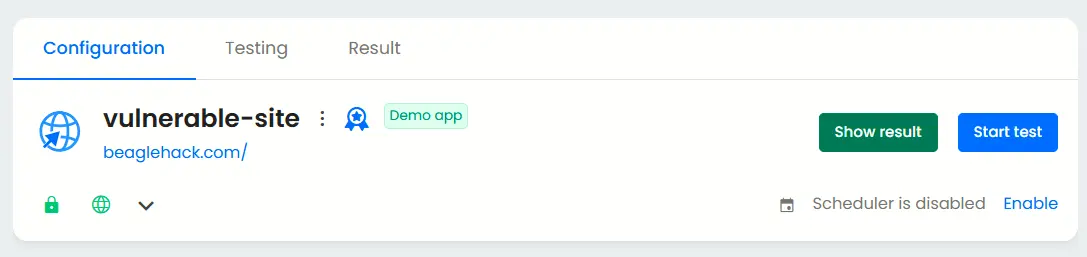
After you have set up your application, click on the ‘start test’ button to commence Black box testing without any privileged access.
Advantages and disadvantages of black box penetration testing
Advantages
Realistic attack simulation: Accurately replicates external hacker behavior.
No insider bias: Provides an unbiased evaluation of external security.
Validates detection & response: Tests real-time security readiness.
Regulatory alignment: Helps meet global compliance standards.
Cost-effective for external testing: Focuses resources on the most exposed areas.
Disadvantages
Limited visibility: Testers cannot assess code-level vulnerabilities or internal systems that are not externally reachable.
Time-intensive: Reconnaissance and exploitation phases can be lengthy.
Incomplete internal coverage: May miss deeper, code-level vulnerabilities.
Potential false negatives: Some vulnerabilities may remain undiscovered due to lack of internal insight.
Despite its limitations, black box penetration testing remains invaluable for organizations seeking realistic threat simulations and continuous external security validation.
Common black-box penetration testing techniques
Black-box penetration testers use a variety of methods to uncover potential entry points. These techniques mirror real-world hacker tactics, helping organizations identify overlooked security gaps.
Fuzzing
Sending large volumes of unexpected, malformed, or random inputs to web forms, APIs, and network services to trigger crashes, logic failures, or unhandled exceptions. Fuzzing is effective at exposing input validation flaws and buffer overflows.
Syntax testing
Injecting inputs that violate expected formats, missing fields, illegal characters, truncated JSON or XML, unexpected encodings. The goal is to expose parsing bugs, validation gaps, and inconsistent error handling.
Exploratory testing
This means performing ad-hoc tests driven by observations and anomalies rather than a rigid checklist. It also uses outputs from one test to design the next.
This approach is ideal when you have limited target context; it surfaces business-logic issues and unexpected flows.
Data analysis
Analyzing response timing, error messages, headers, and payload differences to infer backend logic, authorization behavior, or data structures. Techniques like response diffing and timing analysis can reveal authentication gaps or information leakage.
Test scaffolding
Building automated test harnesses that replay sequences, permutations, and edge cases at scale. Scaffolding is particularly useful for uncovering race conditions, session issues, and chained vulnerabilities that manual testing alone would miss.
Behavior monitoring
Monitoring system stability, error rates, log activity, and resource usage while inputs are being injected. Unexpected crashes, slowdowns, or new log entries often indicate potential vulnerabilities. Combining active probing with passive telemetry from server logs or WAF alerts helps correlate inputs with system responses.
Black-box pentesting checklist
A structured checklist ensures a systematic, thorough assessment. Here’s a simplified black-box penetration testing checklist:
| Action item | Status |
|---|---|
| Define testing scope and targets | ☐ |
| Conduct OSINT(open-source intelligence) gathering | ☐ |
| Identify live hosts and open ports | ☐ |
| Scan web applications and APIs for vulnerabilities | ☐ |
| Test authentication and session management | ☐ |
| Check for injection flaws (SQLi, XSS, command injection) | ☐ |
| Analyze configurations and error handling | ☐ |
| Attempt controlled exploitation | ☐ |
| Document findings and remediation step | ☐ |
| Perform re-test after fixes | ☐ |
Black-box vs grey-box and white-box pen testing
The key distinction between the three testing approaches is how much information the tester knows. Black box simulates an external adversary. Grey box grants partial access credentials, API documentation, or partial architecture knowledge. White box provides complete visibility into source code and infrastructure.
| Aspect | Black box | Grey box | White box |
|---|---|---|---|
| Tester access | No internal knowledge | Partial access(e.g., credentials) | Full access to source code and architecture |
| Focus area | External attack surface | Internal & external components | Code-level vulnerabilities |
| Realism | Highly realistic | Balanced | Low (not attacker - like) |
| Depth of testing | Limited | Moderate | Deep |
| Use case | External web apps, APIs | Application logic flaws | Secure coding validation |
In practice, organizations get the most coverage by combining black box and grey box testing. Black box validates external exposure; grey box tests what an authenticated attacker (such as a compromised user or insider) could access.
How to choose the right pen test provider
The quality of a penetration test depends heavily on the provider therefore,choosing the right penetration testing provider can make the difference between a surface-level assessment and a strategic security investment.
Here’s what to consider:
1. Expertise and certifications
Look for providers with certified testers (CEH, OSCP, or CREST) and proven experience in black-box testing methodologies.
2. Automated and manual balance
The ideal provider combines AI-powered automation (for scale) with manual validation (for accuracy), ensuring high-fidelity results.
3. Transparent reporting
Ensure the provider delivers clear, evidence-backed reports with reproducible test results and remediation advice tailored to your environment.
4. Continuous security validation
Modern security requires ongoing testing. Choose a solution like Beagle Security that supports continuous black-box testing with automated retests after fixes.
5. Compliance alignment
If your organization operates under SOC 2, GDPR, or HIPAA, confirm that the provider’s methodologies align with those frameworks and that reports are formatted to support audit requirements.
Final thoughts
Black box penetration testing is one of the most effective ways to measure real-world cyber resilience. It helps uncover externally exploitable vulnerabilities, validate incident response readiness, and expose gaps that traditional security checks often miss.
When combined with continuous monitoring and periodic grey- or white-box assessments, it becomes part of a broader defense-in-depth strategy that protects both external and internal attack surfaces.
If you’re ready to get started, platforms like Beagle Security provide an automated way to run continuous black box testing without the overhead of manual pentesting. Start a free 14-day advanced trial or explore the interactive demo to see how it fits into your workflow.
FAQs
What is black box in penetration testing?
Black box penetration testing is a security assessment where testers simulate external attacks with no prior knowledge of the target system’s code or architecture. It reflects the perspective of a real attacker probing your public-facing surfaces.
What is the difference between white box and black box penetration testing?
Black box testing starts with zero knowledge, no code, no credentials - simulating a real external attacker. White box testing provides full access to source code and architecture, enabling deep internal analysis.
Black box tests your perimeter. White box tests your code. Most organizations benefit from both.
What types of vulnerabilities can black-box testing detect?
It can uncover authentication flaws, misconfigurations, insecure inputs, logic errors, and other weaknesses exposed through external interfaces such as web apps, APIs, or networks.
How often should companies perform black-box penetration tests?
Ideally, organizations should conduct black-box testing at least once or twice a year, or after major updates, infrastructure changes, or new feature releases.


![Top vendor application security tools [2026] Top vendor application security tools [2026]](/blog/images/top-vendor-application-security-testing-tools-2026-cover.webp)



![Top API security vendors [2026] Top API security vendors [2026]](/blog/images/top-api-security-vendors-cover.webp)

![Top enterprise application security tools [2026] Top enterprise application security tools [2026]](/blog/images/blog-banner-four-cover.webp)
![Top Snyk alternatives and competitors [2026] Top Snyk alternatives and competitors [2026]](/blog/images/top-snyk-alternatives-cover.webp)


![Top Burp Suite alternatives in the market [2026] Top Burp Suite alternatives in the market [2026]](/blog/images/burpsuite-alternatives-cover.webp)
![Top Invicti alternatives in the market [2026] Top Invicti alternatives in the market [2026]](/blog/images/invicti-alternatives-cover.webp)
