
When it comes to improving your application’s security posture, it is deemed effective when you’re taking essential measures to safeguard your customer-facing external assets as well as your internal assets.
Many companies underestimate the risks associated with internal applications and ultimately end up having to pay a hefty price for it. Conducting regular vulnerability assessments should be at the centre of your efforts for establishing a robust cyber defense program.
Why do you need penetration testing for your internal apps?
Big companies tend to have a lot of internal web applications residing in their private network for a wide range of internal tasks. These applications are typically used by only the company employees and have very little to no security in place to fend off any cyber-attack.
Attackers could reach these internal systems without much trouble. This could be through an email with a malicious attachment sent to one of your employees, for example. If the internal applications do not have any sort of hardening in place, it makes it easy for an attacker to initiate chain attacks after gaining an initial foothold.
Organizations often forget the threat insiders pose as well. Authenticated tests against privileged user roles can give you a complete picture of how dangerous a regular insider can be with the sort of information available for them.
Finding out the known and unknown vulnerabilities of internal apps through a penetration test can help you to significantly reduce risks and improve the security posture of these applications. Moreover, certain compliance standards require you to submit audit reports for internal application scans.
And to empower you to achieve it in an easy, fast and economical way, we’re introducing Beagle Security Cosmog.
What is Beagle Security Cosmog?
Beagle Security Cosmog allows organizations to run automated penetration tests for web applications in their internal private network without having to expose them on the internet.
This is helpful if you have internal applications that are not being pentested regularly or are currently having test/pre-release environments exposed to the internet.
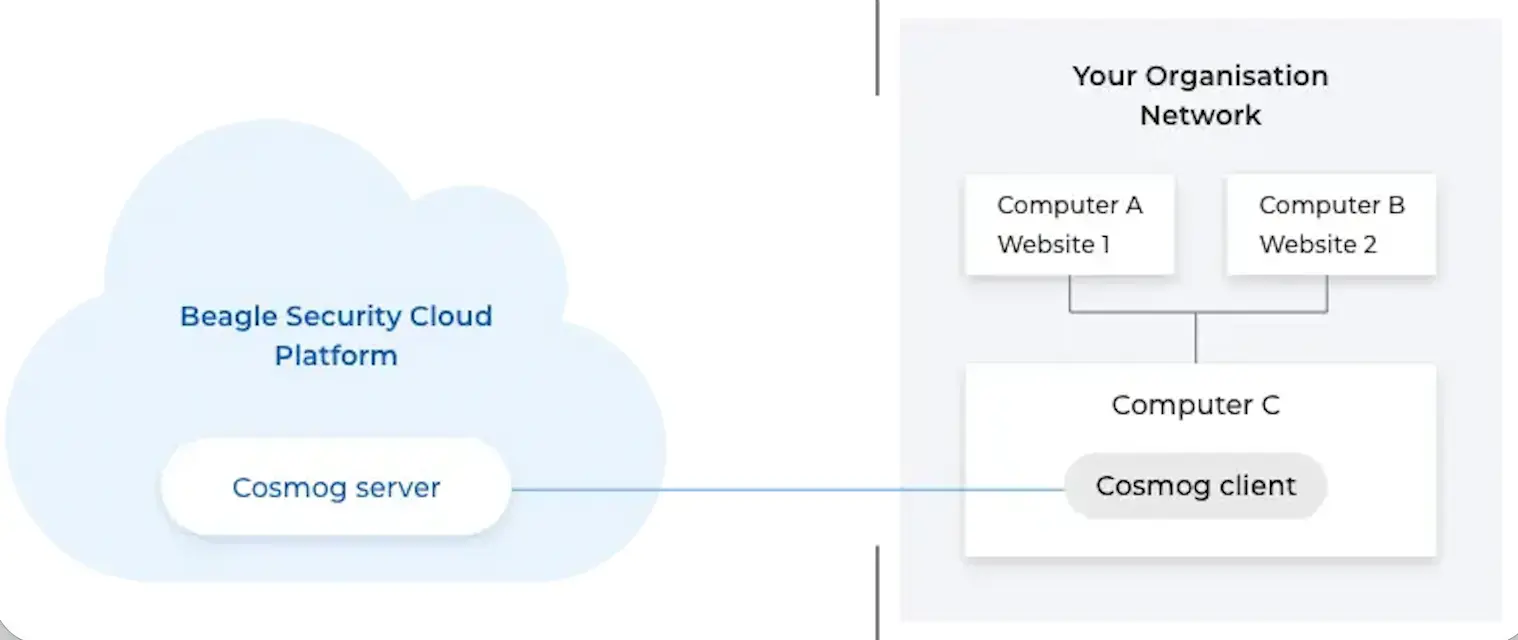
In terms of setup, all you have to do is install an on-prem Cosmog client in a host machine inside your internal network. The client will connect with the Cosmog server to create a secure tunnel between the Beagle Security Cloud Platform and your organization’s network.
A single installation is necessary to run penetration tests for all the applications in your private network. Once you start a penetration test, the Cosmog server will be ready to accept the connection from the Cosmog client. Starting the Cosmog client will establish a secure channel between Beagle Security and your network. This ensures that all traffic for the penetration test is end-to-end encrypted.
How does Beagle Security Cosmog installation work?
Cosmog allows you to securely test applications inside your internal network without exposing them to the internet.
Before you begin, choose the right setup:
Standard platforms → If your application runs on VMs, bare metal, or non-Kubernetes environments.
Kubernetes → If your application runs inside a Kubernetes cluster
Step 1: Create a Cosmog profile
You can create a Cosmog profile from the Tunneling section in your dashboard.
Click Tunneling in the application dashboard.
This opens the Cosmog configuration panel.
Click Create new profile.
Select the setup type. (Standard platforms or Kubernetes)
- Enter:
- Bridge IP address
- Test IP range
- Click Save.
Step 2: Install the Cosmog client
Open your Cosmog profile.
Click Install.
- In the pop-up:
- Select your platform.
- Select the installation type.
Copy the installation command
Run the command on your host machine (or Kubernetes environment).
This command will run the Cosmog client while also setting up a secure tunnel to Beagle Security.
Once the client installation is complete, you’re good to add your web applications and start the penetration test.
Wrapping up
Beagle Security Cosmog allows you to improve the security posture of applications in your private network efficiently without having to do complex on-prem installations, pay a hefty fee or waste your valuable time waiting for updates or maintenance schedules.
The feature is currently available on the enterprise plan. If you’d like to know more about the solution or schedule a demo, please feel free to schedule a time from here.
We’re also happy to answer any questions that you may have about the feature. Simply get in touch with us via live chat and we’ll be happy to help you!
![Top vendor application security tools [2026] Top vendor application security tools [2026]](/blog/images/top-vendor-application-security-testing-tools-2026-cover.webp)








![Top 15 SaaS security companies [2026] Top 15 SaaS security companies [2026]](/blog/images/blog-banner-six-cover.webp)

![Top API security vendors [2026] Top API security vendors [2026]](/blog/images/top-api-security-vendors-cover.webp)