![Top 15 SaaS security companies [2026] Top 15 SaaS security companies [2026]](/blog/images/blog-banner-six.webp)
SaaS apps today are doing everything - storing data, handling payments, running entire businesses.
Also? They’re exposed to the internet 24x7.
Which means, security isn’t optional anymore. It is not even a ‘later’ problem. Attacks are happening in real time, which makes SaaS penetration tests all the more crucial.
That’s where SaaS security companies come in, which is helping teams stay ahead without slowing everything down.
What are the various categories of SaaS companies?
Not all security tools do the same thing and that’s where things can get confusing.
Some focus on your cloud setup, some on your application, and others on how people access your systems. If you are building or managing a SaaS product, chances are you’ll end up using a mix of these.
Broadly, there are 4 main categories of SaaS security companies. Let’s see what they are.
AppSec
Standing for Application Security , it focuses on your actual app. They help you find things like
Vulnerabilities in your code
Broken authentication
API flaws.
In simple terms, AppSec answers the question ‘can someone break into my app?’.
SSPM
It stands for SaaS Security Posture Management. It’s less about your code and more about how your tools are set up.
Modern teams use a lot of SaaS apps. With all these numerous tools available, misconfigurations can quietly creep in and create security risks.
SSPM tools help your figure out:
Who has access to what
Whether permissions are too open
If sensitive data is exposed
In layman’s terms, it answers ‘are we accidentally leaving things too open?’.
SASE
SASE, standing for Secure Access Service Edge , focuses on protecting how users connect to your system.
With the advent of remote work, people are logging in from everywhere. It could be from a different device, different network or even a different location. That itself creates a whole new level of risk.
SASE tools help
Secure remote access
Monitor user activity
Ensures only verified users and devices can access a specific SaaS app. (Zero Trust Network Access)
Think of it like ** ‘who is getting in, and should they be?’**.
Cloud security
Behind every SaaS app is infrastructure, which includes things like servers, databases, cloud services etc, or in other words, basically the backbone of a system.
Cloud security tools make sure that this foundation is actually secure. They help identify:
Exposed services
Infrastructure level risks.
Misconfigured cloud settings.
Thinking in a simple way, it answers ‘is the system running my application secure?’.
Top SaaS security companies at a glance [2026]
| Company | Category | Starting Price | G2 Rating | Key Features |
|---|---|---|---|---|
| Beagle Security | AppSec | $119/month | 4.7/5 | AI pentesting, continuous testing |
| Invicti | AppSec | Custom pricing | 4.6/5 | Proof based scanning, automated DAST |
| Astrix | SSPM | Custom pricing | 5/5 | Non-human identity discovery, AI agent security |
| Synk | AppSec | Free plan available, paid plans from $25/month | 4.5/5 | Developer first security, risk based prioritization |
| Escape | AppSec | Custom pricing | 5/5 | AI pentesting, attack surface management |
| Todyl | SASE | Custom pricing | 4.6/5 | Endpoint security, GRC |
| Cato Networks | SASE | Custom pricing | 4.5/5 | AI security, detection & response |
| Zygon | SSPM | $3 per user /month | 4.9/5 | Access collaboration, automation |
| Nudge Security | SSPM | $5 per user / month | 4.7/5 | Security nudges, workflow automation |
| Palo Alto Networks | SASE + cloud security | Custom pricing | 4.3/5; 4.6/5 | Prisma Cloud, Cortex XDR |
| Zscaler | SASE | Custom pricing | 4.6/5 | Zero Trust, secure access |
| SentinelOne | Cloud Security | $179.99 per endpoint per month | 4.7/5 | AI powered autonomous agent, cloud native security |
| CrowdStrike | Cloud Security | $59.99 per device, billed annually | 4.6/5 | Endpoint security, exposure management |
| Tenable | Cloud Security | $5,652.20 for 1 year license | 4.5/5 | Exposure management, security hygiene |
| Qualys | Cloud Security | Custom pricing | 4.3/5 | Vulnerability & configuration management, risk remediation |
Beagle Security
Beagle Security is an agentic AI penetration testing platform that helps teams find vulnerabilities in their apps through continuous, automated testing,
It’s designed to fit into development workflows, so security checks can run regularly instead of being a one time effort.
Key features
- Continuous security testing
Runs tests regularly so new vulnerabilities don’t go unnoticed as the app changes.
- Agentic AI pentesting
Uses automation to simulate real world attacks and identify weaknesses.
- API security testing
Tests APIs for common vulnerabilities and misconfigurations.
Pricing
Essential: For $119 per month, it’s perfect for growing teams.
Advanced: For $359 per month, this plan is aimed for organizations with advanced web apps and API security testing needs.
Enterprise: For larger organizations. Pricing is custom.
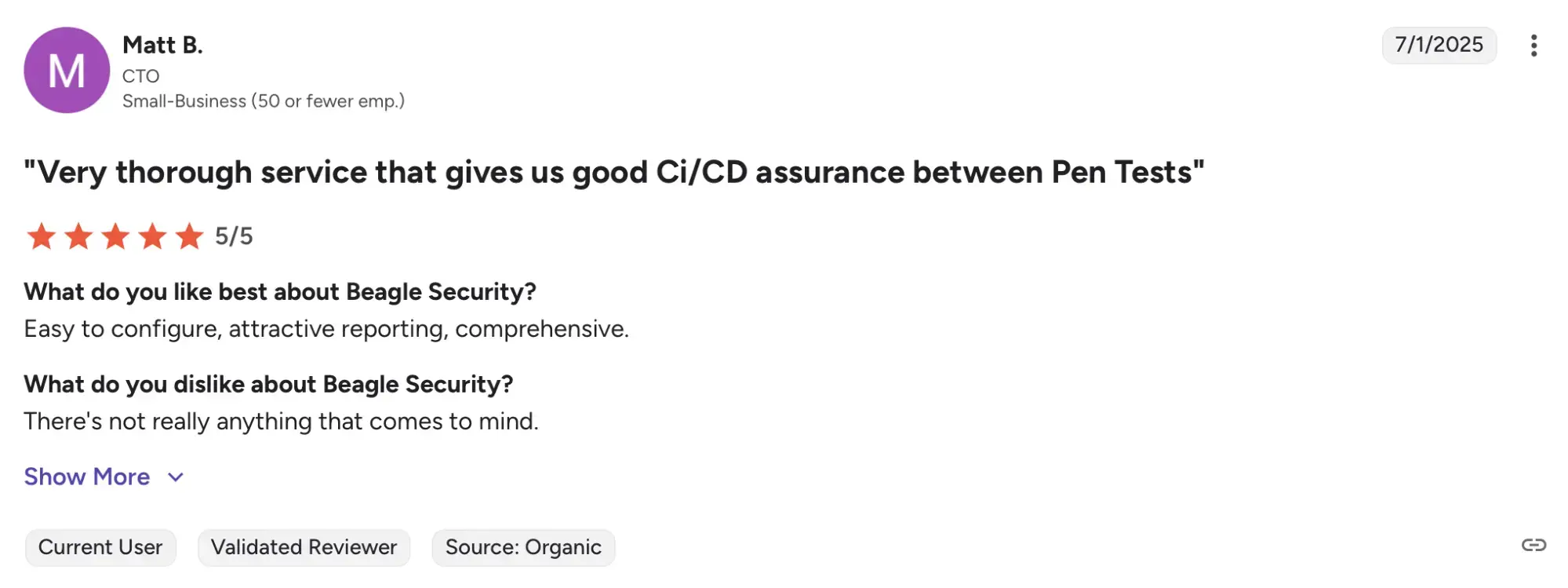
Ratings & reviews
With a total of 87 reviews, Beagle Security has a G2 rating of 4.7/5. Users consistently praise the ease of use and consistent reporting provided, which simplifies the process of identifying and addressing vulnerabilities.
Invicti
Invicti (formerly Netsparker) is an application security testing platform that is well established in the DAST space.
What sets Invicti apart is its proof based approach, where it validates whether they can actually be exploited, thus helping reduce false positives and time consumption.
Key features
- Vulnerability scanning
Scans web apps and APIs to detect security issues quickly and accurately.
- DAST first approach
Focuses on testing applications in runtime, which is where the real attacks happen.
- Proof based scanning
Confirms whether a vulnerability is actually exploitable, helping cut down false positives.
Pricing
Invicti has two pricing tiers, both custom, meaning you have to contact them to get a specific pricing for your organization. The pricing tiers are:
AppSec Core
AppSec Enterprise
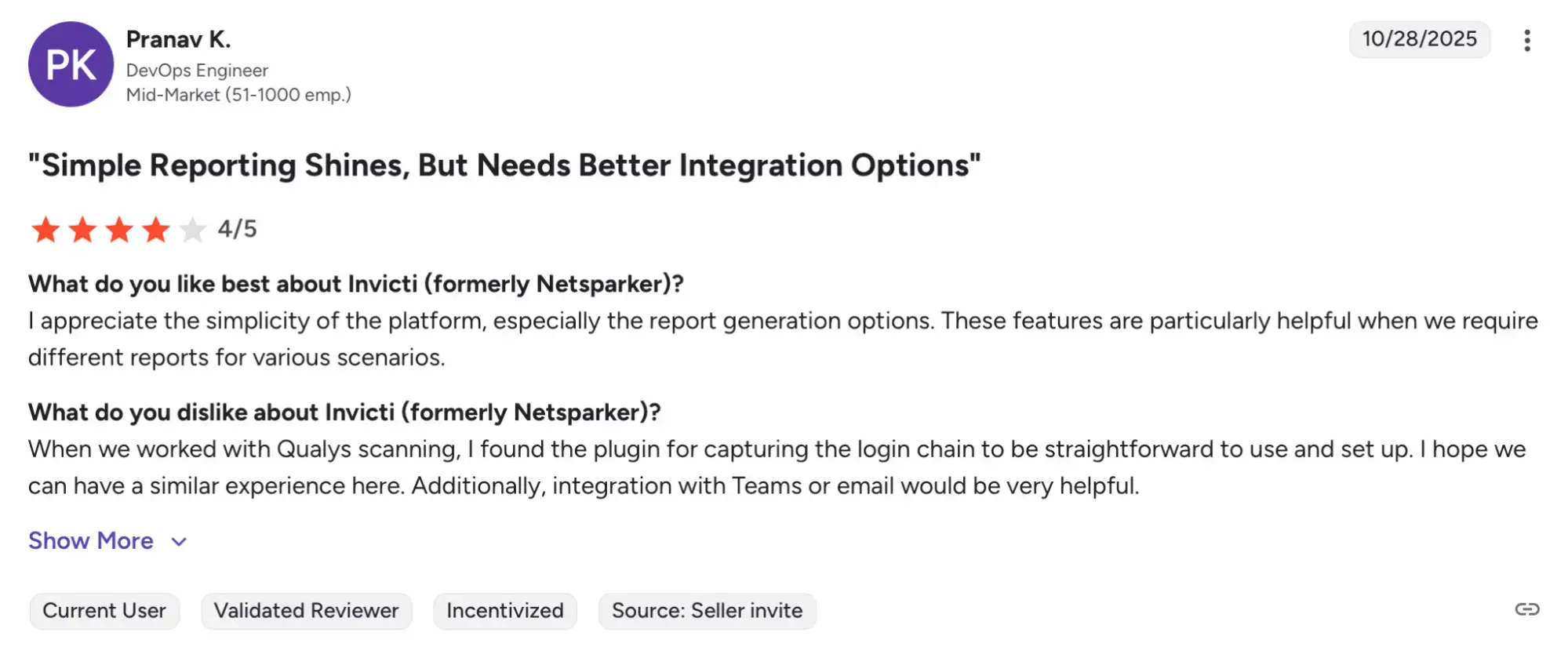
Ratings & reviews
Invicti has a rating of 4.6/5 on G2, based on 68 reviews. Users praise the product for its accuracy and ease of use. However, some users do mention an inferior customer service.
Astrix
Astrix focuses on securing non-human identities (NHI) like API keys, service accounts etc, which often have access to critical systems.
These identities are easy to overlook but can become major security risks if left unmanaged. Astrix helps teams discover and secure every NHIs and AIs allowing organizations to adopt AI securely and at scale.
Key features
- Non-human identity discovery
Identifies service accounts, API keys and integrations across systems.
- AI agent security
Specifically can discover and secure generative AI agents like ChatGPT.
- Tackle agentic risk at the source
Focuses on securing identities early to prevent issues before they spread.
Pricing
Astrix does not have their pricing tiers listed, so contact them to find out more.
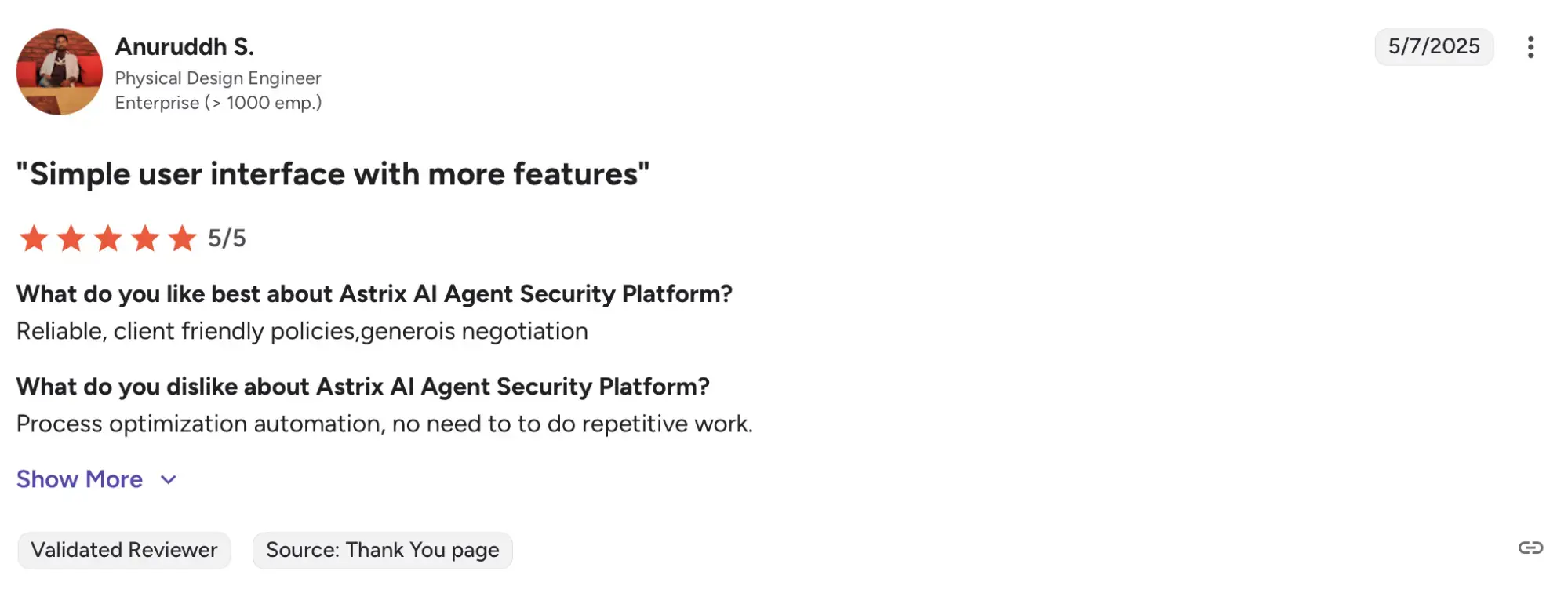
Ratings & reviews
Astrix has just 1 review on G2, with a rating of 5/5. The user identifies reliability and client friendly policies as major pros with a slight disadvantage in process optimization automation.
Synk
Snyk has built a strong reputation as a developer-first security solution. It provides coverage across static application security testing (SAST), software composition analysis (SCA), container security, infrastructure as code (IaC) scanning, and more recently, API and web application testing through its DAST capabilities.
Key features
- Developer first integrations
Works inside IDEs and CI/CD pipelines so security runs where developers already work.
- Open source vulnerability scanning (Synk Open Source)
Detects vulnerabilities early and throughout the development cycle.
- Risk based prioritization
Focuses on risks that actually matter and is the most exploitable.
Pricing
Free plan: For small teams and developers.
Team: Starting at $25/month, aimed for development teams.
Ignite: From $1,260/year, aimed for organizations with less than 50 developers.
Enterprise: Custom priced plan for large organizations. Contact Synk directly for more.
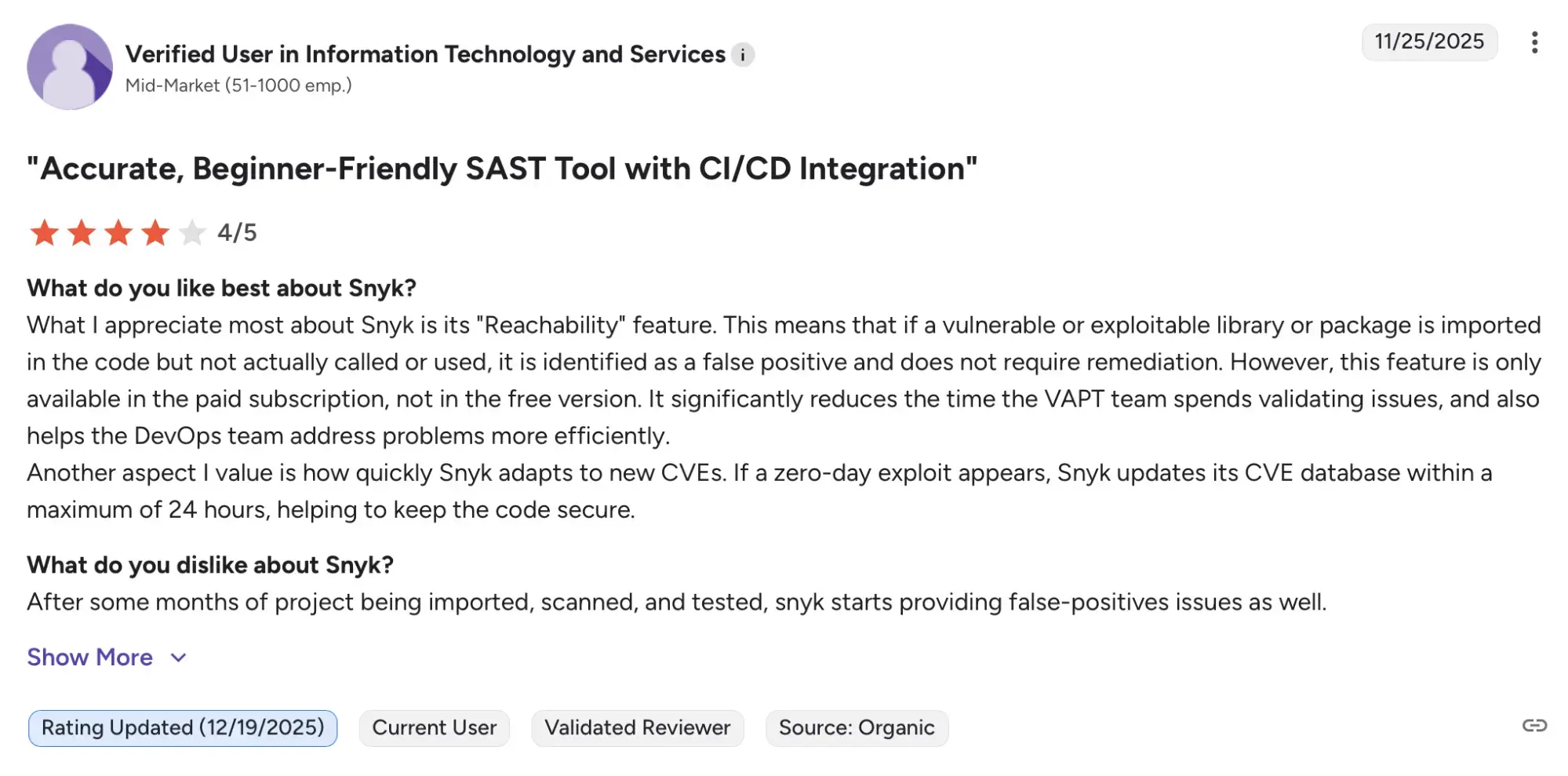
Ratings & reviews
Synk has a rating of 4.5/5 based on 127 reviews on G2. Users praise Synk for seamless integrations with CI/CD pipelines, with some noting a frequent occurrence of false positives.
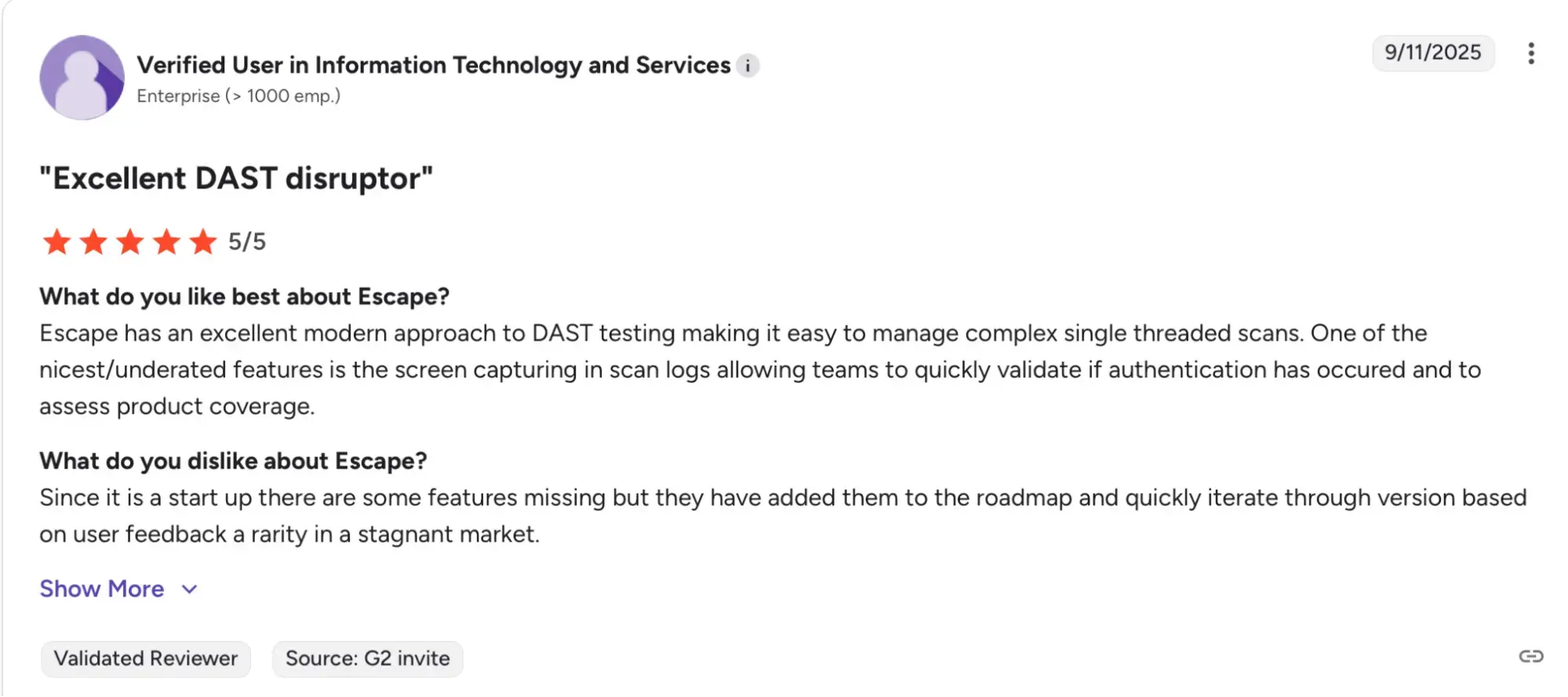
Escape
Escape is an application security platform focused on securing modern applications, with a strong emphasis on APIs and business logic vulnerabilities.
It helps teams discover, test and protect applications, APIs using automated AI pentesting and attack surface management.
Key features
- Business logic-aware DAST
AI powered DAST that easily integrates with modern applications, finds complex issues and helps with remediation.
- AI pentesting
Runs continuous AI powered pentesting assessments with proofs.
- Attack surface management
Discovers and validates exposed applications, APIs and infrastructures.
Pricing
Pricing is not publicly listed, so contact the vendor for more details.
Ratings & reviews
With a rating of 5/5 on G2 based on 9 reviews, users highlight ease of use and scanning technology as major wins, though limited features is a major con reported.
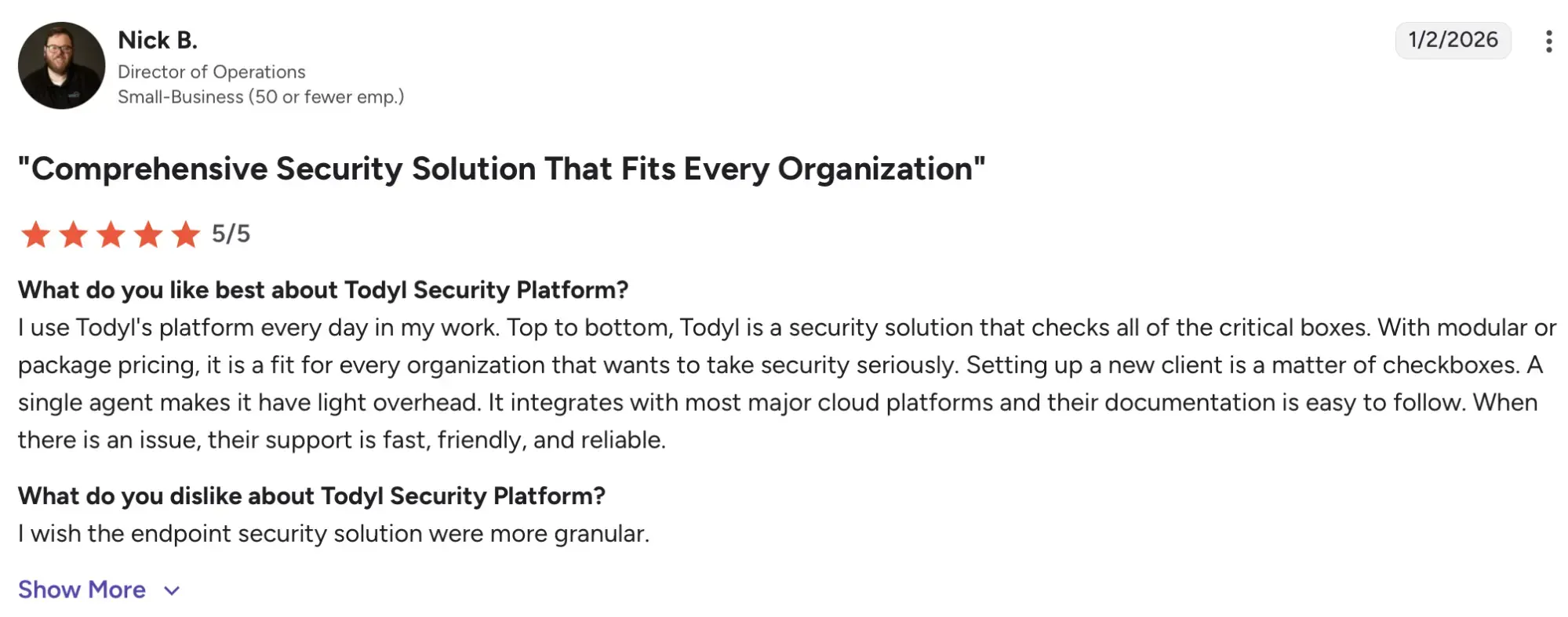
Todyl
Todyl is a company that provides unified cybersecurity solutions to help managed service providers (MSPs), IT, and security professionals protect against threats, manage risks, and ensure compliance.
With 24x7 expertise and top-notch support, Todyl offers a seamless and user-friendly platform that integrates SASE, EDR/NGAV, SIEM, MXDR, SOAR, and GRC into a single, cloud-native solution. This approach enables businesses to quickly gain security and compliance benefits.
Key features
- Managed SIEM services
Collects and correlates data across the network to detect threats and support investigation and compliance reporting.
- Endpoint security
Combines prevention, detection and response in a single agent to stop malware, ransomware and advanced threats.
- Governance, risk and compliance (GRC)
Helps track risk, map controls to frameworks and manage compliance with centralized policies and reporting.
Pricing
There are three tiers of pricing in Todyl. However, the pricing is custom, so contact the vendor directly to get a specialized pricing for your needs. The three tiers are:
Essentials: Best for small businesses building comprehensive security.
Advanced: Best for businesses with 1 or 2 locations with growing security needs.
Complete: Best for highly regulated industries and multi location businesses requiring audit readiness.
Ratings & reviews
With a 4.6/5 G2 rating based on 96 reviews, Todyl receives praise for its comprehensive support and features, with a slight drawback in complexity in its initial setup.
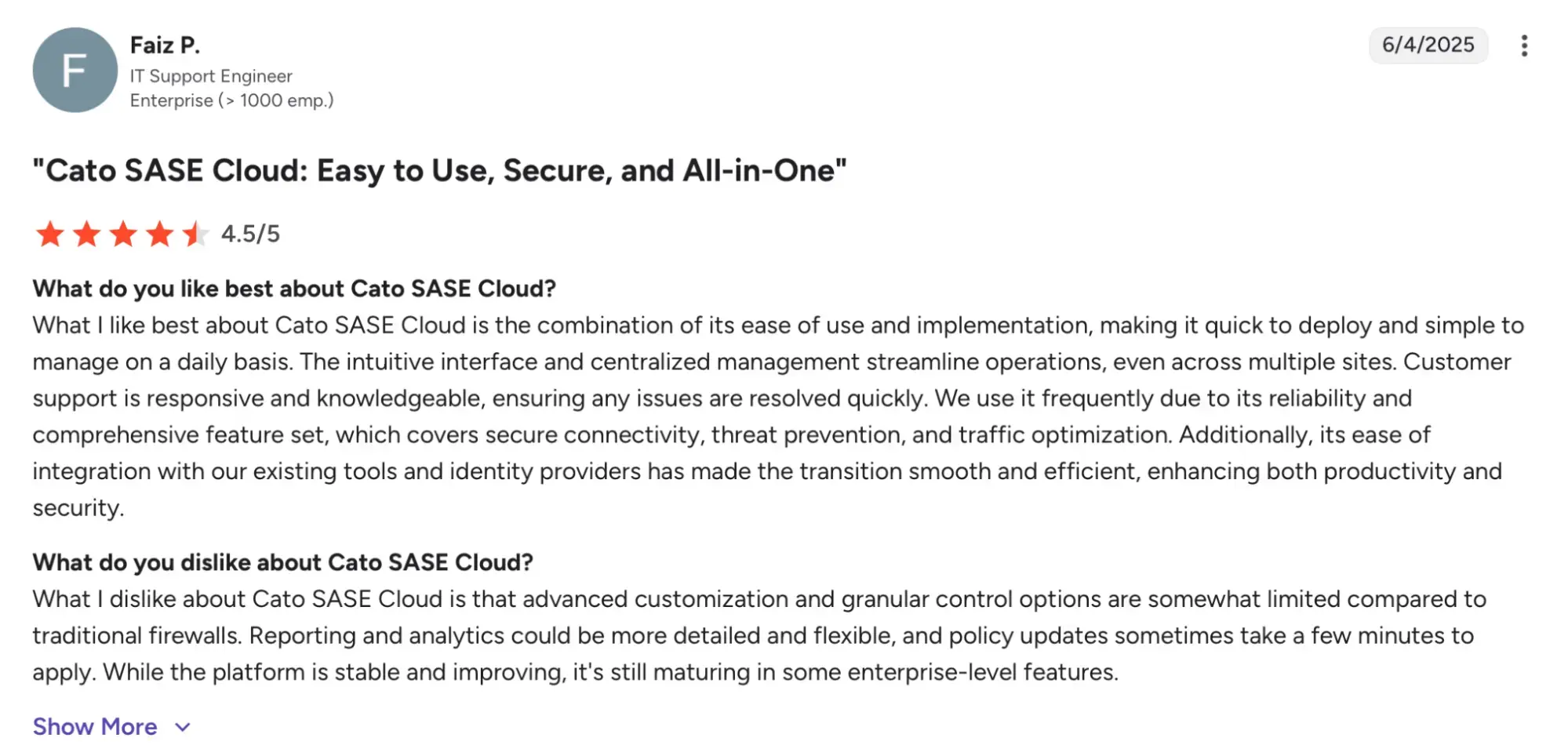
Cato Networks
Cato Networks provides a cloud native platform that combines networking and security into a single service.
It is built around the SASE model and connects users, offices, cloud environments and applications through one global network while applying security controls consistently across all traffic.
Key features
- AI security
Secured AI usage across users and applications by controlling access, preventing data leakage and blocking threats.
- Detection & response
Helps identify threats in a massive data lake, and surface them in a manageable way for analysis and resolution.
- Cloud access security broker
Allows you to check each cloud app for risks and set detailed access rules to give only the necessary permissions and reduce exposure.
Pricing
There is no available pricing on the website, contact the vendor directly for more information.
Ratings & reviews
Based on 82 reviews, Cato Networks has a G2 rating of 4.5/5. Users highlight centralized management and reliability as major highlights though some note advanced customization to be an issue.
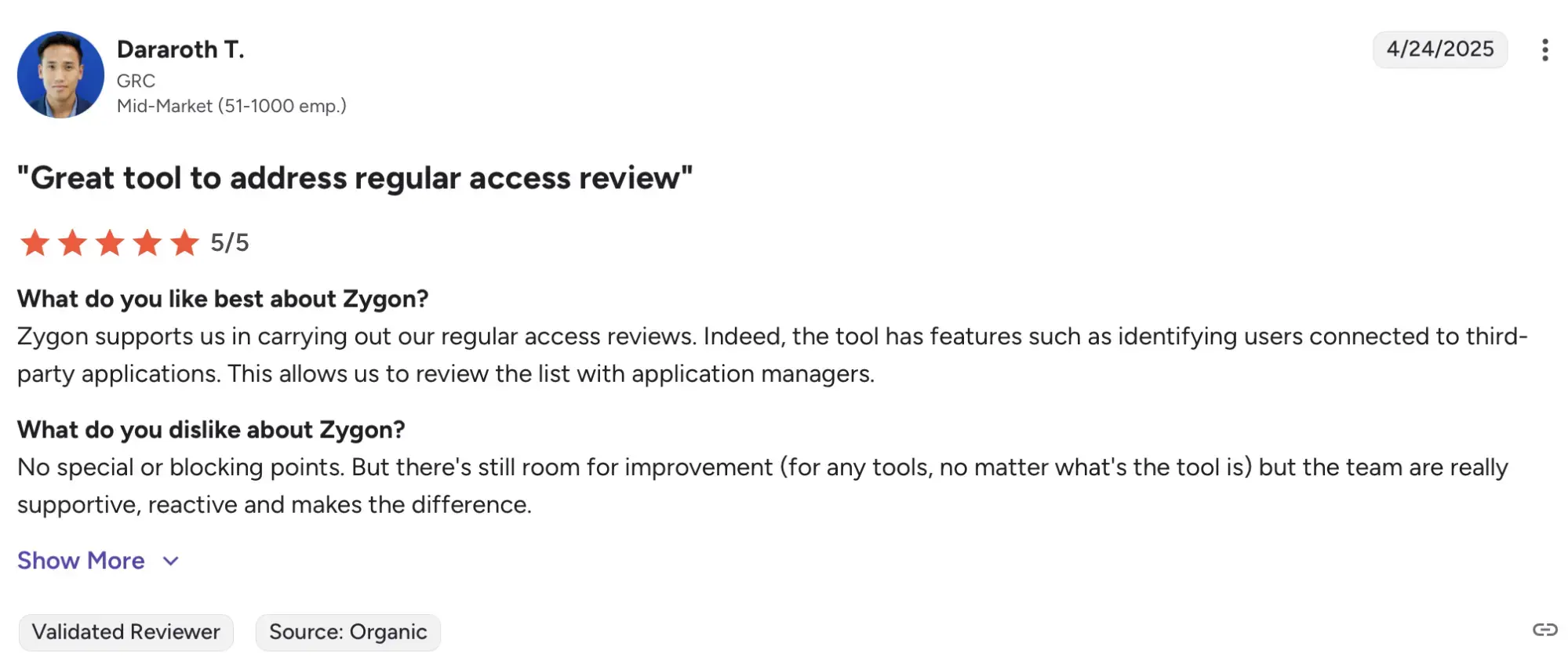
Zygon
Zygon is a modern identity governance platform built to help IT and security teams manage and secure access across all SaaS applications.
Key features
- Workflows & automation
Automates access control actions across apps and identities.
- Collaboration for identity security
Enables IT teams, app owners and end users to work together on access reviews, tasks and remediation.
- Browser extension copilot
Manages and automates user access directly within applications without switching between tools.
Pricing
Zygon has 3 pricing tiers
SaaS Management: $3 per user per month, billed annually.
Modern Identity Governance: $ 6 per user per month, for up to 1,000 users, billed annually.
Enterprise IGA: Custom pricing, for more than 1,000 users.
Ratings & reviews
Zygon has a rating of 4.9/5, based on 46 reviews. Users highlight the platform’s powerful detection and tracking. However, limited automation seems to be a frequent con.
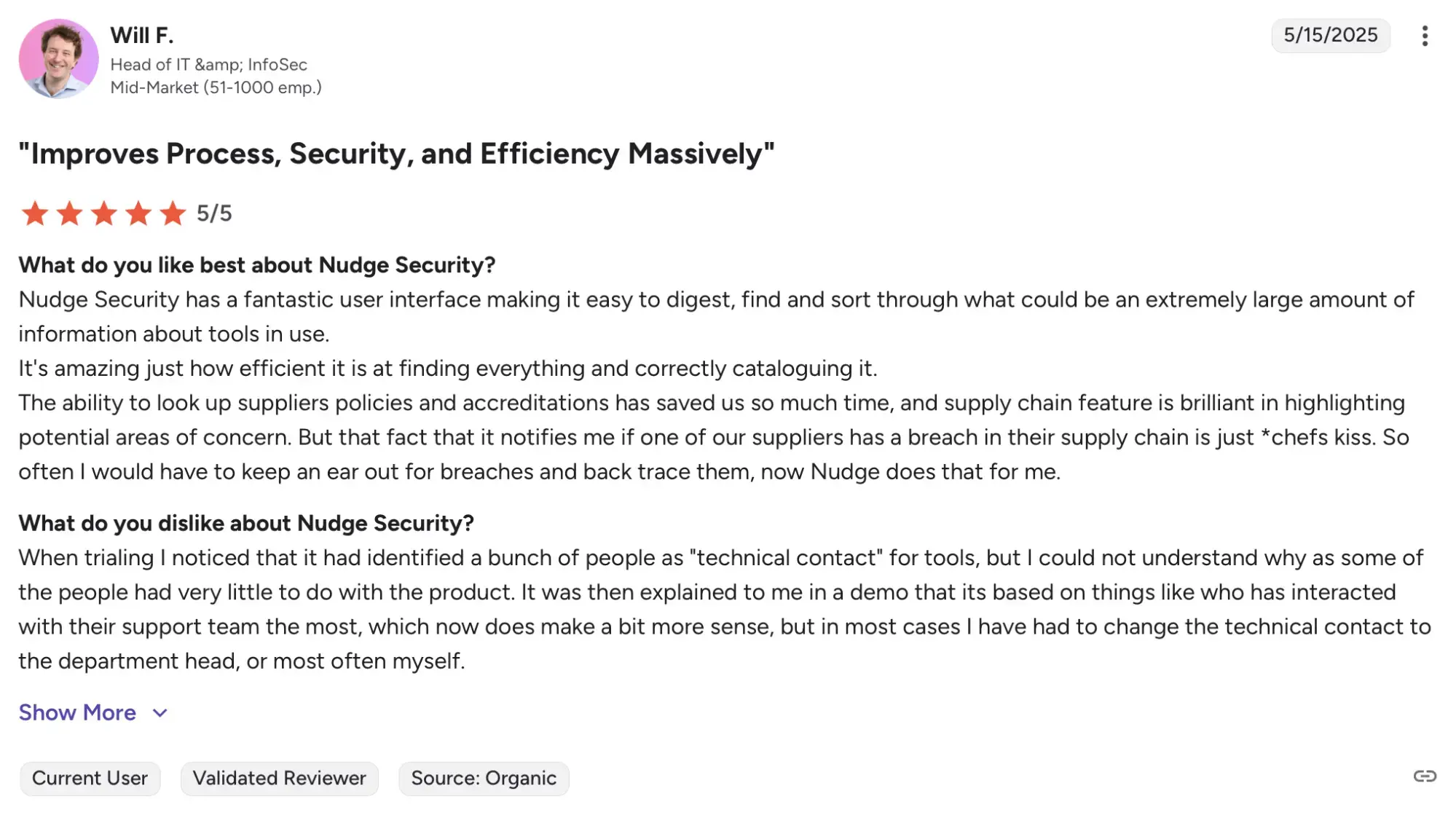
Nudge Security
Nudge Security is a SaaS security platform designed to give organizations full visibility into all the apps and accounts being used.
The platform has a proven track record of users getting complete visibility into their SaaS footprint.
Key features
- Security nudges
Uses just in time prompts to guide employees toward safer SaaS usage and enforce security policies without blocking productivity.
- Workflow automation
Automates common SaaS security tasks using predefined workflows.
- SaaS & AI discovery
Continuously detects and inventories all SaaS apps, accounts and integrations.
Pricing
Nudge Security has an all in one platform pricing of $5 per active user per month for teams with 150 - 2,500 accounts.
For teams with less than 140 users, the price is a $750 flat monthly fee.
For teams with more than 2,500 users, contact the vendor directly for a custom price.
Ratings & reviews
Nudge Security has a rating of 4.7/5 based on 8 reviews on G2. Deployment ease and reliability are major highlights users have liked and access control being a top limitation.
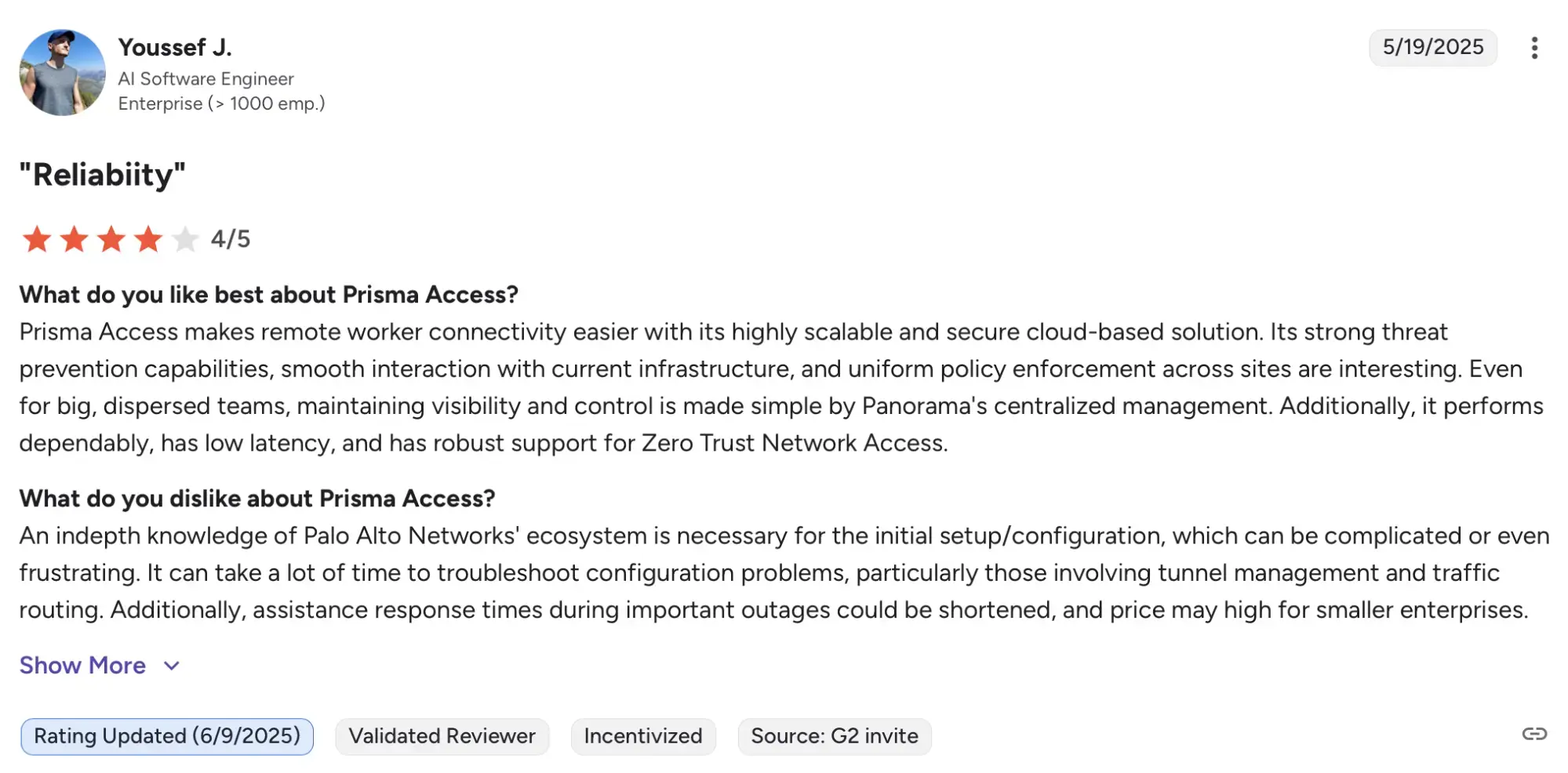
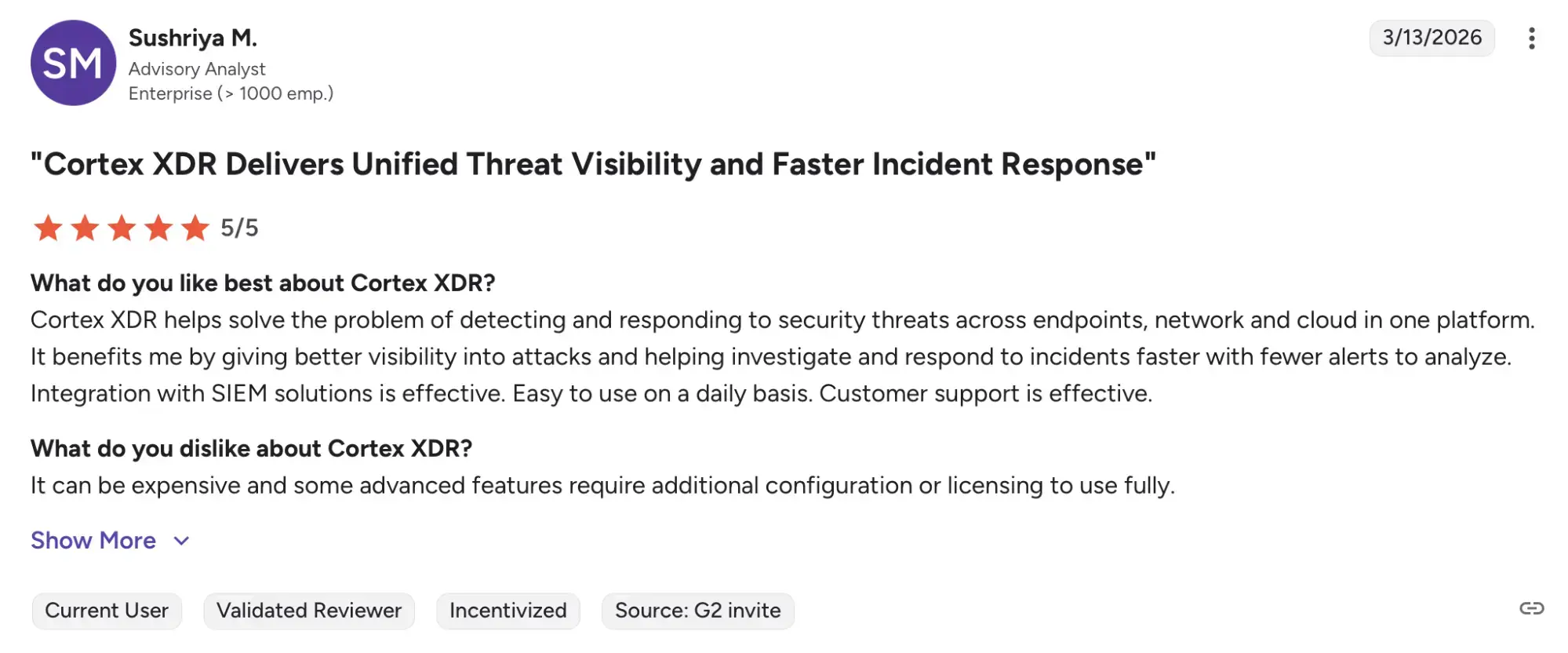
Palo Alto Networks
Palo Alto Networks is a cybersecurity company that provinces a wide range of security applications across cloud, network and applications.
Its main platforms are designed to secure users, applications and infrastructure across cloud and enterprise environments.
Key features
- Cloud security via Prisma Cloud
Prioritizes and eliminates risk, API visibility and protects the entire cloud stack.
- Detection and response via Cortex XDR
Connects data across endpoints and network, proactively hunt, monitor and remediate attacks in real time.
- Secure access via Prisma Access
Helps to achieve true Zero Trust Security for the entire network, protection and safe access to the web.
Pricing
There is no publicly available pricing. Contact the vendor for more details.
Ratings & reviews
Palo Alto Networks offers many products each with their own ratings. Prisma Access has a G2 rating of 4.3/5 based on 73 reviews. Cortex XDR has a G2 rating of 4.6/5 based on 51 reviews.
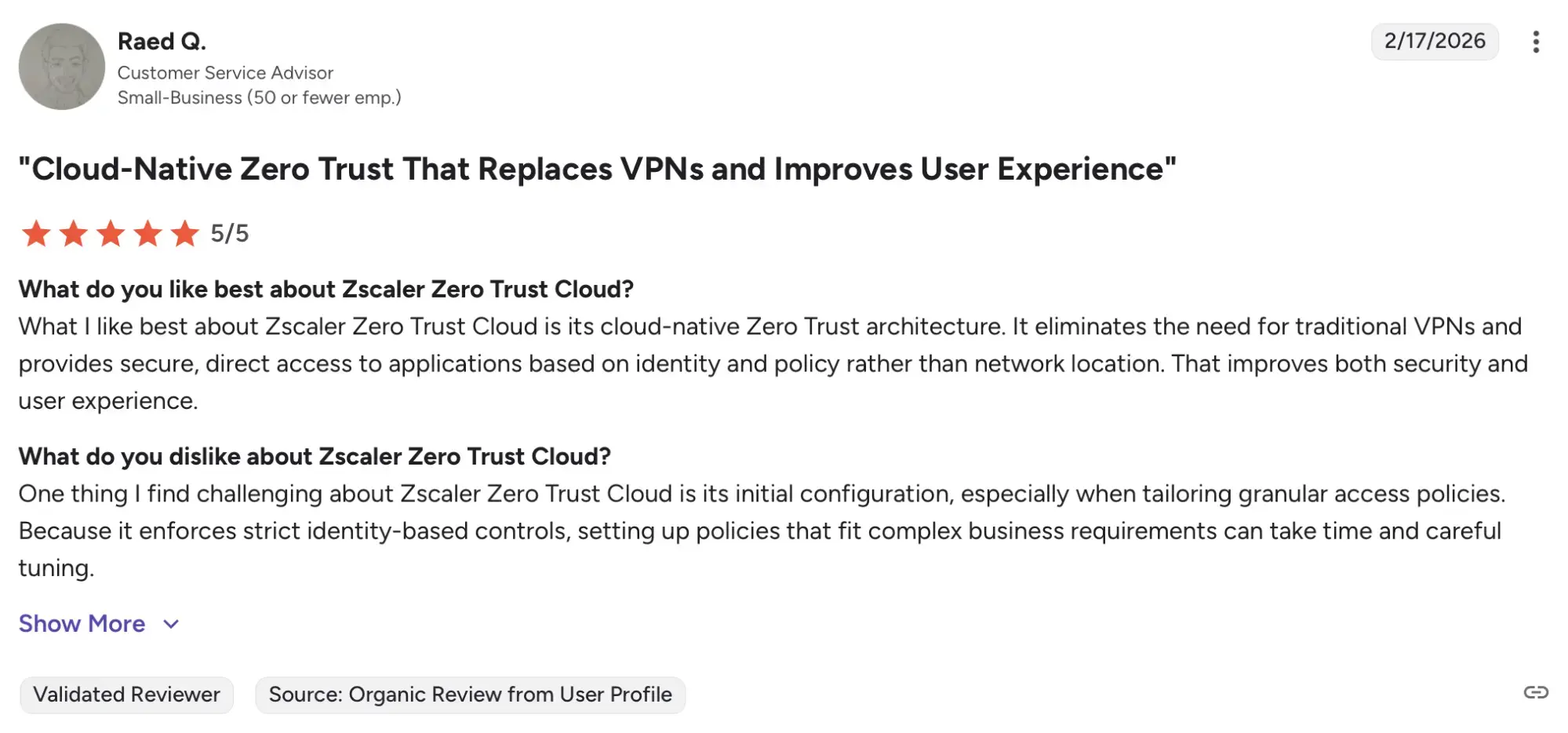
Zscaler
Zscaler is a platform that is designed to securely connect users, applications and devices. Their goals are to improve cyberthreat protection, lay a strong base of IoT adoption and provide secure connectivity to the entire workforce and locations.
Key features
- Unify security and network access
It creates a single-vendor SASE framework using a straightforward, proxy-based design.
- Extend zero trust beyond workforces
It enforces zero trust security for IoT/OT devices, servers and guests in branches.
- Reduce cost and complexity
It removes the need for multiple security point products by unifying security with zero trust.
Pricing
There are two pricing tiers:
Essentials Platform
Zscalar Platform
There is no pricing listed, so contact the vendor for more details.
Ratings & reviews
Based on 42 users, Zscaler has a G2 rating of 4.6/5. Threat detection and robust security are major highlights according to the users, with some noting dependency on internet connectivity to be a slight flaw.
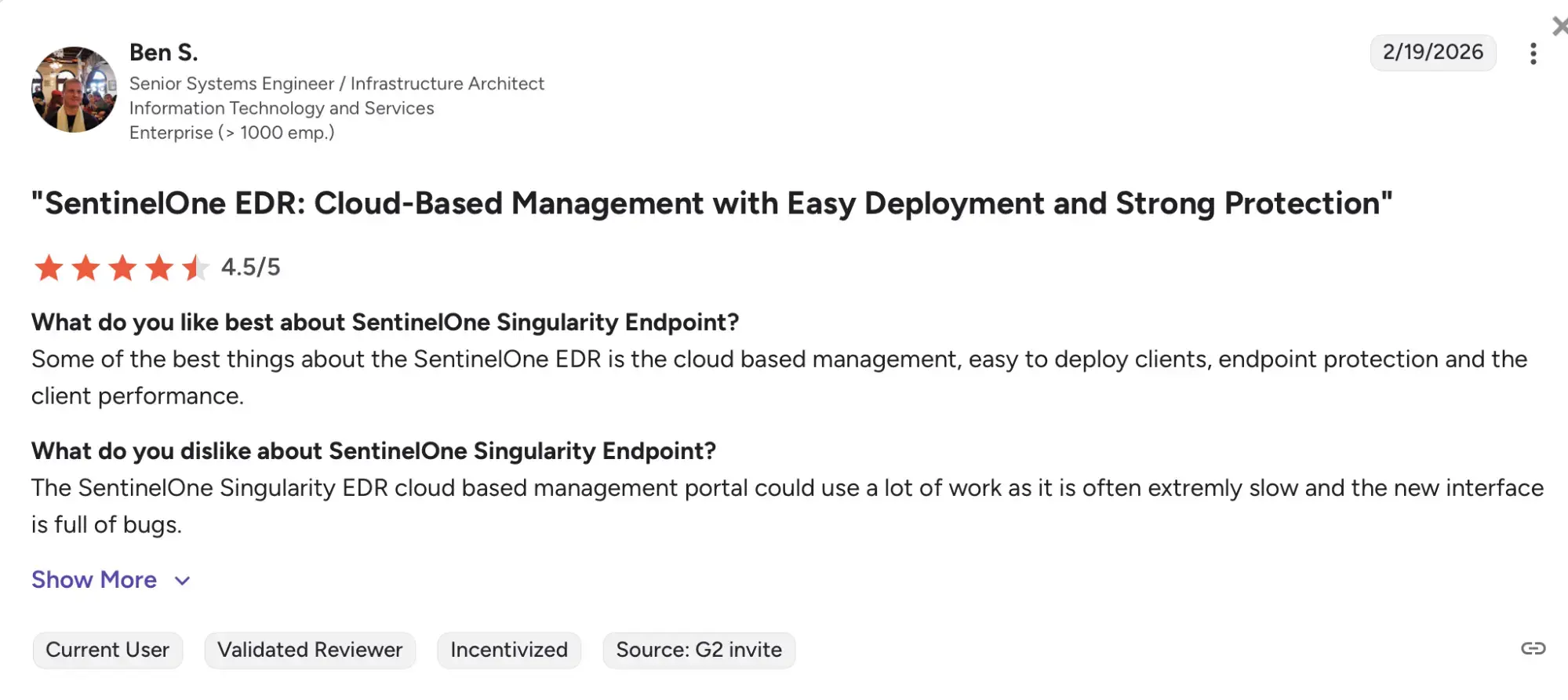
SentinelOne
SentinelOne is an AI native cybersecurity platform. Their mission is to provide intelligent, unified and continuous security solutions, with an emphasis on human leadership combined with AI technology, which enables defenders to act swiftly and maintain an edge.
Key features
- AI-Powered Autonomous Agent
Agents run locally to detect and remediate threats in real-time without relying on cloud connectivity, ideal for air-gapped or remote devices.
- Cloud security posture management
SentinelOne can protect your cloud environment by using Cloud Security Posture Management (CSPM) within the SentinelOne Cloud Security (CNAPP) solution.
- Cloud native security
Eliminates false positives and takes fast action on alerts that matter.
Pricing
SentinelOne has three pricing tiers
Singularity Complete: For growing, collaborative teams, this plan costs $179.99 per endpoint per month.
Singularity Commercial: $229.99 per endpoint per month. Targeted for teams who need more advanced security.
Singularity Enterprise: For global organizations, this pricing is custom. Contact the vendor for more details.
Ratings & reviews
Based on 356 reviews, SentinelOne as a whole, has a G2 rating of 4.7/5.
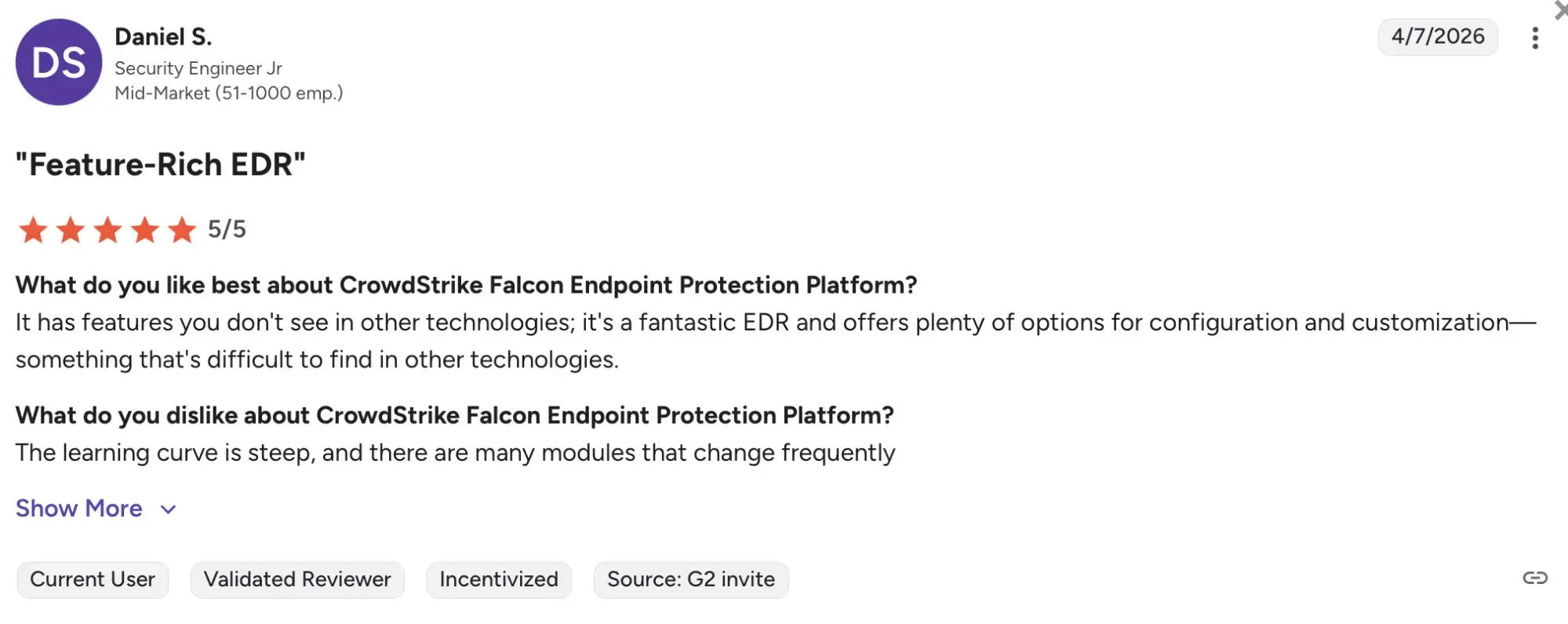
CrowdStrike
CrowdStrike is a global cybersecurity leader known for its Falcon platform, a cloud native security solution that protects endpoints, cloud workloads and data, built to stop breaches.
Key features
- Endpoint security
Provides AI powered protection, detection and response.
- Exposure management
Helps to gain full visibility and AI powered prioritization to stop breaches before they start.
- Threat intelligence & hunting
Helps to disrupt adversaries with an AI powered unified intelligence and hunting team.
Pricing
CrowdStrike has 3 paid pricing tiers, with 1 free trial.
Falcon Free Trial: A free trial plan valid for 15 days.
Falcon Go: $59.99 per device, billed annually.
Falcon Pro: $99.99 per device, billed annually.
Falcon Enterprise: $184.99 per device, billed annually.
Ratings & reviews
CrowdStrike products have a rating of 4.6/5 on G2, based on 584 reviews.
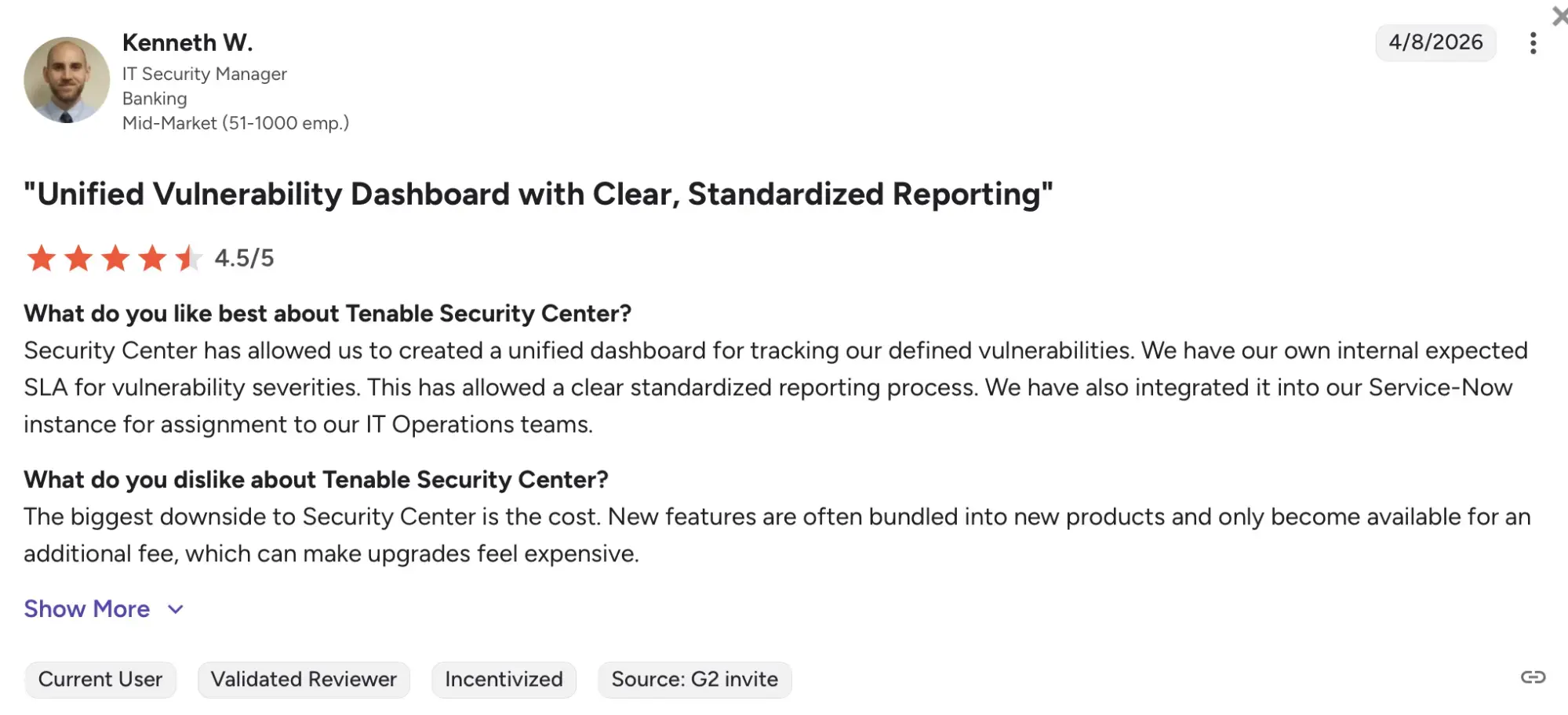
Tenable
Tenable is best known for its exposure management platform, helping organizations identify, prioritize and fix security issues across their entire attack surface.
Key features
- Exposure management
From the flagship Tenable One Exposure Management Platform, it unifies data from disparate tools and combines AI with technical and business context to uncover an organization’s highest-risk exposures.
- Threat investigation
The platform helps accelerate cyber threat investigations with risk context.
- Security hygiene
Helps identify toxic risk combinations and eliminates common hygiene issues like open ports or lack of multifactor authentication.
Pricing
Tenable Nessus Professional: $5,652.20 for 1 year license.
Tenable Nessus Expert: $8,012.20 for 1 year license.
Tenable Vulnerability Management: $6,112.40 for 1 year subscription, for 100 assets (can purchase protection up to 250 assets, for more, contact the vendor).
Tenable Web App Scanning: $7,434 for 1 year subscription.
Ratings & reviews
Based on 563 reviews, Tenable product catalogue has a total rating of 4.5/5 on G2.
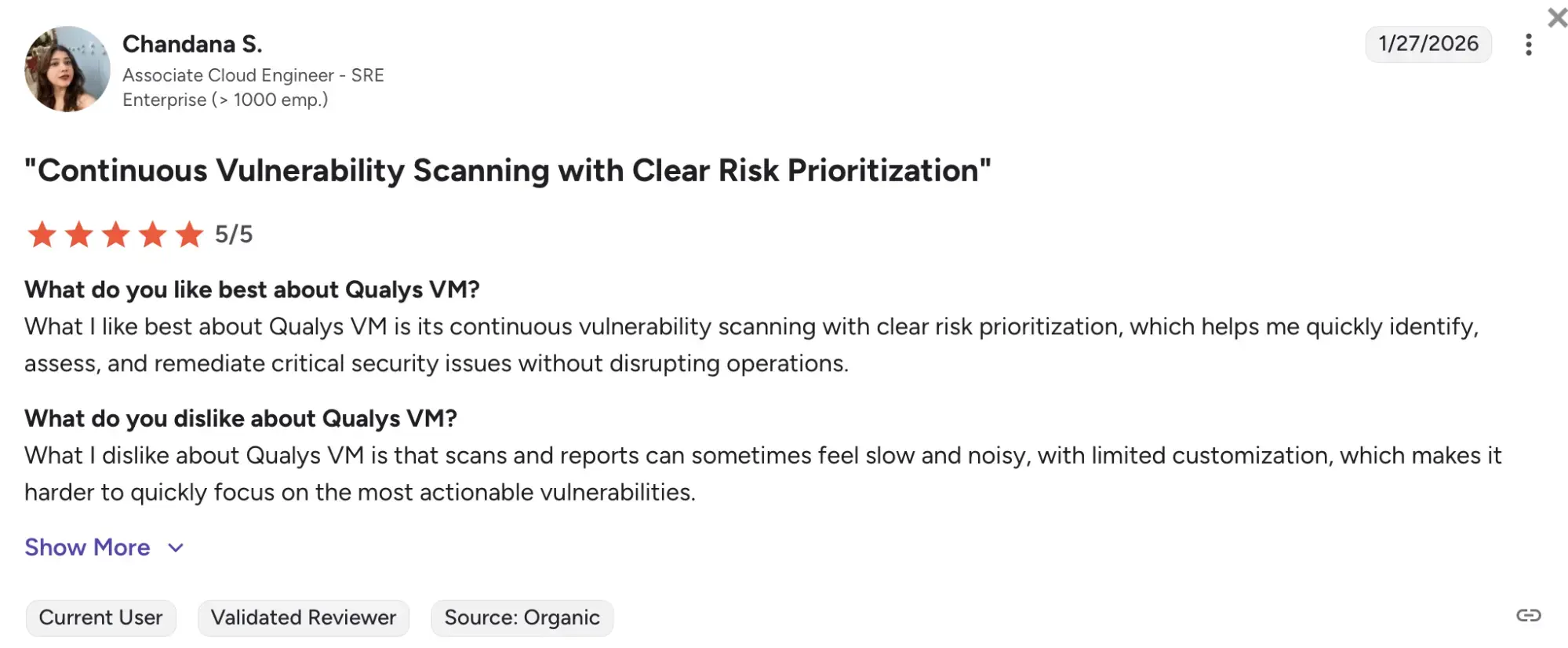
Qualys
Qualys is one of the first SaaS security companies in the world. With more than 25 years of experience in the cybersecurity market, Qualys focuses on helping organizations identify, access and reduce cyber risk across the entire environment.
Key features
- Vulnerability and configuration management
With their TotalAppSec platform, Qualys provides comprehensive protection for modern web applications and APIs.
- Risk remediation
With TruRisk Eliminate, Qualys offers a comprehensive risk reduction solution with patch management, mitigation and isolated options to address nearly 100% of CISA KEVs and ransomware vulnerabilities.
- Compliance
Qualys’ Executive Audit Readiness Report pinpoints gaps and delivers prescriptive insights to strengthen compliance and improve audit outcomes.
Pricing
Pricing is custom and depends on cloud platform apps, the number of network addresses, web applications, and user licenses. Contact the vendor for more details.
Ratings & reviews
Across its products, Qualys has a G2 rating of 4.3/5, based on 257 reviews.
Final thoughts
SaaS security isn’t a ‘pick one tool and chill’ kind of problem.
It’s layers. Apps, clouds, users, access; everything is connected and everything is exposed. So most teams end up stacking tools.
But the smarter move? Start with something that actually fits into your workflow.
That’s where Beagle Security stands out: helping you test continuously, catch issues, and fix them before they turn into something bigger.
Because at the end of the day, good security shouldn’t feel like extra work.
It should just work.
FAQs
What is the difference between AppSec, SSPM and SASE?
AppSec focuses on securing the application itself, SSPM manages how SaaS tools are configured and accessed, and SASE secures how users connect to applications.
What are the biggest security risks in SaaS applications?
Common risks include insecure APIs, weak authentication, misconfigurations, excessive permissions and unmonitored third party integrations.
What should you look for in a SaaS security company?
Look for tools that fit your workflow, provide clear visibility, reduce noise and help prioritize real risks.
Which SaaS security tool is the best?
There is no single ‘best’ tool. The right choice depends on your architecture, team and what you’re trying to secure.










