
Intruder is a cloud based vulnerability scanner and attack surface management platform designed to help organizations identify security weaknesses across internet-facing systems, applications, APIs, and cloud environments. It has built its reputation around simplicity, continuous scanning, and proactive threat detection. Instead of relying only on scheduled scans, the platform continuously monitors attack surfaces for newly exposed assets, emerging threats, cloud misconfigurations, and known vulnerabilities.
Intruder also supports integrations with cloud providers like AWS, Azure, and Google Cloud, along with DevSecOps and workflow tools that help teams bring vulnerability management into their regular operational processes.
In this review, we’ll take a closer look at Intruder, its key features, strengths, limitations, and how it compares to what modern security teams expect from cloud-based vulnerability management platforms today.
TL;DR: Intruder review
| G2 rating | Gartner rating |
|---|---|
| 4.8/5 (based on 206 reviews) | 4.7/5 (based on 135 reviews) |
As of the latest data on May 2026
Intruder has highly rated reviews on both G2 and Gartner, with users highlighting its ease of use, intuitive interface, and vulnerability identification as major wins.
Source: G2
Source: Gartner
Key features of Intruder
Intruder is designed as a straightforward vulnerability scanning platform for SMBs. Its main features include:
Web application vulnerability scanning for common issues such as SQL injection, XSS, weak configurations, and exposed services. The platform uses scanning technologies based on ZAP along with its own detection capabilities.
Infrastructure and external attack surface scanning that identifies outdated software, exposed systems, weak encryption, and misconfigurations.
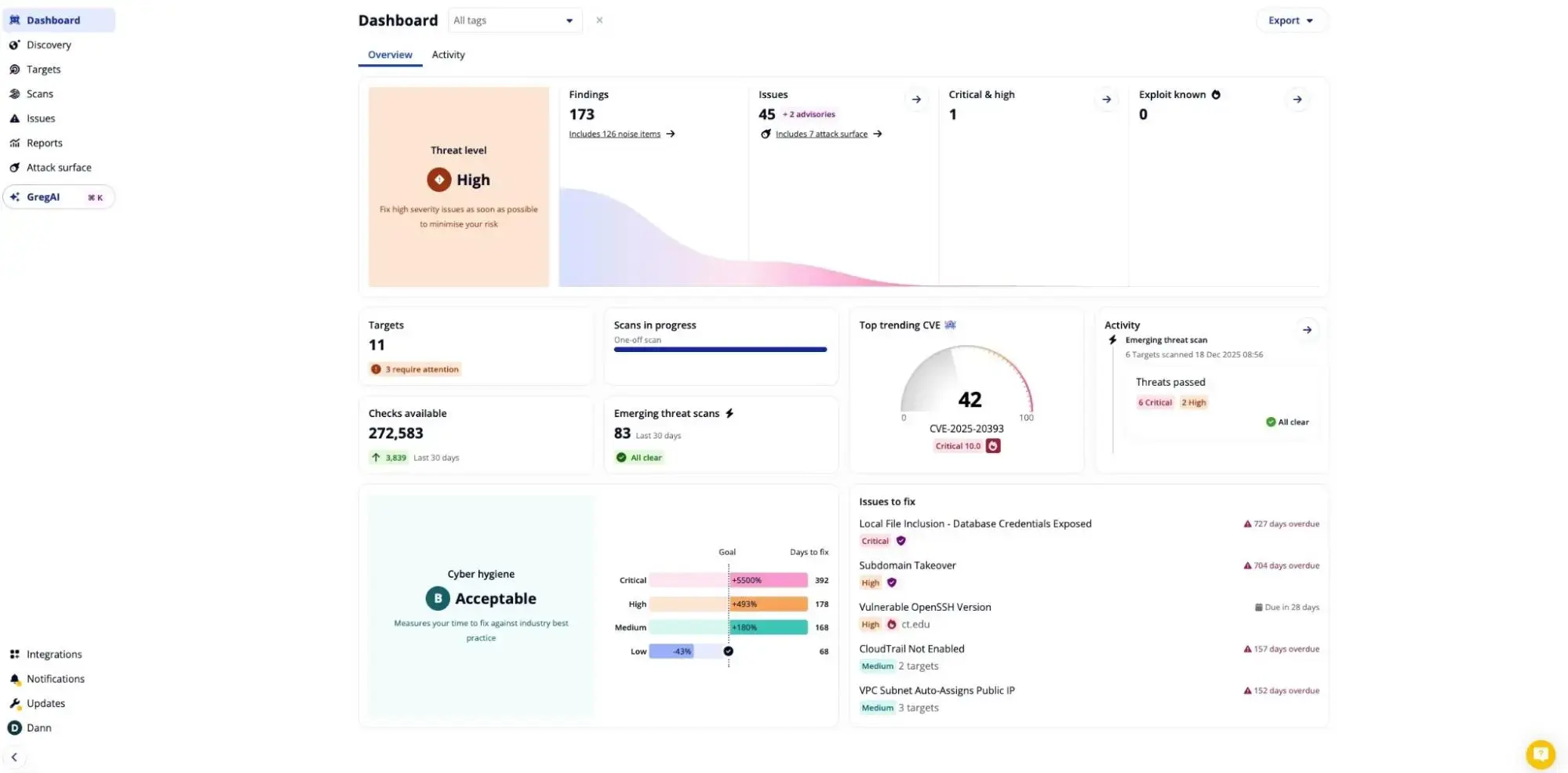
Continuous attack surface monitoring that automatically detects newly exposed assets, IPs, and emerging threats, then triggers scans to help teams respond faster.
Compliance reporting support for frameworks such as SOC 2, ISO 27001, and Cyber Essentials, helping organizations simplify audit preparation and vulnerability tracking.
Integrations with cloud providers and operational tools including AWS, Azure, GCP, Jira, Slack, GitHub, and Microsoft Teams to support DevSecOps and security workflows.
Pros of Intruder
Intruder is generally easy to set up and use, which is one of the main reasons smaller teams and SMBs tend to like the platform. The onboarding experience is fairly straightforward compared to heavier enterprise vulnerability management tools.
The platform does a good job with continuous external attack surface monitoring, especially for organizations that want visibility into exposed assets, outdated services, and internet-facing risks without spending too much time managing scans manually.
Users often highlight the clean interface and overall simplicity of the platform. Findings, risk levels, and remediation guidance are presented in a way that’s easy to understand even for lean security teams.
Integrations with cloud providers, Jira, Slack, GitHub, and other workflow tools make it easier to bring vulnerability management into existing DevSecOps and operational processes.
Intruder works well for organizations that mainly want lightweight cloud-based vulnerability scanning without needing a large security team to operate the platform.
Cons of Intruder
Some users report slow scan completion times, especially when scanning broader environments or larger internet-facing infrastructures.
False positives can still be an issue in certain cases, particularly because parts of the platform rely on established open-source scanning technologies like ZAP and OpenVAS.
Reporting and customization capabilities may feel limited for larger organizations that need deeper workflow customization, advanced reporting, or broader security orchestration features.
Pricing can become difficult to evaluate depending on the features required, and some users feel the licensing structure lacks transparency.
Intruder pricing
Intruder offers four pricing tiers, each targeting different types of users and organizations.
Essential: Aimed for startups, this plan costs $119/month. ($1,430 annually)
Cloud: This plan is for cloud native companies with cost being $239/month. ($2,870 annually)
Pro: Aimed for companies with hybrid environments, this plan costs $399/month. ($4,790 annually)
Enterprise: This plan is a custom plan, aimed at large enterprises and organizations. It’s best to contact the vendor directly for more details.
Summing up
Intruder keeps things simple, and that’s exactly why many smaller teams prefer it. The platform is easy to onboard, straightforward to manage, and works well for organizations that mainly want continuous external vulnerability monitoring without dealing with the operational weight of larger enterprise security platforms.
Intruder does external vulnerability monitoring well. Where it gets harder is when your application has authenticated flows, complex APIs, or business logic that a scanner can’t just crawl from the outside. That’s a different problem entirely.
Beagle Security focuses more on how modern applications actually behave. Its agentic AI-driven pentesting platform is designed to interact with applications dynamically, explore attack paths, and simulate attacker behavior across web applications, APIs, and GraphQL environments.
With capabilities like authenticated testing, CI/CD integrations, compliance reporting, and continuous testing workflows built into the platform, Beagle Security is aimed at teams looking for more adaptive and realistic application security testing.
If that’s the gap you’re trying to close, it’s worth seeing how Beagle Security handles it. Schedule a demo and judge it against what you’re running today.
FAQs
What is Intruder used for?
Intruder is a cloud-based vulnerability scanner used for identifying security weaknesses across websites, servers, cloud infrastructure, APIs, and internet-facing assets.
Is Intruder a vulnerability scanner or a pentesting tool?
Intruder is primarily a vulnerability scanning platform focused on automated detection and continuous monitoring rather than full manual or agentic AI driven pentesting.
Is Intruder suitable for small businesses?
Yes, Intruder is commonly used by small businesses and security teams because of its relatively simple setup, cloud-based deployment model, and easier onboarding experience.










