
The SaaS (Software-as-a-Service) market has exploded over the last decade, with businesses across every industry relying on cloud-hosted applications for critical workflows. But with this rapid adoption comes an equally rapid rise in cyber threats. Attackers now target SaaS platforms more aggressively than ever, exploiting misconfigurations, insecure APIs, broken access controls, flawed multi-tenant designs, and overlooked business-logic vulnerabilities.
This is exactly why SaaS penetration testing has become a security essential. Whether you’re building a B2B SaaS platform, a consumer app, or a multi-tenant cloud service, a structured pentest helps you uncover real-world vulnerabilities before attackers do.
In this blog, you’ll learn what SaaS penetration testing is, how it works, why it’s important, and how modern SaaS companies can implement it effectively.
What is SaaS penetration testing?
SaaS penetration testing is a security assessment designed to identify, exploit, and validate vulnerabilities in cloud-hosted SaaS applications. Unlike traditional web app pentests, SaaS pentesting focuses on:
Multi-tenant architecture security
API and microservices testing
Role-based access controls (RBAC)
Business logic workflows
Authentication and SSO integrations
Data segregation and privacy controls
A SaaS pentest simulates real-world cyberattacks, using both automated and manual techniques, to understand whether an attacker can compromise the application, access data, disrupt workflows, or escalate privileges.
Because SaaS platforms often process sensitive business data, financial information, or user identities, a pentest helps ensure the service is secure, compliant, and trustworthy.
Why SaaS penetration testing matters
SaaS applications operate in highly dynamic, interconnected, cloud-native environments. Unlike traditional on-premise software, SaaS products must secure multi-tenant data, integrations, APIs, and continuous product updates simultaneously. Because of this complexity, SaaS platforms face a unique set of security challenges that attackers are actively exploiting.
Here’s an expanded breakdown of why SaaS penetration testing is essential:
1. Attackers actively target SaaS misconfigurations
A majority of modern SaaS breaches don’t come from zero-day exploits, they come from misconfigurations. These issues often arise due to rapid feature releases, complex permissions, and human error.
Common SaaS misconfiguration risks include:
Misconfigured access control (users gaining unintended privileges)
Unsecured admin or super-admin consoles
Overly permissive APIs allowing sensitive data exposure
Publicly accessible development or staging environments
Weak or inconsistent tenant isolation rules
API keys or secrets stored incorrectly
Because SaaS platforms evolve quickly, small configuration mistakes can create critical entry points. A penetration test simulates how attackers could exploit these weaknesses before they become incidents.
Why this matters:
Misconfigurations are now one of the leading causes of cloud and SaaS breaches globally, and pentesting helps identify and eliminate them proactively.
2. SaaS is multi-tenant: One flaw can expose every customer
SaaS platforms often serve hundreds or thousands of tenants. A single vulnerability in the multi-tenant architecture can compromise all customers.
Pentesting validates isolation at multiple layers, such as:
Database isolation (row-level, schema-level, or separate DBs)
Role-based access control (RBAC) and privilege escalation paths
API endpoints ensuring no cross-tenant data leakage
Storage systems (S3 buckets, blobs, caches, shared search indexes)
Session management to prevent takeover or session fixation attacks
Even a small logic flaw, like using incremental IDs or leaking tenant IDs in responses, can lead to severe data exposure across the platform.
Why this matters:
Multi-tenant architecture significantly increases the blast radius of a vulnerability. Pentesting ensures that strong isolation boundaries exist and cannot be bypassed.
3. SaaS integrates with third-party systems, broadening the attack surface
Modern SaaS products are part of a complex ecosystem of integrations. Each integration adds new trust relationships, permissions, and potential failure points.
Typical integrations include:
SSO and authentication providers: Okta, Azure AD, Google Workspace
Payment gateways: Stripe, Razorpay, PayPal
CRM/ERP platforms: Salesforce, SAP, HubSpot
Communication tools: Slack, Teams, Gmail APIs
Webhook or workflow automation services: Zapier, Make, internal webhooks
Cloud service providers: AWS, GCP, Azure resources
Attackers target integrations because compromising one external system can give them indirect access to SaaS environment data.
Pentesting helps validate:
Token handling
OAuth/OIDC flows
Webhook signature verification
API permission scopes
Data validation between integrated systems
Why this matters:
SaaS applications operate in a highly interconnected ecosystem, and security weaknesses in integrations can cascade rapidly.
4. Compliance & regulatory standards require proactive pentesting
Organizations handling customer data must follow strict security frameworks. Most compliance routes explicitly mandate regular penetration testing to maintain certification and avoid penalties.
Key standards include SOC 2, ISO 27001, GDPR and PCI DSS.
Why this matters:
Without evidence of ongoing pentests, SaaS companies risk certification issues, customer churn, legal scrutiny, and failed audits.
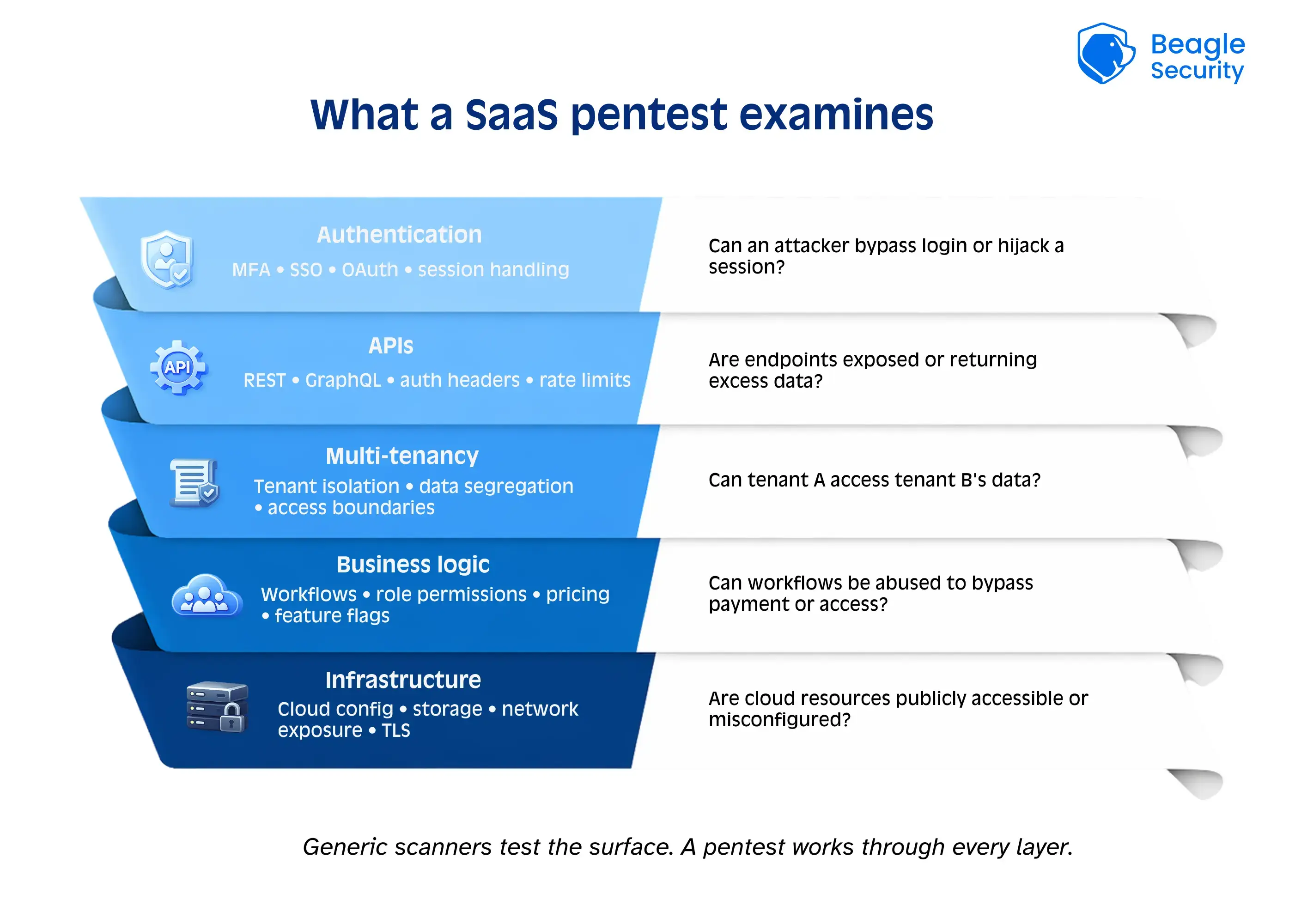
What does a SaaS pentest include?
A complete SaaS penetration test examines the full security posture of your platform, from authentication flows to multi-tenant isolation and underlying infrastructure. Because SaaS applications evolve quickly, each layer must be tested thoroughly to ensure attackers can’t exploit business logic, API weaknesses, or misconfigurations. Here’s what a modern SaaS pentest typically covers:
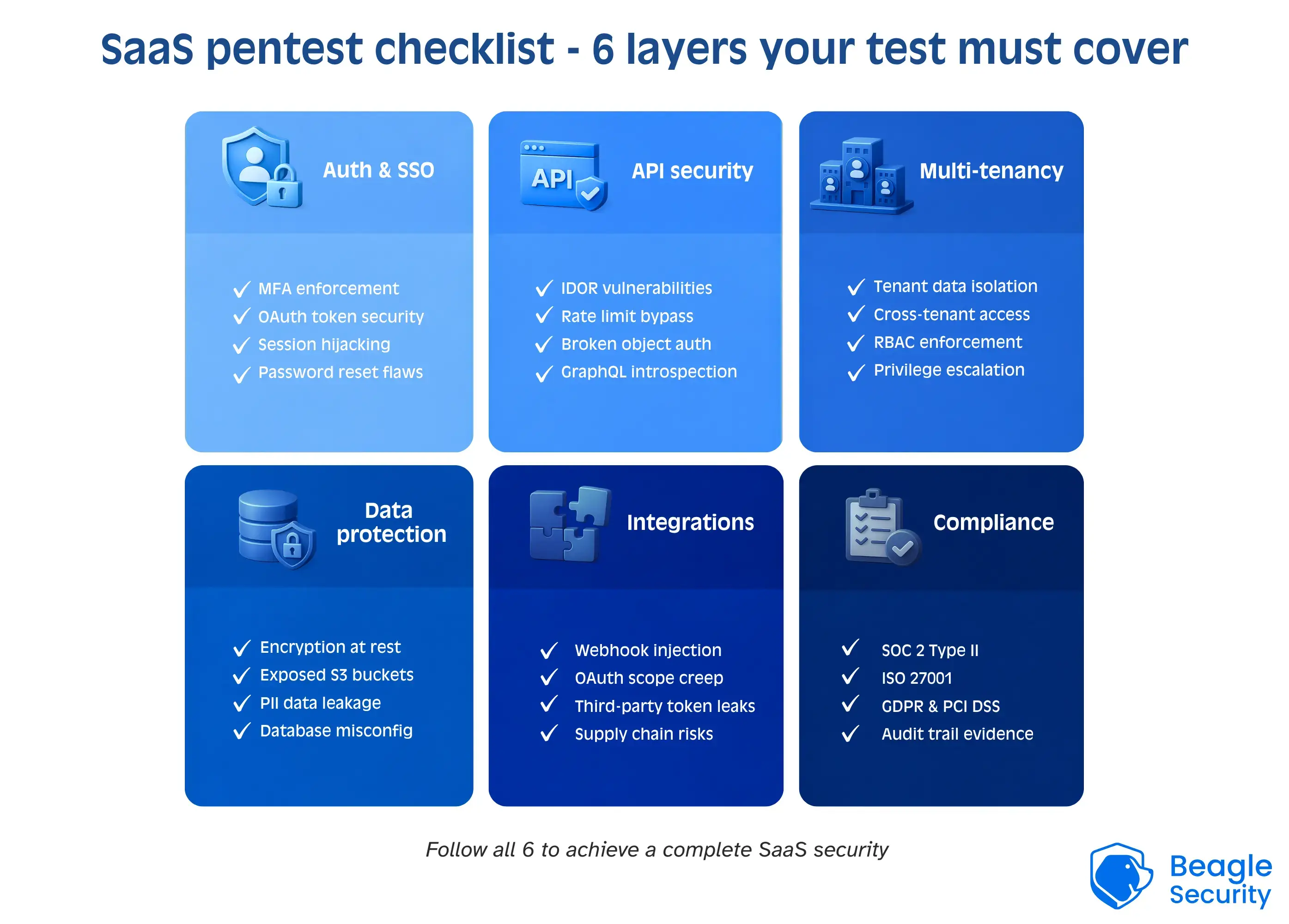
1. Authentication & access control testing
Evaluates MFA, SSO, OAuth, password policies, session handling, and role permissions to ensure attackers cannot bypass authentication or gain unauthorized access.
2. API & microservices security testing
Checks APIs for BOLA, insecure endpoints, rate-limit bypasses, token leaks, and microservice trust issues to prevent data exposure or unauthorized actions.
3. Business logic testing
Identifies workflow flaws like skipped steps, payment bypasses, approval manipulation, or privilege misuse that automated scanners typically miss.
4. Multi-tenant isolation testing
Ensures strict tenant separation by testing for cross-tenant data access, predictable IDs, and weak access controls that could expose other customers’ data.
5. Configuration & infrastructure review
Assesses cloud settings, storage permissions, CI/CD security, dependencies, and secrets management to detect misconfigurations attackers often exploit.
6. Frontend & client-side testing
Tests for XSS, CSRF, DOM issues, insecure CSP, and client-side data exposure to protect users from browser-based attacks.
7. Reporting & remediation verification
Delivers clear findings, impact analysis, and fixes, followed by re-testing to verify vulnerabilities are resolved and security is maintained.
How SaaS penetration testing works: step-by-step process
Scoping & pre-engagement
The scoping phase defines the overall direction of the pentest and ensures both teams are aligned. This includes identifying:
Test boundaries and in-scope functionalities
User roles and tenant types to be tested
Cloud components, APIs, and integrations
Compliance requirements (SOC 2, ISO 27001, GDPR, PCI DSS)
Testing environments (staging, production-mirror, sandbox)
Access needs, accounts, and timelines
This phase removes ambiguity and ensures expectations are clear. The final output is a signed scope document and engagement plan that guides all upcoming testing activities.
Information gathering
In this step, pentesters collect detailed information to understand how the SaaS platform functions. They typically review:
System architecture and data flows
Technology stack (frontend, backend, cloud services)
Authentication flows (SSO, MFA, OAuth, API keys)
API documentation and endpoint structure
Business logic workflows
Public assets such as subdomains or open API docs
Pentesters may also speak with developers or product teams. The goal is to build a complete understanding of the application so testing can be precise rather than guess-based.
Vulnerability assessment
Here, testers perform a broad assessment using both automation and manual checks. Common focus areas include:
Outdated libraries, packages, or frameworks
Known CVEs and dependency risks
Exposed or unauthenticated endpoints
Weak configurations (CORS, headers, rate limits)
Missing security controls or best practices
Insecure or forgotten test/staging environments
This step creates an initial vulnerability map. It highlights all potential weak areas across the SaaS ecosystem before deeper exploitation begins.
Manual exploitation
Manual exploitation is the most critical phase where testers simulate real attackers. They attempt to:
Escalate privileges
Break tenant isolation (cross-tenant access)
Manipulate or abuse APIs
Bypass authentication and session controls
Exploit workflow and business logic gaps
Chain multiple vulnerabilities together
This step validates the true impact of each vulnerability, showing what an attacker could realistically achieve. The goal is to demonstrate real-world risk, not just theoretical scanner results.
Reporting
A strong SaaS pentest report provides both clarity and actionability. It includes:
Executive summary for leadership
Risk scoring with severity levels
Proof-of-concept (PoC) attacks
Step-by-step reproduction instructions
Screenshots or payload samples
Tenant-specific or environment-specific impact
Prioritized remediation guidance
This report helps engineering and security teams understand what went wrong, how severe each issue is, and exactly how to fix it.
Re-test & continuous testing
A pentest isn’t complete until vulnerabilities are validated after fixes. This phase includes:
Re-testing previously identified vulnerabilities
Confirming patches are effective
Checking no new issues were introduced
Updating compliance-ready reports
Providing ongoing scanning or continuous pentest recommendations
Because SaaS products evolve rapidly, many teams shift to continuous testing to catch issues as new features roll out. The goal is not just passing a test once, but maintaining long-term product security.
How often should you perform SaaS penetration testing?
| Scenario | Recommended frequency |
|---|---|
| Minimum for compliance | Annually |
| Fast-moving SaaS companies | Quarterly |
| Enterprise-facing SaaS | Quarterly or bi-annual |
| API-first, multi-tenant, or AI-driven SaaS | Continuous |
| After major releases | Immediately |
| After incidents | Immediately |
The most secure SaaS companies follow a continuous and annual approach:
Continuous pentesting for real-time coverage
One annual full-scope pentest for compliance and audits
This gives you the best of both worlds. Strong security posture year-round and complete documentation for compliance.
SaaS pentesting vs. traditional web app pentesting
| Feature | SaaS pentest | Traditional web pentest |
|---|---|---|
| Multi-tenant testing | Yes | Usually no |
| API-first focus | High | Medium |
| SSO / OAuth | Critical | Optional |
| Role & access control depth | Deep | Standard |
| Compliance requirements | High (SOC 2, ISO) | Medium |
This comparison reinforces the importance of SaaS-specific testing, not generic web testing.
How Beagle Security helps SaaS companies stay secure
Beagle Security offers a modern, automated penetration testing platform designed for high-growth SaaS teams.
Key benefits include:
Business-logic testing with no-code workflows
Advanced API, GraphQL, and authentication testing
Continuous CI/CD native penetration testing
Multi-tenant isolation validation
Role-based scenario testing (RBAC-aware)
Enterprise-ready reports
Integrations with Slack, Jira, GitHub, GitLab, Bitbucket & more
Zero false-positive approach
This ensures SaaS teams get deep security coverage with faster turnaround compared to traditional pentesters.
Final thoughts
SaaS penetration testing is no longer optional, it’s a vital practice that ensures your application, customers, and data remain secure in an increasingly hostile cyber landscape. Modern SaaS platforms operate in complex, API-driven, multi-tenant environments that require deeper testing than traditional web apps.
By implementing regular SaaS pentesting and choosing the right security partner, you strengthen your product’s trustworthiness, reduce your attack surface, and stay compliant with growing security expectations.
If you’re looking for a modern, accurate, and developer-friendly way to test your SaaS platform, Beagle Security offers a complete solution tailored for SaaS workflows.
FAQs
1. What is SaaS penetration testing?
A security assessment that simulates cyberattacks on SaaS applications to identify vulnerabilities in authentication, APIs, multi-tenancy, and business logic.
2. Why do SaaS companies need penetration testing?
To prevent breaches, meet compliance, secure multi-tenant data, and protect API-driven workflows.
3. How often should SaaS platforms be pentested?
Annually at minimum, plus after major updates or before major customer onboarding.
4. Does SaaS penetration testing include APIs?
Yes, APIs are one of the most heavily targeted areas.
5. Can automated scanners replace SaaS pentesting?
No. Scanners cannot detect business-logic or multi-tenant risks. A hybrid manual and automated approach is essential.


![Top vendor application security tools [2026] Top vendor application security tools [2026]](/blog/images/top-vendor-application-security-testing-tools-2026-cover.webp)



![Top API security vendors [2026] Top API security vendors [2026]](/blog/images/top-api-security-vendors-cover.webp)

![Top enterprise application security tools [2026] Top enterprise application security tools [2026]](/blog/images/blog-banner-four-cover.webp)
![Top Snyk alternatives and competitors [2026] Top Snyk alternatives and competitors [2026]](/blog/images/top-snyk-alternatives-cover.webp)


![Top Burp Suite alternatives in the market [2026] Top Burp Suite alternatives in the market [2026]](/blog/images/burpsuite-alternatives-cover.webp)
![Top Invicti alternatives in the market [2026] Top Invicti alternatives in the market [2026]](/blog/images/invicti-alternatives-cover.webp)